Fraud is a constant risk that can quietly slow business growth for large fintech enterprises. When fake identities or false vendors get through checks, the impact goes beyond immediate financial losses. These types of fraud often blend in with normal activity, especially in busy fintech environments, and can be hard to spot with older, rule-based systems.
Most standard security tools are not designed for the scale and speed of global businesses. They may struggle with high transaction volumes or flag too many real customers as risks. To address these challenges, many companies now use AI-powered fraud detection systems that learn from patterns and spot unusual activity in real time. This helps businesses grow and protect their customers at the same time.
At Intellivon, our AI-powered fraud detection systems are designed to fit smoothly into existing technology and meet international compliance requirements. This blog outlines how we build a reliable fraud detection platform for large organizations that is AI-driven and scales alongside the enterprise.
Why Traditional Fraud Controls Are Failing Modern Fintech Ecosystems
Traditional fraud systems fail in modern fintech because they rely on static rules that cannot adapt to real-time payment speeds or behavioral anomalies.
AI-powered fraud detection solves this by using machine learning to analyze vast datasets instantly, reducing false positives and identifying coordinated “low-and-slow” attacks that manual reviews miss.
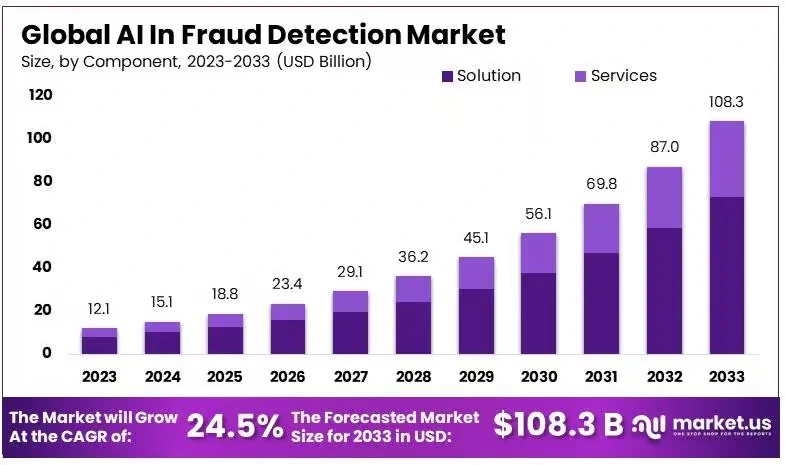
AI-driven fraud detection tools are gaining rapid traction as cyber threats grow alongside digital transaction volumes. As a result, enterprise adoption continues to rise, with the market expected to see strong expansion through 2033.
When an organization relies on outdated tools, they do more than just miss fraudulent activity. They often create unnecessary friction for their legitimate users. In a competitive market, this inefficiency becomes a significant barrier to expansion.
1. Cannot Keep Up With Real-Time Payments
Most traditional systems operate on simple if-then logic. For example, a rule might flag any transaction over $10,000.
However, modern fraudsters understand these thresholds. They intentionally stay just below them to avoid detection. Because these rules are static, they cannot adjust to new tactics without manual intervention.
In a real-time payment environment, every millisecond counts. If your system takes too long to analyze a transaction against a massive list of rules, the user experience suffers.
Conversely, if the rules are too loose to ensure speed, the risk of loss increases. This trade-off is no longer necessary when you use intelligent orchestration.
2. Cross-Border Activity Creates Blind Spots
Expanding into new territories brings a surge in data complexity. Different regions have unique spending habits and local payment methods.
They also have varying regulatory requirements. Traditional controls often struggle to normalize this data. This leads to a fragmented view of risk across your global operations.
- Data Silos. Information from one market often does not communicate with another.
- Localized Patterns. What looks like fraud in London might be standard behavior in Singapore.
- Compliance Gaps. Rigid systems often fail to adapt to the specific laws of new jurisdictions.
Without a unified AI layer, these regional differences become hiding spots for criminal networks.
3. Fraud Has Become Behavioral and Coordinated
The biggest threat today is not a single stolen credit card. Instead, it is the rise of synthetic identities and coordinated bot attacks.
These mimic human behavior and might log in at normal hours or browse pages slowly before they strike.
Rule-based systems cannot see the big picture of a user journey. Instead, they see a single transaction rather than the suspicious pattern leading up to it. Identifying these subtle shifts requires behavioral biometrics. Only advanced machine learning can provide this level of pattern recognition.
4. Manual Review Is No Longer Scalable
As your enterprise grows, the number of flagged transactions naturally increases. If your system relies on human analysts to clear these alerts, you will eventually hit a breaking point. This creates a massive bottleneck for your operations.
- Operational Costs. Hiring and training a massive compliance team is expensive.
- Inconsistency. Different analysts may interpret the same data differently.
- Slow Onboarding. Making a customer wait 48 hours for a manual check is a mistake.
Automating the vast majority of these decisions allows your expert team to focus on the most complex cases. This shift transforms your risk department into a lean unit that supports business growth.
What Is an Enterprise-Grade AI Fraud Detection System?
An enterprise AI fraud detection system is a multi-layered decisioning engine that processes identity, device, and behavioral signals in real time. It uses machine learning to score risk and automate actions such as approvals or step-up authentication.
This architecture ensures high-speed security while maintaining a frictionless experience for legitimate enterprise users. This allows your organization to trigger immediate actions like allowing a payment, requiring extra authentication, or blocking a high-risk attempt entirely.
What it does
A sophisticated fraud engine transforms how your organization handles risk. It moves your team from manual checks to automated intelligence. This shift is essential for maintaining the speed of modern finance.
- Detects suspicious activity in milliseconds. Real-time processing ensures that you stop fraud before the transaction is finalized.
- Prioritizes investigations. The system automatically surfaces the most complex threats. Consequently, your human analysts can focus their time where it matters most.
- Orchestrates risk actions. You can set the system to trigger different responses based on the risk score. These responses might include a simple SMS verification or a full manual hold.
- Improves over time through feedback loops. Every outcome is fed back into the machine learning models. This means the system becomes more accurate as it processes more data.
Managing these complex layers requires a balance of high-speed data engineering and deep psychological insights. However, when you implement this correctly, the system becomes an invisible shield. It protects your revenue without slowing down your customers.
An enterprise-grade AI system moves your fraud strategy from reactive defense to proactive prevention. It ensures your security scales at the same pace as your global transaction volume.
When Does It Make Strategic Sense to Invest in AI Fraud Detection?
Organizations should invest in AI fraud detection when manual reviews bottleneck growth or when false positive rates degrade the customer experience.
Transitioning to machine learning models allows enterprises to scale across borders without increasing headcounts. This investment also mitigates systemic fraud losses and ensures continuous compliance with evolving global regulations.
However, the true trigger occurs when your current risk posture begins to stifle your ability to compete in a digital-first market. Therefore, identifying these inflection points early allows your leadership team to protect both your margins and your reputation.
1. When Fraud Losses Become Systemic
Occasional fraud is a known cost of doing business. Specifically, when these losses become a predictable and growing percentage of your revenue, your current controls are no longer effective.
Traditional systems often miss “low and slow” attacks where fraudsters chip away at small amounts over time. These systemic losses can quickly drain your resources if they are not caught by adaptive algorithms.
2. When False Positives Affect Customer Experience
Nothing hurts a fintech brand faster than declining a legitimate transaction. If your rules are too strict, you will inevitably flag honest customers as potential threats.
Consequently, these users will likely take their business to a competitor who offers a smoother experience. An AI system reduces this friction by understanding the nuance of individual user behavior.
3. When Manual Controls Slow Growth
Scaling an enterprise requires speed and efficiency. If every new market expansion requires hiring dozens of additional human reviewers, your growth model is unsustainable. In addition, manual processes are inherently slower than automated decisioning.
Moving to an AI-powered layer allows you to handle millions of transactions without increasing your operational headcount.
4. When Compliance Risk Begins Rising
Global regulators are increasingly demanding more sophisticated anti-money laundering and fraud prevention measures. Relying on basic checks may leave your organization vulnerable to heavy fines and legal scrutiny.
Therefore, implementing an advanced detection system is a proactive way to meet these evolving standards. It demonstrates to regulators that your enterprise takes financial integrity seriously.
The right time to invest is before your legacy systems reach their breaking point. This strategic move ensures your infrastructure can support your long-term business goals without compromise.
High-Risk Fraud Scenarios Your AI System Must Detect
Advanced AI fraud detection systems must identify high-risk scenarios like Authorized Push Payment (APP) fraud and synthetic identity creation. Consequently, enterprises can prevent sophisticated insider abuse and external attacks before they impact the bottom line.
A robust AI system must recognize these patterns across every touchpoint of your enterprise. Therefore, your security layer needs to be as dynamic as the criminals attempting to bypass it.
1. Authorized Push Payment Manipulation
In this scenario, a fraudster tricks a legitimate user into sending a payment voluntarily. This often happens through social engineering or spoofed invoices. Because the user authorizes the transaction, traditional systems usually mark it as safe.
However, an AI-powered system analyzes the recipient’s history and the timing of the request. It can flag unusual patterns that suggest a user is being manipulated.
2. Synthetic Identity Creation
Criminals often combine real and fake data to create entirely new personas. Specifically, they might use a stolen Social Security number with a fictional name and address.
These identities can stay dormant for months while building a positive credit history. An intelligent system looks for anomalies in how these identities were formed. It detects the subtle signs of a manufactured profile before a major theft occurs.
3. Account Takeover
Account takeover happens when an unauthorized person gains access to a user’s credentials. This typically leads to rapid fund depletion or unauthorized data changes.
A static rule might not catch a login from a new device if the password is correct. In contrast, behavioral biometrics analyzes how the user interacts with the app. This includes typing speed and navigation habits to confirm the person is truly who they claim to be.
4. Transaction Laundering
This complex fraud involves hiding illegal sales behind a legitimate merchant account. For example, a small online store might process payments for prohibited goods or services.
These activities are difficult to spot because they appear to be standard e-commerce transactions. An AI engine monitors merchant behavior and settlement patterns to find these hidden links. Consequently, your enterprise avoids unknowingly facilitating criminal activity.
5. Insider Abuse
Internal threats are often the hardest to detect because employees already have authorized access. This might involve an administrator overriding a block or diverting small amounts of capital.
Standard audit logs are often too massive for manual review. However, machine learning can baseline normal employee behavior and flag any deviations. Therefore, you can identify suspicious internal actions without creating a culture of distrust.
Detecting these high-risk scenarios requires a system that understands both technical data and human behavior. This comprehensive approach ensures that your enterprise remains protected against even the most sophisticated attacks.
Core AI Engines That Power Enterprise Fraud Detection
The strength of your fraud defense depends on the intelligence of its underlying engines. A modern enterprise system uses a multi-layered approach to analyze data from different angles. This coordination allows the platform to verify identity and intent simultaneously.
Therefore, your organization can maintain high security without slowing down legitimate users. Specifically, these core engines work together to create a comprehensive view of every interaction.
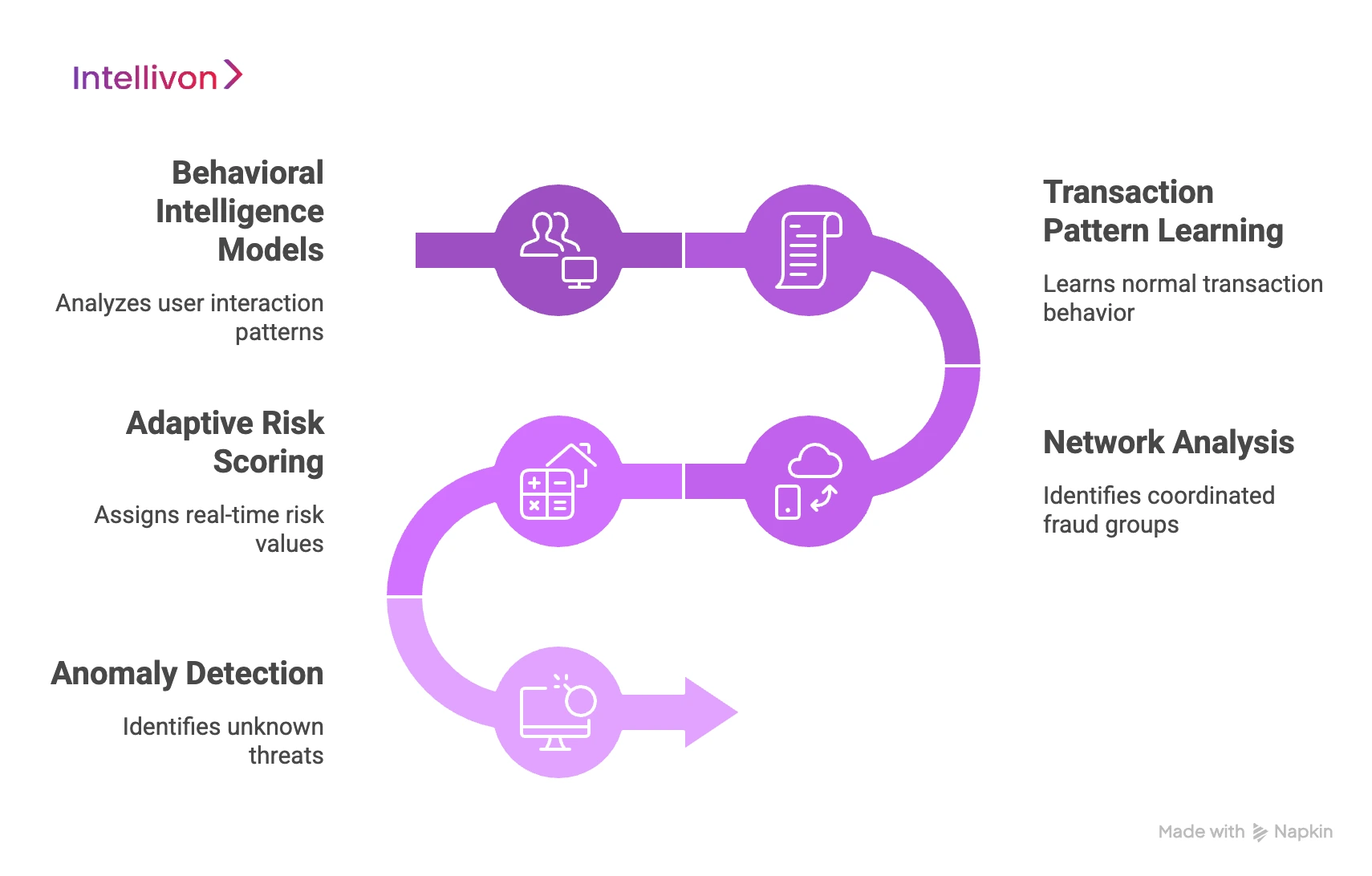
1. Behavioral Intelligence Models
This engine focuses on how a user interacts with your digital interface. It analyzes subtle movements like typing speed, mouse patterns, and navigation habits.
Because these physical traits are unique to each person, they are nearly impossible for a bot to mimic. However, if a user’s behavior suddenly changes, the system can trigger a step-up authentication.
2. Transaction Pattern Learning
This model looks at the historical context of every payment. It learns what a “normal” transaction looks like for a specific customer or merchant.
- Velocity Checks. It monitors how many transactions occur within a short window.
- Spending Habits. The engine flags purchases that fall far outside a user’s typical range.
- Geospatial Data. It compares the transaction location with the user’s known travel patterns.
3. Network Analysis
Fraudsters often work in coordinated groups using linked devices or accounts. Network analysis identifies these hidden connections by mapping relationships between data points.
Specifically, it can spot a single device being used to log into multiple unrelated accounts. Consequently, you can stop a massive attack before it spreads across your entire ecosystem.
4. Adaptive Risk Scoring
Unlike static rules, adaptive scoring assigns a unique risk value to every event. This score changes in real time based on the latest data and emerging threats.
- Dynamic Thresholds. The system can tighten security during high-risk periods like holiday sales.
- Granular Control. You can set different actions for low, medium, and high-risk scores.
- Continuous Updates. The engine learns from every confirmed case of fraud to improve its future accuracy.
5. Anomaly Detection
This engine identifies “unknown unknowns” by looking for data that does not fit any established pattern. It is particularly effective against zero-day attacks that have never been seen before.
Because it does not rely on a list of known threats, it can catch new fraud tactics as they emerge. Therefore, your enterprise remains protected even when criminals pivot to new methods.
These core engines transform your data into a strategic asset. They ensure that your fraud detection is both proactive and precise.
How AI Improves Fraud Detection Beyond Rules-Based Systems
AI improves fraud detection by identifying unknown attack patterns that static rules miss. Machine learning models use behavioral analytics to differentiate between legitimate users and sophisticated bots.
Consequently, enterprises can reduce false positive alerts by up to 75%. This shift enhances analyst productivity and allows security systems to adapt instantly to emerging fraud tactics.
1. Detecting Unknown Attack Patterns
Traditional systems can only stop threats that have been seen before. If a fraudster changes a single variable, a rule-based filter might fail.
In contrast, AI identifies anomalies that do not fit any established profile. It looks for deviations in data clusters rather than specific triggers. Because of this, your system can catch “zero-day” attacks before they become a widespread problem.
2. Learning From Behavior
A stolen password is a static attribute that any fraudster can use. However, the way a person types or moves their mouse is much harder to replicate.
Behavioral analytics serve as a major differentiator for enterprise-grade platforms. The system creates a unique signature for every legitimate user. If an interaction deviates from this signature, the engine flags it for closer inspection.
3. Reducing False Positives
This is perhaps the strongest driver for enterprise investment. High false positive rates frustrate your customers and lead to abandoned transactions. Leading industry benchmarks show that specialized AI hubs can reduce false positive alerts by 75%.
Specifically, machine learning understands the nuance of high-value, legitimate spending. This ensures that your best customers never face unnecessary hurdles during their journey.
4. Adapting to Changing Fraud Tactics
Fraudsters pivot their methods as soon as a hole is plugged. Platforms like Adyen and PayPal emphasize that their models undergo constant risk tuning. These systems learn from every successful and unsuccessful transaction.
Consequently, your defense evolves at the same pace as the criminals. This adaptability is essential for maintaining security in a global, fast-moving market.
5. Supporting Better Analyst Productivity
AI should narrow your review queues rather than flooding them with low-level alerts. By automating clear-cut decisions, the system allows your experts to focus on the most complex cases.
It provides analysts with the “why” behind every risk score. This context makes the manual review process much faster and more accurate. Therefore, your team becomes a highly efficient unit rather than a bottleneck.
A transparent approach to AI acknowledges that human expertise still matters for high-stakes edge cases. This balance of machine speed and human judgment creates the most resilient fraud strategy possible.
Core Architecture of an AI-Powered Fraud Detection System
An enterprise AI fraud architecture consists of eight integrated layers. This holistic approach ensures high-speed accuracy and long-term model health. Specifically, the following eight components form the backbone of an elite fraud prevention strategy.
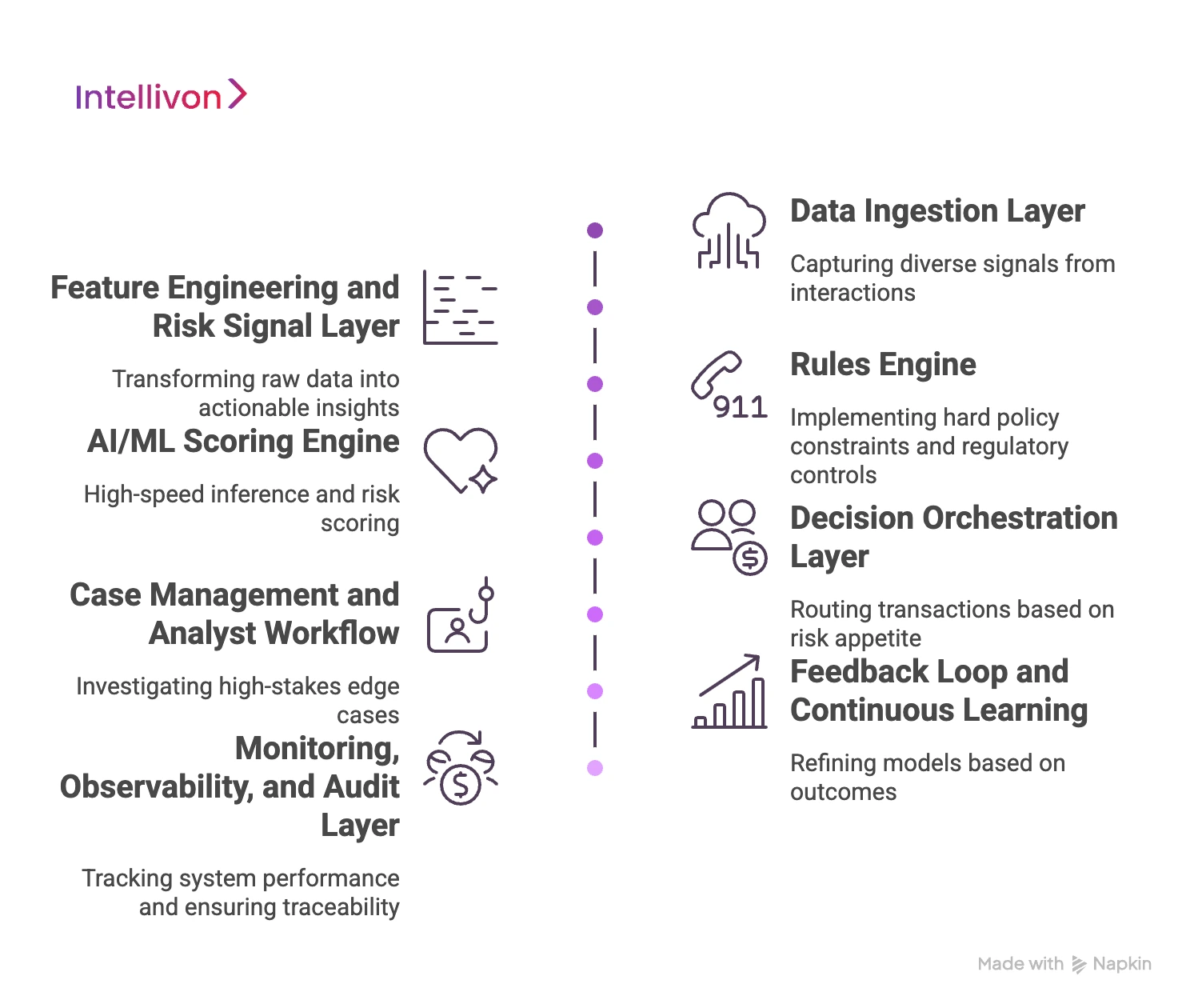
1. Data Ingestion Layer
The quality of your detection starts with the breadth of your inputs. A robust ingestion layer captures a wide variety of signals from every interaction. This includes core transaction details and ledger events alongside deep identity markers.
- Identity and Context. KYC and KYB data must merge with real-time device telemetry.
- Environmental Signals. The system tracks IP addresses, geographic data, and session behavior.
- Historical Context. Past disputes and third-party risk signals are integrated instantly. Consequently, the system creates a rich, multi-dimensional view of every single event.
2. Feature Engineering and Risk Signal Layer
Raw data must be transformed into actionable insights before it reaches the models. This layer calculates complex variables that describe behavior.
- Velocity Checks. Monitoring how often an entity acts within a specific time window.
- Entity Linking. Finding hidden connections between seemingly unrelated accounts.
- Device Fingerprinting. Identifying a specific hardware profile, even if the user changes their IP. In addition, this layer manages behavioral baselines and customer clustering. These signals provide the essential context that the AI needs to make an accurate judgment.
3. Rules Engine
While AI handles the nuance, a traditional rules engine remains vital for hard policy constraints. These rules ensure that your organization stays within legal and regulatory boundaries.
- Regulatory Controls. Implementing mandatory AML or regional compliance checks.
- Blocklists and Allowlists. Instantly stopping known bad actors or fast-tracking trusted partners.
- Threshold Overrides. Setting hard limits on transaction sizes for specific risk tiers. Therefore, the rules engine acts as a primary safety net for the entire system.
4. AI/ML Scoring Engine
This is the heart of the platform where high-speed inference happens. Following the lead of global leaders like PayPal, we use a mix of learning styles to ensure coverage.
- Supervised Models. These learn from large datasets of labeled fraud examples.
- Unsupervised Anomaly Detection. These identify new, unknown patterns without prior training.
- Ensemble Scoring. Combining multiple model outputs into a single, highly accurate risk score. This multi-layered approach allows the system to detect both known and emerging threats simultaneously.
5. Decision Orchestration Layer
Once a risk score is generated, the system must decide on an action. This layer routes the transaction based on your specific risk appetite.
- Automated Actions. Approving low-risk events or declining clear fraud immediately.
- Step-up Authentication. Triggering an SMS or biometric check for suspicious activity.
- Operational Holds. Freezing an account or throttling a suspicious merchant in real time. This ensures that your response is always proportional to the detected level of risk.
6. Case Management and Analyst Workflow
Not every decision can be fully automated. A sophisticated case management system allows your human experts to investigate high-stakes edge cases.
- Queue Prioritization. Surfacing the most urgent alerts to the top of the list.
- Link Analysis. Visualizing relationships between accounts to find fraud rings.
- Incident Support. Providing all the necessary data for regulatory filings or incident reports. Consequently, your analysts spend their time on the most impactful investigations.
7. Feedback Loop and Continuous Learning
The system must learn from its own successes and failures to remain effective. Feedback loops ensure that your models do not become stagnant over time.
- Analyst Dispositions. Feeding manual review outcomes back into the training set.
- Chargeback Outcomes. Updating the model when a fraud event is confirmed after the fact.
- Drift Monitoring. Identifying when model accuracy begins to drop as fraud tactics change. This continuous refinement cycle is what keeps an enterprise-grade system ahead of the competition.
8. Monitoring, Observability, and Audit Layer
This final layer provides a window into how the system is performing at all times.
- Latency Tracking. Ensuring that security checks do not slow down the user experience.
- Decision Traceability. Providing a clear “why” behind every approval or decline for audit purposes.
- Model Health. Tracking score distributions and rule hit rates to ensure stability. Therefore, your leadership team always has a clear view of your organization’s risk posture.
Building this entire machine requires deep expertise in both data engineering and financial security. When these eight layers work in harmony, they turn risk management into a powerful growth enabler.
Integrating AI Fraud Detection Into Existing Fintech Systems
Successful AI fraud detection integration requires a unified data layer across core banking, payment infrastructure, and open banking APIs.
By embedding machine learning into card and wallet systems, enterprises can achieve real-time risk scoring without increasing latency.
This architectural alignment ensures that security remains consistent across all digital touchpoints and legacy environments.
1. Core Banking
Your core banking system is the primary source of truth for customer identities and account balances. Integrating AI here allows the system to monitor internal movements and high-value transfers.
- Historical Data Access. The AI engine uses years of transaction history to build accurate user baselines.
- Account-Level Monitoring. Detecting subtle changes in account behavior that might indicate a long-term compromise.
- Regulatory Reporting. Automating the data collection required for suspicious activity reports. In addition, this connection ensures that any risk decision is immediately reflected in the user’s primary account status.
2. Payment Infrastructure
Payment rails require extreme speed and high availability. An AI layer must integrate via low-latency APIs to score transactions in the middle of the payment flow.
- Real-Time Gateway Hooks. The system intercepts payment requests to provide an instant go or no-go decision.
- Network Coordination. Syncing with external payment networks to verify merchant and acquirer data.
- Settlement Protection. Identifying fraudulent patterns before the final settlement occurs. Therefore, your payment infrastructure remains protected without adding any noticeable delay to the customer experience.
3. Card and Wallet Systems
Digital wallets and physical cards are frequent targets for high-frequency fraud. Integrating AI into these systems allows for more granular control over individual spending limits and locations.
- Tokenization Security. Monitoring the lifecycle of digital tokens used in mobile wallets.
- Geospatial Syncing. Comparing the location of a card swipe with the real-time location of the user’s mobile device.
- Merchant Category Controls. Automatically blocking high-risk merchant types based on the user’s historical profile. Consequently, your card program can offer higher limits to trusted users while strictly controlling risk.
4. Open Banking APIs
The rise of open banking has created new entry points for sophisticated attackers. Securing these APIs requires an AI system that understands the nuances of third-party data sharing.
- Consent Verification. Ensuring that data requests are legitimate and authorized by the actual account holder.
- API Pattern Recognition. Identifying bot-driven attempts to scrape data or test credentials through open endpoints.
- Third-Party Risk Scoring. Assigning risk values to the different fintech apps connecting to your infrastructure. This proactive approach ensures that your open banking initiatives drive innovation without introducing new vulnerabilities.
Successful integration turns your existing infrastructure into a powerful sensor network for detecting fraud. This architectural alignment is what separates a basic security tool from an enterprise-grade intelligence platform.
Regulatory Expectations for AI-Based Fraud Monitoring
Regulatory expectations for AI fraud systems focus on model explainability, detailed audit trails, and continuous monitoring.
Enterprises must align their AI outputs with AML and KYC standards while adhering to GDPR and CCPA data privacy laws. Consequently, a compliant fraud architecture ensures that every automated decision is traceable and justifiable to global financial regulators.
1. Explainability
Regulators often refer to this as the “right to an explanation.” If your system declines a transaction or freezes an account, you must be able to explain why. Black-box models that cannot describe their reasoning are a major compliance risk.
- Feature Importance. Showing which specific data points led to a high risk score.
- Natural Language Justification. Providing a human-readable summary for every automated action.
- Bias Detection. Regularly testing models to ensure they do not discriminate based on protected characteristics. Therefore, choosing an explainable AI framework is essential for maintaining your social and legal license to operate.
2. Audit Trails
Every decision made by your AI system must be recorded in a tamper-proof log. This trail is the first thing a regulator will ask for during a formal review.
- Decision Traceability. Mapping every risk score back to the specific model version that generated it.
- Data Lineage. Tracking where the input data came from and how it was transformed.
- Override Logs. Documenting whenever a human analyst manually changed an AI-generated decision. Consequently, your organization can prove that it maintains full control over its automated infrastructure at all times.
3. Continuous Monitoring
A static model is a non-compliant model. Regulators expect your enterprise to monitor for “model drift,” where accuracy fades as fraud patterns change.
- Performance Benchmarks. Tracking false positive rates and detection accuracy in real time.
- Threshold Retuning. Updating your risk levels to reflect the current threat environment.
- Stress Testing. Simulating massive fraud attacks to ensure your system remains resilient under pressure. In addition, this constant oversight ensures that your security remains effective without becoming a bottleneck for legitimate growth.
4. AML Alignment
Your fraud detection system must feed directly into your Anti-Money Laundering (AML) workflows. This includes the automated generation of Suspicious Activity Reports (SARs) when certain triggers are met.
- KYC Integration. Cross-referencing transaction patterns with verified customer profiles.
- Sanctions Screening. Instantly checking participants against global watchlists like OFAC.
- PEP Identification. Monitoring transactions involving Politically Exposed Persons for increased risk. Compliance with these rules is mandatory under frameworks like the Bank Secrecy Act and the EU’s Anti-Money Laundering Directives.
5. Essential Compliance Frameworks
To operate legally in global markets, your AI-powered platform must adhere to several key regulations.
- GDPR and CCPA. Protecting user privacy and the right to data deletion.
- PCI DSS. Ensuring the secure handling of sensitive credit card information.
- SOC2 Type II. Demonstrating high standards for data security and operational privacy.
- PSD2 / SCA. Following Strong Customer Authentication rules for electronic payments in Europe.
Navigating these regulations requires a partner who understands the intersection of high-level math and international law. A compliant system protects your organization from both criminals and regulatory penalties.
How We Build an AI-Powered Fraud Detection System
Building an enterprise-grade defense requires a structured approach that balances technical depth with operational reality. At Intellivon, we engineer complete fraud scoring services and data pipelines that integrate with your existing workflows.
Our methodology focuses on creating a resilient intelligence layer that scales alongside your transaction volume. Therefore, we follow a rigorous seven-step process to ensure your system is both accurate and auditable. Specifically, this framework ensures that every component of your fraud strategy is aligned with your broader business goals.
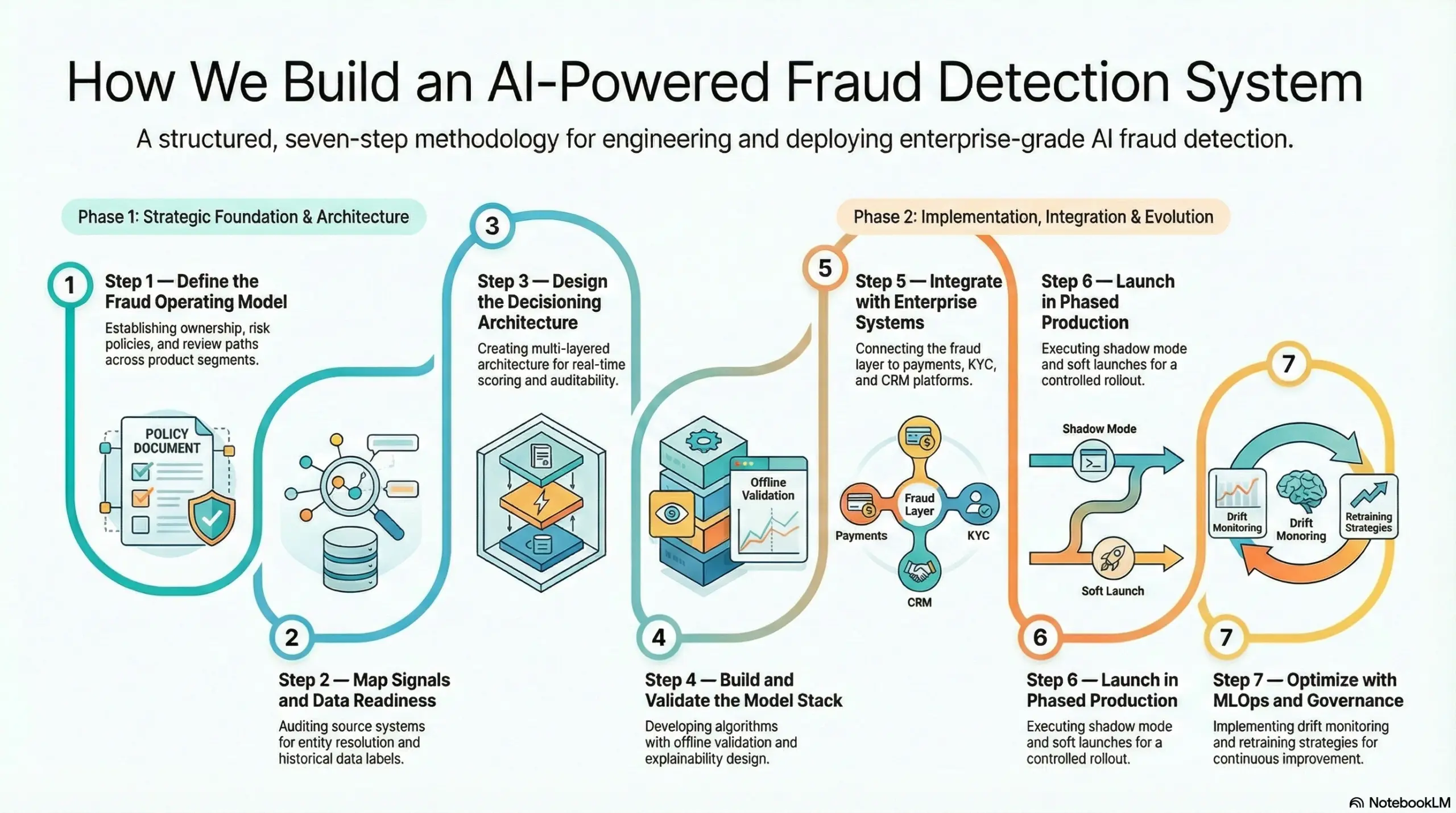
Step 1 — Define the Fraud Operating Model
Before writing a single line of code, we establish the strategic foundation of your system. This involves defining clear ownership and risk policies across your different product segments.
- Risk Policies. We set the specific business thresholds for automated actions.
- Review Paths. Our team maps out exactly how suspicious cases move from the AI to your human analysts.
- Channel Segmentation. We tailor the detection logic to the unique risks of each payment channel. This phase ensures that the AI serves your specific operational needs from day one.
Step 2 — Map Signals and Data Readiness
A model is only as good as the data it consumes. We perform a deep audit of your source systems to ensure high event quality.
- Entity Resolution. We identify how to link disparate data points into a single customer profile.
- Historical Labels. Our team cleans and prepares your past fraud data for model training.
- Data Gaps. We identify and fill any holes in your current telemetry or third-party risk signals. Consequently, your system starts with a clean and comprehensive view of your data environment.
Step 3 — Design the Decisioning Architecture
We build a multi-layered architecture that balances real-time scoring with traditional rules. This ensures that you have both the nuance of AI and the safety of hard policy constraints.
- Real-Time Scoring. Designing for sub-second latency across all transaction types.
- Fallback Logic. Ensuring the system remains secure even if a specific data source becomes unavailable.
- Auditability. Building in the “why” behind every decision for future regulatory reviews. Therefore, your architecture remains robust under the pressure of high-volume global commerce.
Step 4 — Build and Validate the Model Stack
This is where we develop the specific algorithms that will power your detection. We use a “champion-challenger” approach to ensure only the most accurate models reach production.
- Baseline Models. Establishing a performance standard using your historical data.
- Offline Validation. Testing new models against past fraud events to verify their accuracy.
- Explainability Design. Ensuring that every risk score can be translated into a human-readable justification. In addition, we calibrate your rules to minimize false positives while maximizing detection rates.
Step 5 — Integrate with Enterprise Systems
A fraud system must communicate perfectly with your core infrastructure. We build secure integrations with your payments, KYC, and CRM platforms.
- API Orchestration. Connecting the fraud layer to your real-time payment rails.
- Ops Tools. Feeding alerts directly into the dashboards your analysts already use.
- Data Platforms. Ensuring that fraud outcomes are archived for long-term trend analysis. This connectivity ensures that risk management becomes a seamless part of your daily operations.
Step 6 — Launch in Phased Production
We avoid the risks of a “big bang” launch by using a controlled rollout strategy. This allows us to fine-tune the system using real-world data without impacting your entire user base.
- Shadow Mode. Running the AI in the background to compare its decisions with your current system.
- Soft Launch. Rolling out the new engine to a small segment of your transactions.
- Threshold Tuning. Adjusting risk levels based on live feedback from your analysts. Consequently, you can transition to the new system with total confidence in its performance.
Step 7 — Optimize with MLOps and Governance
The final step is ensuring your system stays sharp as threats evolve. We implement a full MLOps framework for continuous monitoring and improvement.
- Drift Monitoring. Automatically flagging when model accuracy begins to change.
- Retraining Strategy. Establishing a schedule for updating models with the latest fraud labels.
- Incident Handling. Creating clear protocols for responding to new, large-scale attack patterns. Therefore, your investment remains a cutting-edge asset for years to come.
Building this entire machine requires a partner who understands the full lifecycle of enterprise technology. At Intellivon, we deliver the pipelines, orchestration, and governance that turn AI into a reliable business shield.
Cost Of Building An AI-Powered Fraud Detection System
At Intellivon, AI-powered fraud detection systems are built as governed risk infrastructure, not as scoring tools layered onto transaction systems. The focus stays on creating environments that operate reliably across payment flows, user behaviors, and evolving fraud patterns. Every architectural decision considers detection accuracy, decision speed, explainability, and long-term operational resilience from the start.
When budget constraints exist, scope can be refined thoughtfully. However, core elements such as behavioral intelligence, real-time scoring, decision transparency, and regulatory readiness are never compromised. As a result, enterprises avoid costly redesigns that typically surface after deployment. Stability improves, and long-term fraud resilience remains protected.
Estimated Phase-Wise Cost Breakdown
| Phase | Description | Estimated Cost Range (USD) |
| Fraud Discovery & Risk Mapping | Fraud pattern analysis, transaction review, exposure assessment | $6,000 – $12,000 |
| Data Preparation Layer | Transaction signals, behavioral inputs, normalization | $8,000 – $18,000 |
| AI Risk Model Development | Behavioral modeling, anomaly detection logic | $10,000 – $25,000 |
| Real-Time Decision Engine | Risk scoring and response orchestration | $8,000 – $20,000 |
| System Integrations | Payment rails, identity systems, transaction flows | $6,000 – $15,000 |
| Governance & Explainability | Audit trails, decision transparency, and oversight controls | $5,000 – $12,000 |
| Fraud Policy Engine | Rule overlays and escalation pathways | $4,000 – $10,000 |
| Monitoring & Alert Framework | Case triggers, investigation support | $4,000 – $8,000 |
| Testing & Performance Validation | Accuracy checks, latency validation | $3,000 – $7,000 |
| Deployment & Optimization | Cloud setup, tuning, and monitoring | $4,000 – $8,000 |
Total initial investment: $58,000 – $135,000
Ongoing maintenance and optimization: 15–20% of initial build annually
Hidden Costs Enterprises Should Plan For
Even well-scoped fraud programs can experience pressure when indirect cost drivers are overlooked. Planning for these early helps protect operational performance as transaction volume grows.
- Fraud patterns evolve and require ongoing model tuning
- Compliance expectations increase across jurisdictions
- Investigation workflows may expand with volume
- Integration complexity rises as platforms scale
- Behavioral monitoring needs grow with new user segments
- Governance requirements mature over time
Because of this, effective cost planning always extends beyond the initial build.
Best Practices to Avoid Budget Overruns
Based on Intellivon’s experience delivering enterprise risk platforms, several patterns consistently support predictable outcomes.
- Define fraud exposure clearly before building detection layers
- Embed behavioral intelligence into the core architecture
- Use modular AI models that evolve with transaction growth
- Align fraud policy with operational workflows early
- Maintain strong visibility across detection decisions
- Design for regulatory evolution rather than static compliance
Enterprises that follow these principles typically avoid expensive redesign cycles that slow fraud initiatives.
Request a tailored proposal from Intellivon’s enterprise risk specialists to receive a delivery roadmap aligned with your fraud exposure, transaction environment, and long-term security strategy.
Real Examples Of AI Fraud Detection Systems
Examining the infrastructure of global financial leaders reveals consistent architectural patterns. These platforms do not rely on a single defensive layer. Instead, they combine massive datasets with real-time machine learning to stay ahead of sophisticated threats.
By studying these systems, enterprise leaders can understand the standard for high-performance risk management. Specifically, these examples demonstrate how AI-powered fraud detection functions at a global scale.
1. Stripe Radar
Stripe Radar is built directly into the payment flow to provide a risk score for every transaction. It leverages network-scale intelligence trained on over 1 trillion dollars in annual volume.
- Network Effects. The system learns from data across millions of global companies.
- Customization. Users can set specific rules to supplement the AI scoring.
- Outcome. This combination reportedly reduces fraud by an average of 38% for its users. The key lesson here is the value of combining automated model scoring with highly configurable controls.
2. Adyen RevenueProtect
Adyen focuses on a unified risk evaluation process where every transaction undergoes immediate scrutiny. Their latest risk engine uses global transaction data to classify threats before authorization occurs.
- ML Classification. Each event is mapped against known fraud markers in real time.
- Threshold Logic. The system uses a mix of block and review triggers based on risk levels. This example shows that strong decision orchestration matters just as much as the underlying model.
3. Feedzai
Feedzai provides a single AI-powered risk platform that scores transactions across multiple channels in real time. This unified approach is particularly valuable for enterprises operating across different geographies.
- Cross-Channel Coverage. It monitors risk across various payment types and digital touchpoints.
- Unified Intelligence. A single platform handles the complexities of diverse global markets. Enterprise buyers clearly value a unified view of risk that eliminates fragmented data silos.
4. Revolut’s Sherlock
Revolut developed a custom card fraud monitoring system called Sherlock that evaluates transactions in under 50 milliseconds. The system is designed for extreme speed and high-frequency retraining.
- Rapid Response. The engine triggers automated block or freeze workflows instantly.
- Feedback Loops. It uses user confirmation loops to verify suspicious activity via the mobile app. The success of Sherlock proves that speed plus integrated user confirmation loops significantly improve overall security outcomes.
These platforms represent the gold standard for modern financial security. They prove that an integrated, AI-first architecture is the only way to protect a high-growth fintech ecosystem.
Conclusion
Moving from traditional rules to an AI-powered fraud detection system is a strategic shift. This investment does more than just lower your risk of financial loss. It turns security into a powerful growth engine for your enterprise. By automating complex decisions, you can reduce friction for your customers while protecting your reputation across global markets.
At Intellivon, we specialize in building these high-performance AI solutions for the fintech sector. We engineer the data pipelines and orchestration layers that make your organization resilient. Our team ensures that your security scales seamlessly alongside your business goals.
Build an AI-Powered Fraud Detection System With Intellivon
Intellivon delivers governed, AI-driven fraud detection systems built for enterprise fintech environments. By combining behavioral intelligence with real-time decision infrastructure, we help organizations detect fraud without slowing legitimate transactions.
The result is a scalable, audit-ready risk framework that protects revenue while maintaining customer trust.
Why Partner With Intellivon?
Choosing the right partner to build your fraud detection system is a strategic decision. We focus on the core pillars of enterprise-grade fraud resilience to support long-term operational stability.
- Governance-First Architecture: Detection systems are designed where policy drives the technology. As a result, your internal fraud controls and risk tolerance are embedded directly into automated decision logic.
- Behavioral Intelligence Models: Fraud rarely follows static patterns. Therefore, our AI models analyze behavioral signals and transaction context to identify threats beyond traditional rule-based systems.
- Real-Time Decision Infrastructure: Speed matters in financial transactions. Specifically, we build systems that assess risk instantly without introducing latency into payment or onboarding flows.
- Configurable Fraud Policies: Risk tolerance varies across markets and products. Consequently, our platforms allow you to adapt fraud policies across regions, user types, and transaction scenarios.
- Provider-Agnostic Integrations: Enterprises often operate across fragmented systems. Instead of locking you into one vendor, we integrate fraud signals across payment rails, identity tools, and data sources.
- Enterprise-Grade Explainability: Regulatory clarity is essential. Every automated fraud decision is supported by transparent reasoning and traceable audit logs.
- Scalable Monitoring: Fraud patterns evolve continuously. Our infrastructure supports ongoing monitoring and adaptive model tuning as your transaction volume grows.
Intellivon provides the technical depth and strategic foresight required to manage fraud risk at enterprise scale. By aligning AI intelligence with governance controls, we help you strengthen protection without disrupting growth.
Book a strategy call with Intellivon to design an AI-powered fraud detection system aligned with your transaction environment, risk exposure, and long-term operational goals.
FAQs
Q1. How does AI improve fraud detection in fintech?
A1. AI analyzes massive datasets in real time to spot subtle behavioral shifts. Unlike static rules, machine learning adapts to new attack patterns. This proactive approach identifies fraud before transactions settle.
Q2. What data is needed to build an AI fraud detection system?
A2. Effective systems require transaction details, device telemetry, and IP geolocation data. In addition, incorporating KYC records and historical dispute labels helps the models differentiate between legitimate users and sophisticated criminals.
Q3. Can AI reduce false positives in payment fraud prevention?
A3. Yes. AI understands the nuance of individual customer spending habits. Consequently, it can reduce false positive alerts by up to 75%. This ensures that honest customers experience zero friction.
Q4. Should fintech companies build or buy a fraud detection platform?
A4. Buying offers speed for standard needs. However, large enterprises often build custom layers to handle unique data structures. This allows for deeper integration with legacy core banking and payment systems.
Q5. How long does it take to build an enterprise fraud detection solution?
A5. A production-ready MVP typically takes three to six months to develop. This timeline includes data mapping, model training, and shadow-mode testing. Full-scale global deployment often requires additional phased rollouts.