Parents want to stay involved in their child’s education, but outdated communication systems create frustrating barriers. Teachers spend hours on administrative tasks instead of teaching. Meanwhile, parents feel disconnected from daily classroom activities and have trouble addressing concerns before they escalate. Sharing sensitive student information through unsecured channels like personal texts or social media poses serious privacy risks.
A secure parent-teacher communication platform addresses these issues. It offers a dedicated, encrypted space for real-time updates, progress reports, and two-way conversations. This keeps families engaged while protecting student data.
At Intellivon, we have developed secure platforms for large education organizations and district systems, where privacy, uptime, and regulatory checks are crucial. We design these platforms as enterprise systems, and not simple chat tools. They integrate smoothly with SIS, LMS, and identity systems on a large scale. In this blog, we explain how to build a secure parent-teacher communication platform from the ground up.

Key Takeaways of the Parent-Teacher Communication Software Market
The parent–teacher communication software market is entering a high-growth phase, projected to reach USD 2.5 billion by 2025 at a strong 18% CAGR, driven by compliance pressure, digital schooling models, and rising demand for secure family engagement systems.
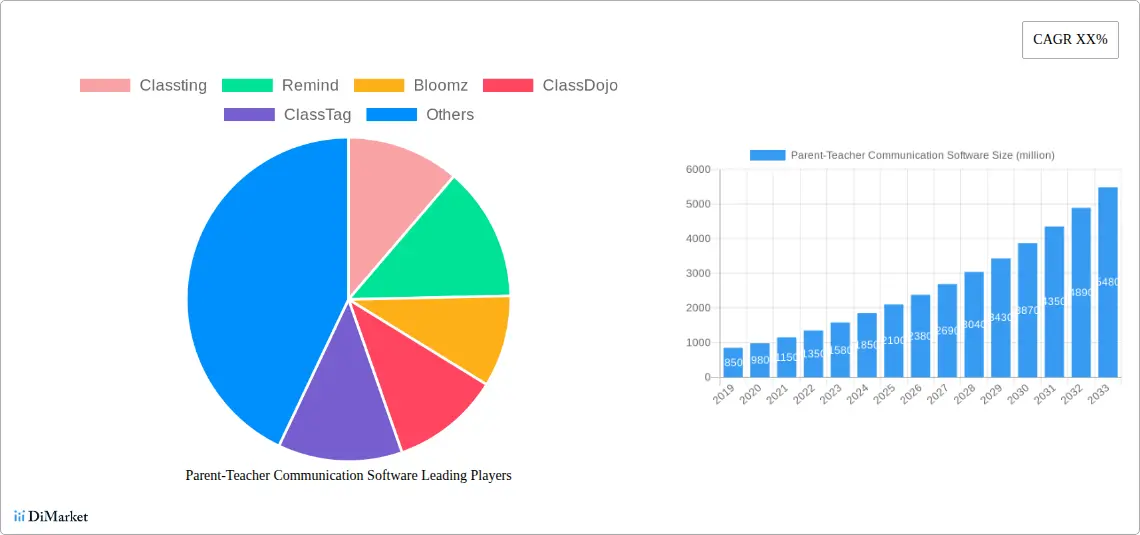
Key Insights:
- Digital transformation across K–12 is replacing emails and paper-based notes with secure, real-time apps for messaging, alerts, attendance, and engagement analytics across hybrid learning environments.
- Government mandates for parental engagement, school safety, and student data privacy under FERPA and COPPA are accelerating institutional adoption, especially in public school systems.
- Asia-Pacific is the fastest-growing region, fueled by smartphone penetration, urbanization, and national digital education programs across India, Southeast Asia, and the Middle East.
- AI-driven features such as real-time translation, personalization, and performance insights are becoming standard, as schools seek unified tools for communication, portfolios, and event management.
- North America holds 38% market share, supported by mature EdTech ecosystems, strict privacy regulations, and large district procurement budgets.
- Schools and institutions contribute over 60% of total revenue, with Android dominating emerging markets and iOS/web platforms leading in developed economies.
- More than 49% of K–12 institutions now use smart digital tools broadly, with parent communication platforms forming a core layer of this stack.
- Post-pandemic procurement remains strong, with public schools driving large-scale adoption through centralized reforms and bulk vendor contracts.
- Platforms such as ParentSquare and ClassDojo report 85%+ engagement gains, alongside measurable reductions in administrative workload.
- AI-backed analytics enable early interventions, helping districts reduce student drop-offs through proactive alerts and data-led decision-making.
- Pilot programs show 15–20% outcome improvements, despite ongoing challenges around privacy enforcement and equitable access.
- Cloud and hybrid deployments with deep LMS and SIS integration present the largest growth opportunity for large, multi-school districts.
As the market scales through regulation, AI adoption, and district-wide digitization, knowing how to create a secure parent–teacher communication platform is no longer a technical exercise. It is now a strategic requirement for any education organization seeking long-term trust, compliance, and operational stability.
What Is a Secure Parent–Teacher Communication Platform?
A secure parent–teacher communication platform is a compliance-ready digital system that enables encrypted messaging, role-based access, secure document sharing, and audit logging between schools and families.
It is designed to meet FERPA and COPPA requirements while supporting district-scale governance, identity control, and real-time school–home communication.
For large school networks, this platform becomes part of the core digital infrastructure. It reduces compliance risk, improves parent engagement, and creates a governed communication environment that scales across schools without exposing student data.
How It Differs From Traditional Communication Apps
Traditional communication tools were built for personal convenience. Secure education platforms are engineered for institutional governance, regulatory oversight, and district-scale risk management.
| Secure Parent–Teacher Platform | Traditional Communication Apps |
| Role-based access tied to school identity | Personal phone numbers and open accounts |
| End-to-end encrypted messaging and storage | Limited or inconsistent encryption |
| FERPA and COPPA-aligned data handling | No built-in education compliance controls |
| Full audit trails and access logs | Little to no audit visibility |
| Centralized district-level governance | Decentralized, user-managed communication |
| Native SIS and LMS integrations | No secure education system integration |
A secure parent–teacher communication platform replaces informal, high-risk messaging with a governed digital infrastructure built for trust, compliance, and district-scale operations. It is no longer a communication upgrade. It is a foundational requirement for modern education systems.
How 96% of School Apps Share Data With Outsiders
Most schools believe that if an app is widely used in classrooms, it must already be safe. In reality, the opposite is often true. A growing body of primary research shows that the majority of education apps quietly transmit student data to third parties, often without meaningful school oversight. This creates hidden exposure across privacy, compliance, and trust.
1. The 96% Data-Sharing Reality Schools Rarely See
A U.S. study supported by the Internet Society Foundation revealed that 96% of educational apps used in schools share children’s personal information with third parties.
More concerning, 78% of that data flows directly to advertisers and analytics firms. These are not fringe apps. Many sit inside daily classroom workflows.
For school leaders, this creates a silent compliance gap. Even well-intended tools can violate district data policies, FERPA controls, and parental consent boundaries without anyone realizing it.
2. Hidden Trackers Across Platforms
Independent privacy researchers and security vendors, including Proton, have found that nearly 90% of EdTech apps and websites contain hidden tracking technologies. These trackers often collect metadata, behavioral patterns, and device identifiers that extend far beyond educational needs.
From an enterprise risk perspective, this means schools are not only managing student data. They are also unknowingly managing third-party surveillance infrastructure inside their digital classrooms.
3. Exposure of Students Outside School Networks
An analysis reported by K-12 industry researchers found that 79% of school-used apps request access to student location, while 52% request access to calendars and contacts. These permissions persist beyond school Wi-Fi, especially under BYOD environments.
This expands exposure from controlled campus networks into homes, buses, and shared family devices. Once permissions are granted, districts lose visibility into how that data is reused or retained.
Regulatory Pressure Is Not Theoretical
Federal education data offices once reported over 1,197 unresolved FERPA complaints in a single review period, later reduced to around 594 after intervention. These were not hypothetical risks. They were filed cases tied to real systems, real vendors, and real student records.
For enterprise administrators, this pattern confirms that compliance enforcement is active, not symbolic.
Communication Structurally Broken
A district communications study from Finalsite found that 40% of school communicators struggle with low family engagement, while 35% report difficulty creating messages that parents actually respond to. When engagement fails, schools compensate with more channels, more tools, and more third-party apps.
This unintentionally multiplies risk while reducing message clarity.
Why This Forces A New Security Standard
These datasets expose a clear pattern. Schools depend on digital communication at a massive scale, yet most existing tools operate on data-hungry consumer architectures. Trackers, advertisers, ungoverned permissions, and unmanaged integrations dominate the ecosystem.
A secure parent–teacher communication platform must therefore be built on zero-tracker architecture, strict vendor isolation, encrypted data flows, and auditable access governance. Anything less simply relocates today’s risks into a larger digital footprint.
Mandatory Compliance Standards for Parent–Teacher Platforms
Parent–teacher communication platforms must comply with FERPA, COPPA, GDPR-K, and district vendor-governance policies. These standards regulate student data access, parental consent, encryption, audit logging, and third-party data sharing across school communication systems.
1. FERPA (Family Educational Rights and Privacy Act)
FERPA governs how U.S. schools collect, store, and share student education records. It gives parents legal rights over access, corrections, and disclosure of their child’s educational data.
For communication platforms, FERPA directly impacts message storage, record retention, access control, and audit logging. Any system that allows unauthorized viewing of grades, behavior records, or disciplinary communication creates immediate legal exposure.
COPPA (Children’s Online Privacy Protection Act)
COPPA regulates how digital platforms collect and use data from children under 13. It requires verifiable parental consent, strict data minimization, and transparent data usage policies.
In a parent–teacher communication platform, COPPA shapes identity workflows, consent management, analytics configuration, and third-party integrations. Schools cannot rely on vendor assurances alone. The technical architecture must enforce these protections automatically.
3. GDPR-K and Global Student Data Privacy Laws
GDPR and its child-data adaptations extend privacy requirements across consent, data residency, breach reporting, and the right to erasure. Similar student privacy laws now exist across the UK, Canada, Australia, and parts of Asia.
For multinational education groups and international schools, this means communication platforms must support lawful data processing, region-specific storage controls, and formal breach notification workflows.
4. District Vendor-Governance Requirements
Beyond statutory law, most school districts impose their own vendor-governance frameworks. These include mandatory security reviews, data-processing agreements, penetration testing requirements, incident-response obligations, and termination clauses tied to data handling.
A parent–teacher platform that cannot satisfy district procurement and legal review will never reach large-scale deployment, regardless of features or usability.
Compliance standards define how parent–teacher communication platforms must be engineered, governed, and audited from day one. Without FERPA, COPPA, GDPR-K, and district governance embedded into the platform design, no system can operate safely at enterprise scale.
Core Features of a Secure Parent–Teacher Communication Platform
A secure parent–teacher communication platform includes role-based access control, end-to-end encrypted messaging, secure document sharing, real-time alerts, centralized broadcasts, full audit logs, parental consent controls, and multilingual communication.
These features ensure FERPA and COPPA-aligned data protection, prevent unauthorized access, and enable district-scale communication with complete visibility and compliance assurance.
1. Role-Based Access Control
Each user group operates within tightly governed permission boundaries. Parents can only view records related to their children. At the same time, teachers can access class-level communication and academic data. Additionally, administrators control system-wide visibility and policy enforcement.
This structure prevents accidental data exposure and limits internal misuse. It also simplifies compliance audits by clearly documenting who had access to what and when.
2. End-to-End Encrypted Two-Way Messaging
All communication is encrypted both while being transmitted and while stored. This applies to one-to-one conversations, group discussions, and school-wide broadcasts. Messages never exist in a readable state outside authorized user sessions.
Encryption protects student records from interception, data leaks, and unauthorized backend access. It also ensures communication remains legally defensible during audits and investigations.
3. Secure File and Document Sharing
Teachers routinely exchange sensitive documents with families. These include report cards, consent forms, medical updates, and intervention plans. A secure platform stores these files within encrypted repositories with defined access rights and retention policies.
This removes dependency on unsecured email attachments and consumer-grade cloud drives. It also creates a single source of truth for document access and history.
4. Real-Time Alerts
Schools depend on timely communication for attendance gaps, safety incidents, schedule changes, and emergency closures. The platform must support instant notifications with configurable urgency levels and delivery guarantees.
Priority routing ensures that critical alerts bypass standard queues and reach parents immediately. This capability directly impacts student safety and institutional accountability.
5. Centralized Broadcast Communication
Administrators require a controlled way to issue announcements across entire schools or districts. A centralized broadcast engine enables leadership to distribute policy updates, calendar changes, and public notices from a verified source.
This prevents message fragmentation across multiple informal channels. It also ensures families receive consistent, trusted communication without confusion or delay.
6. Full Audit Trails
Every message, file transfer, access event, and administrative action is logged automatically. These records include timestamps, user identifiers, and action history.
Audit trails support regulatory reporting, internal investigations, and legal review. They also establish institutional accountability by creating a verifiable record of all digital communication.
7. Data Governance Controls
Consent workflows must be built directly into the platform. Parents should be able to grant, modify, or revoke permissions for communication channels, data usage, and third-party integrations.
This ensures compliance with FERPA, COPPA, and regional student privacy regulations. It also strengthens parent trust by making data governance visible and controllable.
8. Multilingual Communication
Modern school communities are linguistically diverse. The platform must offer real-time translation, multilingual notifications, and accessible interfaces for families with varying literacy levels.
This reduces miscommunication, improves response rates, and ensures no family is excluded due to language barriers. It also aligns communication practices with equity and inclusion mandates.
Taken together, these features form the operational backbone of a compliant communication system. They protect student data, enforce accountability, and support daily engagement across classrooms, parents, and administrators. More importantly, they scale with district growth without multiplying security risk.
Architecture for a Secure Parent-Teacher Communication Platform
A secure parent–teacher communication platform is built on identity-first access control, role-based authorization, end-to-end encryption, zero-trust network segmentation, encrypted cloud storage, real-time audit logging, and a secure API gateway.
This architecture ensures FERPA and COPPA compliance, prevents unauthorized access, and supports district-scale communication with full operational visibility.
1. Role-Based Authorization
Once identity is verified, the authorization engine determines exactly what each user is permitted to see and perform. Parents access only their child’s records, teachers operate within assigned classes, and administrators manage system-wide configuration based on institutional policy.
This engine enforces least-privilege access at every interaction point. From a governance standpoint, it becomes the control layer that regulators and auditors evaluate first.
2. End-to-End Encryption
All communication must be encrypted from the moment it leaves a user’s device until it reaches its intended recipient. This includes messages, notifications, document transfers, and API requests. Data should never traverse internal or external networks in readable form.
Encryption at this layer protects against network interception, man-in-the-middle attacks, and internal exposure. It also establishes legal defensibility when data handling practices are reviewed.
3. Zero-Trust Network Segmentation
The platform must follow a zero-trust model where no internal service is automatically trusted. Each service validates identity, permissions, and request context before allowing access to data or functions.
This isolates core systems such as messaging, document storage, analytics, and administration. If any one component is compromised, the breach cannot spread laterally across the platform.
4. Encrypted Cloud Storage
Student records, communication logs, and shared documents must reside in encrypted storage environments. Data should be logically isolated by district, school, and user domain to prevent cross-tenant leakage.
This allows multi-district deployments to operate within a single cloud environment without violating data residency or segregation requirements. It also simplifies secure backup and disaster recovery design.
5. Secure API Gateway
Modern platforms integrate with SIS, LMS, identity systems, notification services, and analytics engines. Every integration must pass through a secured API gateway that enforces authentication, traffic throttling, and schema validation.
This prevents unauthorized system access and reduces the risk created by third-party extensions. It also ensures integrations remain auditable and compliant with data-sharing policies.
6. Real-Time Audit Logging
Every access event, message action, permission change, and file interaction must be logged in real time. These logs are stored securely and protected from tampering.
Live monitoring enables administrators to detect abnormal behavior, potential breaches, or policy violations immediately. Over time, audit logs become the foundation for compliance reporting and dispute resolution.
7. Compliance Governance
The architecture must encode regulatory requirements directly into system behavior. This includes data retention rules, deletion workflows, consent enforcement, and archival policies.
By embedding governance into architecture rather than manual procedures, institutions reduce human error and maintain continuous compliance without operational friction.
A secure parent–teacher communication platform succeeds only when its architecture is built for identity control, encryption, governance, and audit-readiness from day one. This foundation is what protects trust, sustains compliance, and enables district-scale growth without multiplying risk.
How Data Flows Securely Inside The Platform
In a secure parent–teacher communication platform, users authenticate through verified identities, messages are encrypted during transmission, stored in encrypted repositories, and accessed only after role-based validation. Every interaction is logged in real time for audit and compliance, ensuring FERPA and COPPA-aligned data protection across all communication workflows.
This is how a secure parent–teacher communication platform protects sensitive information at every step.
1. User Authentication at the Entry Point
Every session begins with identity verification. Parents, teachers, and administrators authenticate through secure login mechanisms integrated with institutional identity systems or verified credentials.
This ensures that only authorized users can initiate communication. It also establishes a verified identity context that follows every action taken inside the platform.
2. Secure Session Establishment and Access Validation
Once authenticated, the platform validates the user’s role and permissions before any data is accessed. Parents are restricted to their children’s records, teachers are limited to assigned classrooms, and administrators operate under governance-defined privileges.
This step prevents cross-user data exposure and enforces least-privilege access in real time.
3. Message Encryption During Transmission
When a message is sent, it is encrypted immediately on the sender’s device. It remains encrypted as it travels through the network and application servers.
At no point does the message exist in readable form during transit. This protects communication from interception across public networks and internal infrastructure.
4. Encrypted Storage and Data Isolation
Once delivered, messages and documents are stored in encrypted repositories. Data is logically isolated by district, school, and user domain to prevent cross-tenant exposure.
Encryption at rest ensures that even in the event of unauthorized system access, stored data remains unreadable and protected.
5. Controlled Retrieval and Decryption at the User Level
When an authorized recipient opens a message or document, decryption occurs only within their secure session. The platform validates identity and permissions again before rendering any content.
This double-verification prevents session hijacking and unauthorized reuse of stored communication data.
6. Continuous Audit Logging of Every Interaction
Every login, message action, file access, and administrative change is recorded in real time. These logs include user identity, timestamps, and the nature of the interaction.
Audit trails enable compliance reporting, internal investigations, and legal verification without relying on manual record-keeping.
7. Administrative Monitoring and Policy Enforcement
Administrators monitor system activity through governed dashboards. They can detect abnormal behavior, policy violations, or unusual access patterns.
This enables proactive risk response instead of reactive breach management. It also supports continuous compliance across large school networks.
How We Build Secure Parent-Teacher Communication Platforms
Building a secure parent–teacher communication platform starts long before development begins. It requires a disciplined engineering process that treats privacy, governance, and scalability as first-order design parameters. This is the structured approach we follow to ensure every deployment is audit-ready, resilient, and built for long-term district adoption.
1. Compliance-First Discovery
We begin by defining the regulatory and operational boundaries of the platform. This includes mapping FERPA, COPPA, regional student data laws, and district vendor-governance policies into system requirements. Communication use cases are documented across parents, teachers, administrators, and support staff.
This phase identifies what data can be collected, where it can flow, and how long it can be retained. It prevents rework later and ensures legal alignment from the first architectural decisions.
2. Governance Architecture Design
Next, we design the identity and authorization framework. This includes role structures, least-privilege access policies, session rules, and integration with institutional identity providers. Governance workflows for consent, access change, and administrative escalation are defined here.
By locking governance into architecture early, security becomes systemic rather than dependent on manual controls.
3. Secure Platform and Feature Engineering
Core communication features are then engineered on top of encrypted transport and storage layers. Messaging, file sharing, alerts, broadcast modules, and consent workflows are developed as governed services rather than isolated features.
Each service is tested against misuse scenarios, internal threat models, and data-leak risks. This ensures that convenience never overrides security.
4. Integration With Identity Systems
We integrate the platform into the district’s existing digital ecosystem. This includes SIS for student records, LMS for classroom alignment, and SSO for unified identity management.
Integrations are routed through secure API gateways with strict data-scoping rules. This allows the platform to operate as part of the institution’s core infrastructure rather than as a standalone tool.
5. Security and Audit Readiness
Before deployment, the platform undergoes penetration testing, privacy impact assessments, and internal security audits. Data flows, permissions, consent enforcement, and retention policies are validated against regulatory expectations.
This stage transforms the system from a technical build into a legally defensible communication platform.
6. Phased Deployment
We deploy in controlled phases, typically starting with selected schools or pilot cohorts. This allows real-world validation of performance, adoption behavior, and support workflows.
Once stability is proven, the platform is scaled across the district or education network with centralized governance and monitoring.
7. Continuous Monitoring and Updates
Post-deployment, we maintain continuous monitoring of access behavior, system performance, and policy compliance. Regulatory updates, district policy changes, and evolving security threats are translated into platform updates.
This ensures that the communication system remains secure, compliant, and operationally aligned throughout its lifecycle.
A secure communication platform is only as strong as the process used to build it. When compliance, identity, and encryption drive every development decision from the start, the result is a system that scales safely and earns institutional trust.
Cost to Build a Secure Parent–Teacher Communication Platform
Building a secure parent–teacher communication platform requires sustained investment across encrypted communication infrastructure, identity governance, large-scale integrations, consent management, monitoring systems, and regulatory compliance. The total cost varies based on district size, number of schools, user volume, integration scope, and the depth of security controls required.
At Intellivon, we design cost models aligned with district governance frameworks, long-term IT strategy, and regulatory mandates. Each roadmap balances privacy, uptime, and fiscal discipline. For platforms operating under public funding cycles and strict compliance review, we phase development to preserve FERPA, COPPA, and state-level alignment without compromising adoption.
Estimated Phase-Wise Cost Breakdown
| Phase | Description | Estimated Cost (USD) |
| Discovery & Compliance Blueprint | Requirements analysis, communication workflows, FERPA/COPPA alignment, district governance | 6,000 – 12,000 |
| Secure Cloud Architecture & Identity Setup | Cloud-native design, encryption framework, IAM, PII isolation | 10,000 – 20,000 |
| Core Messaging & File Sharing Engine | Encrypted two-way messaging, secure document sharing, delivery controls | 12,000 – 24,000 |
| Role-Based Access & Consent Management | Parent, teacher, admin permissions, consent workflows, policy enforcement | 7,000 – 14,000 |
| Broadcast & Alerting Systems | Emergency alerts, attendance notices, priority notifications | 6,000 – 12,000 |
| SIS, LMS & SSO Integrations | PowerSchool, Skyward, OneRoster, Clever, ClassLink, OAuth, SAML | 8,000 – 16,000 |
| Audit Logs & Compliance Monitoring Systems | Tamper-proof logs, access monitoring, regulatory reporting | 7,000 – 12,000 |
| Security Engineering & Threat Protection | API security, anomaly detection, intrusion prevention | 7,000 – 12,000 |
| Testing, QA & Security Validation | Load testing, penetration testing, privacy validation | 7,000 – 12,000 |
| Pilot Deployment, Training & Rollout | Administrator onboarding, school rollout, workflow tuning | 7,000 – 12,000 |
Total Initial Investment Range
USD 87,000 – 176,000
Annual Maintenance & Optimization
14–22% of the initial development cost
Hidden Costs Organizations Should Plan For
- Integration complexity increases as districts operate multiple SIS and LMS environments across schools and grade levels.
- Privacy assessments, vendor risk reviews, breach simulations, and regulatory updates require continuous legal and engineering support.
- Data governance and correction workflows introduce recurring costs as student records evolve across academic years.
- Cloud consumption rises steadily as real-time messaging, notifications, monitoring, and backups scale across thousands of users.
- Change management and training remain long-term investments with staff turnover, new teachers, and updated district policies.
- Security hardening is continuous as threat patterns shift and compliance requirements tighten.
Best Practices to Avoid Budget Overruns
- Begin with a tightly defined scope anchored around messaging, alerts, audits, and compliance reporting.
- Engineer compliance rules in the first architecture phase rather than layering controls after launch.
- Use a modular, microservices-based architecture to limit redevelopment cost during upgrades.
- Separate real-time communication workloads from audit analytics to control cloud compute spikes.
- Maintain full observability across access behavior, integrations, and security posture.
- Let platform evolution follow real school usage patterns instead of early-stage assumptions.
Get a precise cost estimate for your district. Book a 30-minute strategy call with Intellivon to receive your custom quote, phased roadmap, and compliance-aligned deployment plan.
Top Examples Of Parent-Teacher Communication Platforms
Large-scale adoption of parent–teacher communication platforms is no longer experimental. Several enterprise-grade platforms now support millions of daily interactions across entire school networks. These examples show how secure, district-ready communication systems operate at a real-world scale.
1. ClassDojo
ClassDojo operates in a majority of elementary and middle schools across the United States and supports usage across more than 180 countries. The platform handles tens of millions of daily interactions between teachers and families.
From a security perspective, ClassDojo introduced district-level deployments with centralized administration, roster management, and controlled access. Private messaging masks personal phone numbers and accounts operate under a school-managed identity. Translation support across multiple languages allows secure engagement with diverse family groups without routing data through third-party consumer apps.
Its scale demonstrates that parent–teacher communication has moved into the category of critical digital infrastructure rather than a classroom utility.
2. ParentSquare
ParentSquare is widely adopted by large public school districts as a unified school–home communication hub. It consolidates messaging, announcements, permission slips, event scheduling, and secure document sharing into one governed system.
The platform emphasizes identity verification, SIS synchronization, and district-controlled delivery channels across app, SMS, email, and web. This ensures communication remains inclusive while still governed by institutional security and compliance controls.
ParentSquare’s district-wide deployments illustrate how communication platforms can replace fragmented tools while remaining audit-ready at scale.
3. Remind
Remind gained early traction across K–12 education for its simple, reliable teacher-parent messaging workflows. Millions of educators adopted it as a safer alternative to personal text messaging.
Over time, Remind expanded into school-wide and multi-school deployments with administrative controls, message archiving, and compliance-aware communication records. It allowed institutions to preserve fast engagement while adding governance layers required for regulated environments.
Its evolution highlights how basic messaging tools must mature operationally to meet enterprise security expectations.
4. Edsby
Edsby represents a different enterprise category. It combines learning management, attendance tracking, analytics, and parent–teacher communication within a single district-scale platform.
Parents access grades, assignments, announcements, and secure messaging inside a unified identity framework. Because communication operates within the same secure environment as academic data, governance becomes centralized instead of fragmented across multiple vendors.
Edsby’s deployments show the advantage of embedding communication directly into core instructional systems rather than running it as a disconnected layer.
These platforms share common characteristics that define true enterprise readiness. They operate across entire districts, integrate with academic systems, enforce controlled identity, preserve communication records, and support multilingual family engagement.
Conclusion
Security is no longer optional in school communication systems. As digital engagement becomes foundational to education delivery, institutions must assume that every message, document, and alert carries regulatory and reputational risk. Compliance now directly drives adoption, procurement, and long-term platform viability.
At the same time, platforms must scale safely across schools, districts, and public networks without multiplying exposure or operational complexity. Most importantly, trust determines long-term success. When families trust how their data is protected and how communication is governed, engagement strengthens, adoption accelerates, and digital infrastructure becomes a true growth enabler rather than a liability.
Build a Secure Parent–Teacher Communication Platform With Intellivon
At Intellivon, we develop enterprise-grade parent–teacher communication platforms that combine compliance-first architecture, identity-led security, and institution-scale communication governance. Our systems unify encrypted messaging, secure document exchange, alerting, consent management, and audit-ready communication into one regulated digital engagement ecosystem.
Each platform is engineered for large institutional environments. It remains resilient under peak communication loads, compliant under regulatory scrutiny, and scalable across multi-school and multi-region education networks. From identity-verified access to encrypted message delivery and tamper-proof audit trails, every layer is designed to support secure, trusted school–home communication from the first deployment cycle.
Why Partner With Intellivon?
- Compliance-First Communication Architecture: Aligned with FERPA, COPPA, GDPR-K, and regional student data privacy laws across global education operations.
- Identity-First Security Framework: Role-based access, verified sessions, and strict permission boundaries that prevent unauthorized exposure of student and family data.
- Encrypted Messaging & Document Infrastructure: End-to-end encryption for conversations, alerts, and shared records with secure storage and controlled retention.
- Enterprise-Scale Cloud Infrastructure: High availability, elastic scaling, and multi-tenant isolation for uninterrupted communication across large institutional footprints.
- Continuous Governance & Audit Readiness: Real-time monitoring, immutable communication logs, and policy-driven controls aligned with evolving regulatory standards.
Book a strategy call with Intellivon to explore how a custom-built, enterprise-grade parent–teacher communication platform can protect sensitive data, strengthen compliance confidence, and scale trusted communication across your education ecosystem.
FAQs
Q1. What makes a parent–teacher communication platform “secure” at an enterprise level?
A1. A platform is considered enterprise-secure when it enforces role-based access, end-to-end encryption, identity verification, audit logging, and compliance with FERPA, COPPA, and regional privacy laws. Security is embedded into architecture, not added as a layer after deployment.
Q2. Can a secure parent–teacher communication platform integrate with our existing SIS and LMS systems?
A2. Yes. Enterprise-grade platforms are designed for native integration with SIS, LMS, and identity systems through secure APIs and SSO. This allows communication to stay synchronized with enrollment, attendance, schedules, and academic records without duplicating data or creating security gaps.
Q3. How do these platforms ensure compliance with FERPA and COPPA in daily communication?
A3. Compliance is enforced through consent workflows, access controls, encrypted storage, data minimization, and immutable audit trails. Every message, file, and access event is governed by policy rules that align operational communication with regulatory requirements automatically.
Q4. What is the typical implementation timeline for an enterprise deployment?
A4. Most enterprise deployments follow a phased rollout over 12–20 weeks. This includes compliance discovery, architecture design, core platform setup, integrations, security validation, pilot deployment, and controlled scale-up across institutions or regions.
Q5. How does a secure communication platform reduce institutional risk and operational cost?
A5. It replaces unsecured messaging, email chains, and consumer apps with one governed system. This reduces legal exposure, eliminates data leakage, simplifies audits, lowers administrative overhead, and strengthens parent trust, which directly improves adoption and long-term platform ROI.