Financial fraud is costing the global economy billions every year, and the figures keep rising. Today, fraudsters work quickly, in coordination, and increasingly use automation. Old rule-based systems were designed for a different time. This is because they identify what they already know, while everything unknown slips through unnoticed. For financial institutions that handle high transaction volumes, complex customer networks, and increasing regulatory pressure, this gap has a high cost.
AI fraud detection agents change this situation. Unlike traditional systems, they learn and respond in real time. They can detect unusual patterns across millions of data points before damage escalates. However, using them effectively in a business environment involves more than just installing a model. It requires clear structure, specialized training, and deep integration that most ready-made tools do not provide.
At Intellivon, we create AI agents designed for high-stakes environments, such as financial fraud detection. This blog explains everything that we have adapted to and learned through our years of hands-on experience in building AI agents for fraud detection for enterprises.
Why Fraud Detection Needs AI Agents Today
Banks are adopting AI agents for fraud detection as threats grow more complex, including deepfakes and synthetic identities rising sharply in recent years.
Traditional rule-based systems struggle to keep up. In contrast, AI agents analyze transactions in real time, understand context, and operate at scale, helping financial institutions respond faster to evolving fraud patterns.
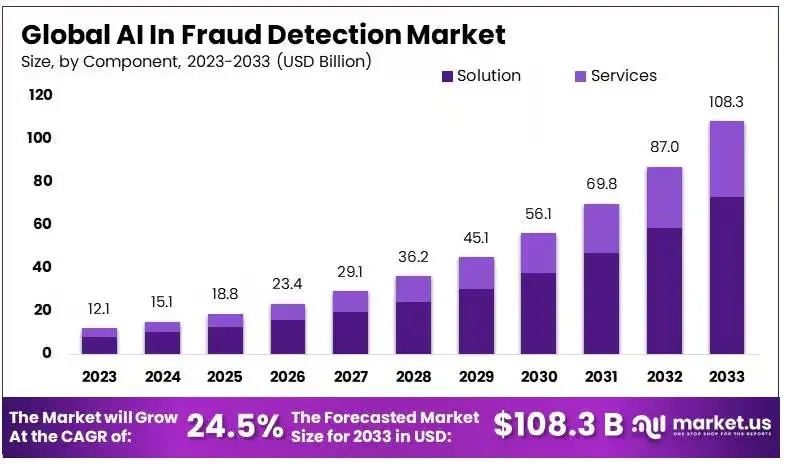
The AI fraud detection market is growing rapidly. It is projected to rise from USD 12.1 billion in 2023 to around USD 108.3 billion by 2033. This reflects a strong CAGR of 24.5% over the forecast period, driven by increasing fraud complexity and demand for real-time detection systems.
Legacy systems are currently struggling to keep pace with sophisticated financial crime. At the same time, traditional infrastructure relies on rigid parameters that simply cannot adapt to the speed of modern digital transactions.
1. Real fraud patterns legacy systems miss
Legacy systems often overlook “low and slow” attacks and synthetic identity fraud. These methods involve small, seemingly normal transactions or fabricated personas that do not trigger standard alarms.
Because these patterns mimic legitimate user behavior over long periods, they bypass filters designed to catch obvious spikes. For example, a fraudster might spend months building a credit profile for a non-existent person before executing a large-scale theft.
2. Limits of rule-based fraud detection models
Rule-based models operate on “if-then” logic, which is inherently reactive and inflexible. These systems require manual updates every time a new threat emerges, creating a dangerous lag between discovery and protection.
Furthermore, they produce high rates of false positives, which frustrate honest customers and increase operational costs for manual reviews.
3. Why static ML models fail in real-time fraud
Static machine learning models are trained on historical data, making them ill-equipped for “zero-day” fraud tactics. While they are better than rules, they still lack the ability to learn from data as it arrives.
In a real-time environment, a model that hasn’t been updated in weeks is effectively blind to emerging trends.
4. Shift from detection systems to decision agents
The industry is moving toward autonomous agents that do more than just flag suspicious activity. These agents evaluate context, cross-reference multiple data points, and make millisecond decisions to block or clear transactions.
This shift changes fraud prevention from a passive observation post into an active, self-improving defense layer.
Modern finance requires a proactive stance that only autonomous AI agents can provide. Transitioning to these intelligent systems is no longer a luxury but a fundamental requirement for institutional security.
What Are AI Agents in Fraud Detection Systems?
AI agents in fraud detection are autonomous systems that analyze transactions, user behavior, and contextual signals to identify and act on suspicious activity in real time. Unlike static models, they make decisions, trigger actions, and continuously adapt to new fraud patterns.
These agents operate across financial systems, combining data, risk logic, and workflows to detect, prevent, and respond to fraud without constant manual intervention.
Difference Between AI Models and AI Agents
AI models and AI agents are often used interchangeably, but they serve very different roles in fraud detection systems. Understanding this difference is critical when designing enterprise-grade solutions.
One predicts risk while another takes the action. This shift changes how fraud systems operate across financial workflows.
Comparison: AI Models vs AI Agents
| Aspect | AI Models | AI Agents |
| Core Role | Predict fraud risk or anomalies | Make decisions and take actions |
| Function | Analyze data and generate outputs | Execute workflows based on outputs |
| Autonomy | Limited, requires a human or system trigger | High, can act independently |
| Scope | Single task, such as risk scoring | End-to-end process handling |
| Adaptability | Retrained periodically | Continuously learns and adapts |
| Integration | Works within a system | Orchestrates across multiple systems |
| Example | Flagging a suspicious transaction | Blocking the transaction and alerting the team |
AI models are essential for identifying potential fraud. However, they stop at prediction. AI agents extend this capability by acting on those insights in real time. As a result, enterprises move from passive detection to active fraud prevention, reducing response time and operational dependency.
Role of Autonomy in Fraud Decision Systems
Fraud detection no longer operates on delayed reviews or manual escalation. As transaction volumes increase, systems must respond instantly and consistently. This is where autonomy becomes critical.
Instead of waiting for human intervention, autonomous systems evaluate risk, make decisions, and trigger actions in real time. As a result, financial operations move faster while maintaining control and accuracy.
1. Real-Time Decision Making Without Delays
Autonomous systems assess transactions the moment they occur. They analyze multiple signals, assign risk, and act within milliseconds. Therefore, suspicious activity can be blocked before damage happens, not after.
2. Consistent Decisions Across High Volumes
Manual reviews often lead to inconsistencies, especially under pressure. Autonomous systems apply the same logic across every transaction. In addition, they reduce dependency on individual judgment, ensuring uniform fraud handling at scale.
3. Reduced Operational Burden on Fraud Teams
Fraud teams spend significant time reviewing alerts and false positives. Autonomous systems handle repetitive decisions automatically. As a result, teams can focus on complex investigations that require human expertise.
4. Continuous Learning From New Fraud Patterns
Fraud evolves quickly. Autonomous systems learn from new data, feedback loops, and outcomes. Therefore, they adapt their decision logic over time, improving detection accuracy without constant manual retraining.
Autonomy shifts fraud detection from reactive processes to proactive decision systems. It enables faster responses, consistent outcomes, and scalable operations. For enterprises, this means stronger fraud prevention while reducing operational strain and improving overall efficiency.
Types of AI Agents Used in Fraud Detection
Specialized AI agents serve as the frontline defense by handling specific segments of the financial ecosystem. These autonomous units work in tandem to create a comprehensive security web that traditional software cannot replicate.
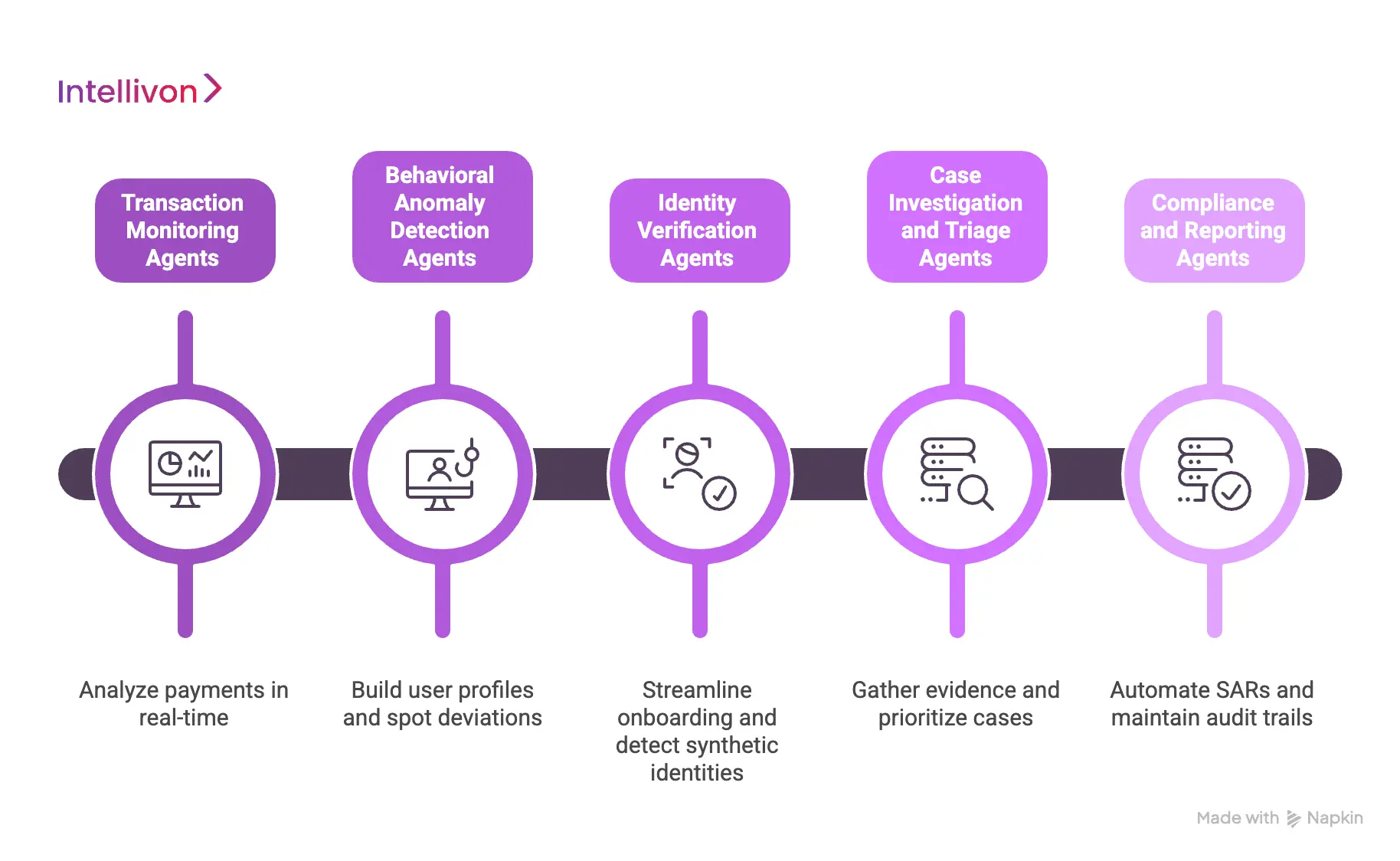
1. Transaction Monitoring Agents
Transaction monitoring agents analyze payments as they happen to stop theft before funds leave an account. These agents look beyond simple dollar amounts to evaluate geographic consistency, merchant risk, and velocity.
For instance, if a card is used in two different cities within minutes, the agent intervenes immediately. This real-time processing ensures that high-speed digital transfers remain secure without slowing down the user experience.
2. Behavioral Anomaly Detection Agents
These agents focus on the “how” rather than the “what” by building a unique profile for every user. They monitor keystroke dynamics, mouse movements, and typical login times to spot account takeovers.
If a user suddenly switches from a mobile app to a desktop at 3 AM, the agent notes the deviation. Consequently, even if a criminal has valid credentials, the agent can block access based on irregular behavior.
3. Identity Verification Agents
Identity agents streamline the onboarding process while weeding out sophisticated synthetic identities and deepfakes. They use computer vision to verify government IDs and match them against real-time biometric scans.
Additionally, they cross-reference external databases to ensure the social footprint of an applicant is legitimate. This reduces the burden on human teams during high-volume periods.
4. Case Investigation and Triage Agents
When a red flag is raised, these agents act as digital detectives to gather all necessary evidence for human reviewers. They aggregate data from past transactions, social media, and credit bureaus into a single report.
By prioritizing cases based on potential loss, they ensure investigators focus on the highest-risk threats first.
5. Compliance and Reporting Agents
These agents automate the tedious task of filing Suspicious Activity Reports (SARs) and maintaining audit trails. They ensure that every action taken by the AI system is documented and explainable to regulators.
Therefore, firms can stay compliant with evolving laws like AML and KYC without increasing their headcount.
By deploying these diverse agents, institutions can move from a broad, ineffective net to a precision-guided defense. This modular approach allows for rapid scaling as the business grows and new threats emerge.
How AI Agents Detect Fraud Step by Step
Modern AI agents function through a systematic pipeline that converts raw data into decisive security actions. This process happens in milliseconds, ensuring that protection never compromises the speed of global finance.
1. Data ingestion from financial systems
The process begins by pulling data from diverse sources like core banking platforms, mobile apps, and external credit feeds. Agents handle structured data, such as transaction amounts, alongside unstructured data, like device fingerprints or IP addresses.
Because the system is built for high-volume environments, it can ingest millions of data points simultaneously without causing latency. This creates a unified view of the customer’s activity across all digital touchpoints.
2. Real-time feature extraction pipelines
Once data is collected, the agent extracts “features” or specific indicators that define a transaction’s risk profile. It compares the current activity against historical patterns, such as the user’s average spend or typical login location.
For example, the system might calculate the distance between the last two transactions to check for “impossible travel.” These pipelines transform raw numbers into meaningful insights that the AI can interpret immediately.
3. Risk scoring and anomaly detection logic
The agent then applies complex logic to assign a risk score to the event. This score isn’t based on a single factor but on the intersection of hundreds of variables analyzed through neural networks.
If the score crosses a specific threshold, the transaction is flagged as an anomaly. This stage is critical because it separates genuine mistakes, like a forgotten password, from malicious intent.
4. Decision-making and action triggers
After scoring, the agent executes a pre-defined action based on the level of threat. Low-risk actions might involve sending a push notification, while high-risk scenarios trigger an immediate account freeze.
The agent communicates directly with the payment gateway to approve, decline, or initiate several steps of authentication. Consequently, the enterprise stops fraud at the source before any financial loss occurs.
5. Feedback loops and model retraining
The final step involves learning from the outcome of every decision. If a human investigator marks a flagged transaction as legitimate, the agent updates its internal logic to avoid similar mistakes in the future.
This continuous feedback loop ensures the system evolves alongside changing fraud tactics. Therefore, the defense becomes stronger and more accurate with every transaction it processes.
This structured approach allows enterprises to automate the entire lifecycle of fraud prevention. By following these steps, organizations move from reactive manual reviews to a proactive, self-sustaining security architecture.
Key Features of Enterprise Fraud AI Agents
Enterprise-grade AI agents are defined by their ability to handle massive data loads while maintaining the transparency required by global regulators. These features ensure that security scales alongside business growth without creating operational bottlenecks.
1. Real-time fraud detection at scale
High-growth enterprises process thousands of transactions per second, leaving no room for manual intervention or slow processing. AI agents operate with sub-second latency, evaluating every packet of data against complex risk profiles instantly.
This speed prevents “transaction friction,” ensuring that legitimate customers enjoy a seamless experience while criminals are blocked in their tracks. Consequently, the organization can expand its volume without needing to increase the size of its security team.
2. Cross-channel fraud visibility
Fraudsters often exploit gaps between mobile apps, web portals, and physical branches. AI agents break down these silos by aggregating data across every touchpoint to identify coordinated attacks.
For instance, an agent can link a suspicious login on a laptop to a password change made via a call center minutes earlier. This holistic view allows for a unified defense strategy that covers the entire customer journey.
3. Explainable AI for audit and compliance
Black-box models are a liability in finance, where regulators demand to know why a specific transaction was blocked. Modern agents utilize “Explainable AI” (XAI) to provide clear, human-readable justifications for every decision made.
Whether it is for internal audits or external regulatory inquiries, the system can point to specific data points that triggered an alarm. Therefore, the enterprise remains compliant with global standards while maintaining full transparency.
4. Adaptive learning from new fraud patterns
The greatest strength of an autonomous agent is its ability to learn from the environment without manual reprogramming. When a new fraud tactic emerges, the agent identifies the subtle shift in data distribution and adjusts its parameters accordingly.
This self-healing nature reduces the “window of vulnerability” that typically exists between a new threat and a software patch. As a result, your defense remains current even against previously unseen “zero-day” attacks.
5. Automated case management workflows
When a high-risk event occurs, agents initiate a structured response. This includes gathering relevant evidence, notifying the affected user, and preparing the necessary documentation for a formal investigation.
By handling the repetitive “grunt work” of data collection, the agent allows human investigators to focus on high-level strategy and complex problem-solving. This automation significantly lowers the cost per investigation.
These core features transform fraud prevention from a back-office cost center into a strategic asset. By prioritizing speed, clarity, and adaptability, enterprises can protect their bottom line while fostering customer trust.
System Architecture for Fraud AI Agents
A robust architecture for fraud AI agents is built on a modular stack that ensures data flows seamlessly from the transaction point to the final decision. This structure allows for both the speed required for instant payments and the depth needed for complex risk analysis.
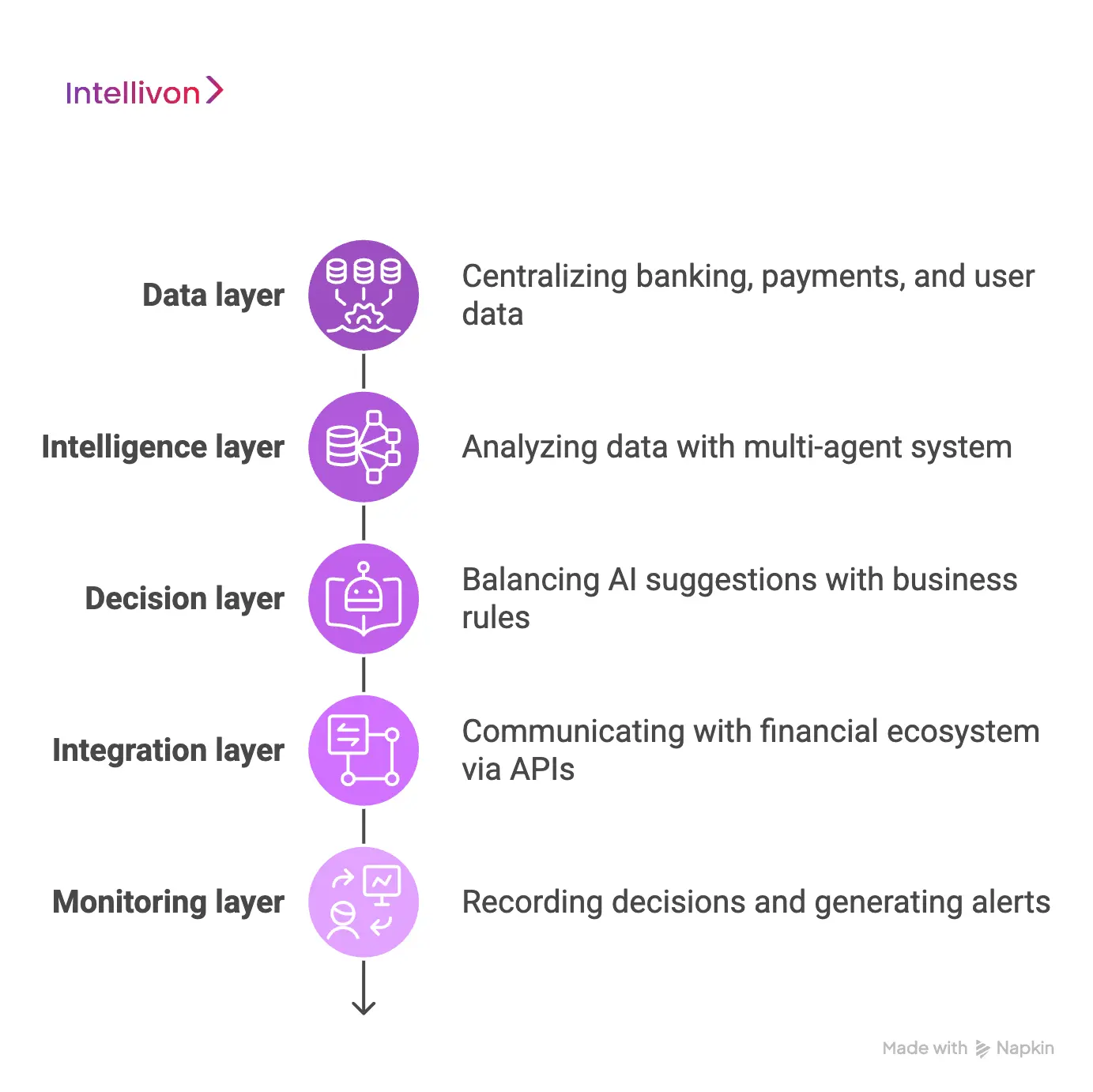
1. Data layer: banking, payments, user data
The foundation of the system is the data layer, which pulls information from core banking systems, payment gateways, and third-party databases. It handles a mix of structured transaction data and unstructured behavioral signals, such as device IDs or session duration.
By centralizing these diverse streams, the architecture creates a “single source of truth” for every customer. This deep visibility is essential for identifying patterns that span multiple accounts or platforms.
2. Intelligence layer: models and agents
This is where the actual analysis happens using a multi-agent system (MAS). Different agents specialize in specific tasks, such as scanning for social engineering or detecting automated bot attacks.
These agents use advanced machine learning to evaluate the data provided by the layer below. Because they work in parallel, they can process massive amounts of information without causing delays in the checkout process.
3. Decision layer: AI plus rule orchestration
The decision layer acts as the brain of the system, balancing the flexibility of AI with the strict requirements of corporate policy. While the AI suggests a risk level, the orchestration engine applies specific business rules, such as “block all transactions over a certain amount from high-risk regions.”
This hybrid approach ensures that the system is both smart and compliant with internal risk appetites. Consequently, the enterprise maintains human-oversight while benefiting from machine-speed execution.
4. Integration layer: APIs and external systems
To be effective, AI agents must communicate with the broader financial ecosystem through secure APIs. This layer allows the system to trigger external actions, such as sending a multi-factor authentication (MFA) request or querying a global blacklist.
It ensures that the fraud system is not an island but a connected part of the enterprise’s infrastructure. Therefore, the security response is coordinated across all relevant software and third-party services.
5. Monitoring layer: logs, alerts, audit trails
The monitoring layer provides the necessary oversight by recording every decision, data point, and system change. It generates real-time alerts for security teams and maintains comprehensive audit trails for regulatory compliance.
This transparency is vital for post-mortem analysis and for proving to auditors that the AI is operating within safe bounds. As a result, the enterprise can confidently defend its security posture during any external review.
By organizing the system into these distinct layers, enterprises can create a fraud defense that is both powerful and easy to maintain. This architectural clarity allows for faster updates and more reliable protection in a rapidly changing market.
Integrations Required for Fraud AI Systems
To maximize the effectiveness of AI agents, they must be deeply embedded in the existing financial infrastructure. Seamless integration ensures that data flows without friction, allowing the AI to act as a unified nervous system across the entire organization.
1. Core banking and payment systems
The most critical integration involves connecting AI agents directly to the core banking ledger and payment processing rails. This connection allows the system to pause or reverse transactions in real-time before they are settled.
By integrating with protocols like ISO 20022 or ACH networks, the agents gain immediate visibility into fund movements. Consequently, the enterprise can enforce security protocols at the very point of exchange, significantly reducing the window for successful theft.
2. KYC, AML, and identity verification tools
AI agents must communicate with Know Your Customer (KYC) and Anti-Money Laundering (AML) suites to ensure every user is legitimate. This integration allows the agent to pull identity scores, document verification results, and PEP (Politically Exposed Person) status during a transaction.
If a user’s risk profile changes, for instance, if they appear on a new sanctions list, the AI can automatically increase the scrutiny on their account. This creates a dynamic defense that responds to compliance risks as they happen.
3. Transaction monitoring platforms
While AI agents provide the intelligence, integration with traditional transaction monitoring platforms provides the operational framework. This allows the AI to “hand off” suspicious patterns to existing legacy systems that might still be required for certain regulatory filings.
It ensures that the new AI layer enhances, rather than replaces, the established compliance infrastructure. Therefore, the enterprise benefits from modern speed without losing the stability of its historical records.
4. External fraud intelligence data sources
No enterprise is an island, and integrating with external threat intelligence feeds is vital for staying ahead of global trends. These sources provide real-time data on compromised IP addresses, known fraudulent device fingerprints, and leaked credentials from the dark web.
By cross-referencing internal activity with these global blacklists, the AI agent can preemptively block attackers who have not yet targeted your specific firm. This collective intelligence turns individual defense into a shared network of security.
5. Case management and investigation tools
When the AI identifies a high-risk event, it must push that data into a case management system for human review. Integration ensures that all evidence is automatically attached to the ticket.
This eliminates the manual effort of gathering data from multiple screens, allowing investigators to make faster, better-informed decisions. As a result, the time from detection to resolution is slashed, protecting both the bank and the customer.
Strategic integration transforms isolated security tools into a cohesive, intelligent ecosystem. When these systems talk to each other, the enterprise gains the comprehensive oversight needed to defeat modern financial crime.
Data Requirements for Fraud AI Agents
High-quality data is the lifeblood of any autonomous fraud system. Without a structured and clean data pipeline, even the most advanced AI agents will struggle to distinguish between a loyal customer and a sophisticated attacker.
1. Transaction and behavioral data needed
To build a precise risk profile, agents require a mix of hard transaction data and “soft” behavioral signals. This includes basic details like the currency, amount, and merchant ID, alongside deeper metrics like device fingerprints and IP velocity.
Behavioral data adds a vital layer of context. For example, if a user who typically types slowly suddenly pastes a complex password, the agent can flag a potential account takeover.
2. Historical fraud data requirements
AI models need a robust library of past fraudulent and legitimate transactions to learn effectively. Ideally, an enterprise should provide at least 12 to 24 months of historical data to account for seasonal spending shifts and evolving attack vectors.
This “training ground” allows the agent to recognize the subtle markers that preceded previous breaches. Consequently, the system can predict future threats by identifying similar patterns before they result in a loss.
3. Data quality and labeling challenges
The biggest hurdle in AI deployment is “dirty” data, which is information that is duplicated, incorrectly formatted, or poorly labeled. If a past fraud instance was not correctly marked in the database, the AI might learn to treat that theft as a normal transaction.
Maintaining strict data hygiene involves regular audits and automated cleaning scripts to ensure the intelligence layer is learning from the truth. Therefore, investing in data engineering is just as important as the AI itself.
4. Handling incomplete or fragmented data
In the real world, data often has missing pieces, such as a hidden IP address or an unverified phone number. AI agents use “imputation” techniques to estimate missing values based on other available signals without stopping the analysis.
They can also cross-reference external identity bureaus to fill in the gaps in a user’s profile. This ensures that the decision-making process remains fluid and accurate, even when the incoming information is less than perfect.
By prioritizing these data requirements, enterprises provide their AI agents with the tools they need to succeed. A well-fed data layer is the difference between a system that guesses and one that knows.
Security and Compliance in Fraud AI Systems
Deploying AI agents within a financial framework requires a rigorous approach to data protection and regulatory alignment. For enterprise leaders, the goal is to build a system that is not only intelligent but also legally defensible and structurally sound.
1. Data privacy under GDPR and CCPA
AI agents must be designed with “privacy by design” to meet strict global standards like GDPR and CCPA. This involves anonymizing sensitive user information before it reaches the intelligence layer and ensuring that data is only used for the specific purpose of fraud prevention.
Because these laws grant users the “right to be forgotten,” the system architecture must allow for the surgical removal of individual data points without disrupting the broader model. Consequently, the organization avoids massive fines while maintaining consumer trust.
2. AML and fraud compliance requirements
Anti-Money Laundering (AML) regulations require systems to flag suspicious patterns that could indicate terrorism financing or shell company activity. AI agents automate this by scanning for “layering” and “integration” phases of money laundering that humans might miss.
They ensure that every high-risk transaction is cross-referenced against global sanctions lists in real-time. Therefore, the enterprise stays ahead of shifting legal mandates without needing to manually review every single account change.
3. Secure data pipelines and encryption
To prevent data breaches, the pipeline between the bank’s ledger and the AI agent must be secured with end-to-end encryption. Using protocols like TLS 1.3 and AES-256 ensures that even if data is intercepted, it remains unreadable to unauthorized parties.
Furthermore, “data-in-use” encryption allows the AI to perform calculations on encrypted sets, minimizing exposure during the processing phase. This technical layer is non-negotiable for protecting the integrity of the financial institution’s core assets.
4. Audit trails and explainability standards
Regulators often demand a “clear-box” view of why an AI agent blocked a specific transaction or froze an account. This requires a comprehensive audit trail that logs every feature used in a decision and the weight assigned to it.
By adopting explainability standards, the enterprise can provide human-readable reports to auditors within minutes. As a result, the “black box” problem is eliminated, turning AI decisions into verifiable business logic.
5. Model governance and risk controls
Ongoing governance ensures that the AI agent does not develop biases or “drift” from its intended purpose over time. This involves setting up automated risk controls that trigger a manual review if the agent’s behavior changes unexpectedly.
Regular “stress testing” of the models against simulated fraud attacks helps identify weaknesses before they are exploited in the real world. This proactive oversight keeps the system’s performance consistent and its risk profile within acceptable limits.
Security and compliance are the twin pillars that allow AI agents to operate at scale. By embedding these controls into the architecture, enterprises turn regulatory hurdles into a competitive advantage in the global market.
Challenges in Building Fraud AI Agents
Implementing advanced AI agents for fraud detection is a complex undertaking that requires balancing technical innovation with existing business processes. Addressing these hurdles early ensures that the system provides a high return on investment without disrupting core operations.
1. Data Quality and Fragmented Systems
The most common challenge is “dirty” or fragmented data spread across different departments and older databases. If an AI agent receives inconsistent information, it cannot accurately identify the subtle signs of a coordinated attack.
Organizations must often invest in data cleaning and unification to ensure the intelligence layer has a single, accurate view of each customer. This foundational work is essential because the AI is only as effective as the data it processes.
2. High False Positives and Alert Fatigue
Legacy systems often flag too many legitimate transactions, which creates “alert fatigue” for security teams and frustrates honest customers. If an AI agent is calibrated too strictly, it may block valid purchases, leading to lost revenue and a poor brand reputation.
The goal is to fine-tune the agent’s logic so it can distinguish between a rare but valid transaction and actual theft. Therefore, reducing false positives is a top priority for maintaining high customer satisfaction.
3. Real-time Processing at Scale
Fraud happens in milliseconds, meaning the AI must analyze every data point and make a decision without slowing down the payment process. As transaction volumes grow, the infrastructure must scale horizontally to prevent bottlenecks or system crashes.
Maintaining sub-second latency while running complex neural networks is a significant engineering feat that requires high-performance cloud environments. Consequently, the enterprise must ensure its hardware can keep up with its software’s intelligence.
4. Integration with Legacy Infrastructure
Many financial institutions still rely on “mainframe” systems that were built decades ago and do not easily communicate with modern AI. Bridging the gap between these old records and new autonomous agents requires custom API layers and middleware.
If the integration is not seamless, the AI may miss critical historical context, making its predictions less accurate. As a result, a phased approach to integration is often the most stable path forward.
5. Regulatory Constraints on AI Decisions
Financial regulators require that every automated decision be explainable, which can be difficult with complex “black box” models. If an AI agent cannot justify why it blocked a specific account, the firm could face legal challenges or compliance audits.
Building “interpretable” AI ensures that every action is backed by a clear trail of evidence that a human auditor can understand. Therefore, compliance must be built into the code, not added as an afterthought.
Navigating these challenges requires a strategic mindset and a focus on long-term scalability. By solving these technical and regulatory issues, an organization can turn its fraud department into a highly efficient defense center.
How We Solve Fraud AI Implementation Challenges
To move from pilot to production, enterprises must adopt a structured approach that prioritizes integration and scalability. We solve these common roadblocks by building a specialized environment where AI agents can operate safely alongside existing financial systems.
1. Unified data architecture approach
The first step in our solution is creating a “Banking OS” or a unified data layer that breaks down internal silos. Instead of letting credit card data, checking accounts, and mortgage records live in separate systems, we aggregate them into a single, clean format.
This gives AI agents the full context they need to make accurate risk assessments across the entire customer profile. By providing a “single source of truth,” we eliminate the data fragmentation that typically leads to missed fraud patterns.
2. Hybrid AI plus rule-based systems
We believe that the future of fraud detection is not purely probabilistic AI, but a hybrid model that blends machine learning with rigid business logic. While the AI agent identifies complex behavioral anomalies, the rule-based engine enforces “hard” compliance boundaries, such as mandatory blocks on specific high-risk regions.
This “Deterministic-Probabilistic Bridge” ensures that the AI plans the security strategy while the rules drive the execution. Consequently, the system remains smart enough to learn but predictable enough for institutional safety.
3. Scalable cloud-native infrastructure
To handle peak transaction volumes, such as during holiday sales or market volatility, we deploy agents on a cloud-native, multi-region architecture. Using technologies like Kafka for real-time event streaming and auto-scaling microservices, our systems maintain sub-100ms latency even under heavy load.
This infrastructure is designed for 99.99% uptime, ensuring that security never becomes a bottleneck for the business. Therefore, your organization can scale globally without worrying about system lag or manual sharding.
4. API-first integration strategies
Our implementation follows an API-first philosophy, allowing our AI agents to plug directly into your legacy cores without requiring a total system overhaul. By using secure webhooks and high-speed APIs, the agents can query external identity bureaus and internal ledgers in real-time.
This modular approach allows for rapid deployment, often within weeks rather than months, minimizing disruption to your ongoing operations. As a result, you get a modern defense layer that enhances your existing investment.
5. Built-in compliance and governance layers
We embed governance directly into the code by including automated audit trails and model monitoring tools from day one. Our systems provide human-readable explanations for every decision, ensuring you are always ready for an unannounced regulatory review.
We also implement continuous “control loops” that monitor for model drift, ensuring the AI stays within your established risk appetite. Therefore, the enterprise gains the efficiency of automation without sacrificing the oversight required by law.
By addressing the root causes of implementation failure, we turn a complex technical challenge into a repeatable business process. This strategy ensures that your investment in AI leads to measurable security gains and long-term operational stability.
How We Build Fraud AI Agents at Intellivon
At Intellivon, we follow a rigorous, engineering-first methodology to transform your existing security posture into a proactive, agentic defense. Our process is designed to minimize friction while maximizing the precision of every automated decision your system makes.
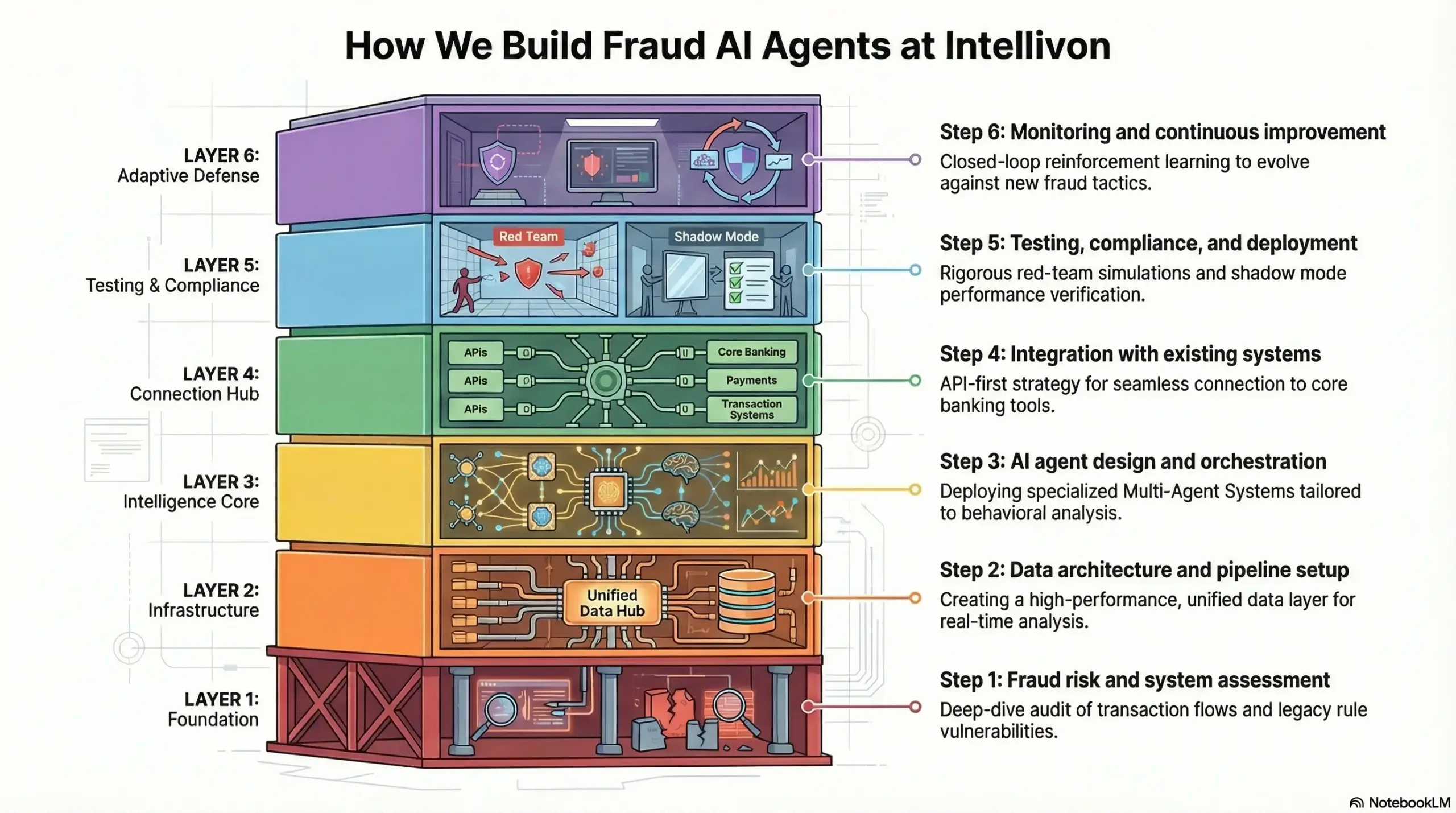
Step 1: Fraud risk and system assessment
We begin with a deep-dive audit of your current transaction flows, legacy rules, and historical breach data. Our specialists identify specific vulnerabilities, such as “low and slow” attacks or synthetic identity gaps that your current systems might miss.
This assessment allows us to map out a custom AI strategy that aligns with your specific risk appetite and business goals. Consequently, we ensure the foundation of the project is built on data-driven insights rather than generic assumptions.
Step 2: Data architecture and pipeline setup
Intelligence is only as good as the data feeding it, so we prioritize building a high-performance, unified data layer. We connect disparate sources, from core banking ledgers to mobile device pings, into a single, clean stream for the AI to analyze.
Our pipelines use real-time processing to ensure that every feature, like geo-velocity or biometric signals, is available for the agent in milliseconds. Therefore, your data moves from siloed storage to an active, liquid asset.
Step 3: AI agent design and orchestration
This is where we build the “brains” of the operation by deploying a Multi-Agent System (MAS) tailored to your needs. We design specialized agents for different tasks, such as one for behavioral analysis and another for cross-border payment verification.
These agents are managed by an orchestration layer that balances AI suggestions with your mandatory business rules. This hybrid approach ensures the system remains both creatively adaptive and strictly compliant with your policies.
Step 4: Integration with existing systems
We utilize an API-first integration strategy to plug our AI agents directly into your current infrastructure without requiring a “rip-and-replace” overhaul. Our team ensures seamless communication between the new intelligence layer and your core banking systems, KYC tools, and payment gateways.
By using secure webhooks and high-speed connectors, we ensure the agents can trigger actions, like blocking a card or requesting MFA, instantly. As a result, you gain cutting-edge protection while preserving your existing technology investments.
Step 5: Testing, compliance, and deployment
Before going live, we subject the agents to “red-team” simulations and rigorous stress tests against massive datasets. We ensure every model meets global explainability standards, providing clear audit trails for every decision made by the AI.
This phase includes a “shadow mode” deployment where the AI runs in the background to prove its accuracy against real-time traffic without affecting users. Consequently, when we finally flip the switch, the system is already proven and fully compliant with regulatory mandates.
Step 6: Monitoring and continuous improvement
Post-deployment, we implement a closed-loop monitoring system that tracks model performance and identifies “drift” in real-time. Our agents use reinforcement learning to stay updated on new fraud tactics, ensuring your defense evolves as fast as the criminals do.
We provide your team with detailed dashboards that highlight ROI, reduced false positives, and caught threats. Therefore, your fraud prevention becomes a self-improving engine that grows stronger with every transaction processed.
Our structured roadmap ensures that your transition to autonomous fraud detection is smooth, secure, and highly effective. At Intellivon, we build a resilient, future-proof security architecture.
Cost to Develop Fraud Detection AI Agents
Building AI agents for fraud detection is not a fixed-cost project. The total investment depends on how deeply the system integrates with payment systems, banking infrastructure, compliance layers, and fraud operations workflows.
Unlike standalone models, fraud detection agents operate within a real-time, multi-agent decision system. Therefore, costs are driven more by orchestration, integrations, and infrastructure than just model development.
1. Cost Breakdown by Modules and Complexity
| Component | Scope | Estimated Cost |
| Data Ingestion Layer | Transaction data, user behavior, device signals | $15,000 – $35,000 |
| Fraud Detection Agents | Anomaly detection, risk scoring models | $25,000 – $60,000 |
| Behavioral Analysis Agents | Pattern recognition, user profiling | $15,000 – $40,000 |
| Decision & Action Engine | Transaction blocking, alert triggers | $20,000 – $50,000 |
| Case Management System | Investigation workflows, alert handling | $15,000 – $35,000 |
| Monitoring & Feedback Systems | Model tracking, adaptive learning loops | $10,000 – $25,000 |
Fraud agents are built as part of a unified detection system, not isolated components. As a result, system design plays a critical role in overall cost.
2. Infrastructure and Integration Costs
| Component | Scope | Estimated Cost |
| Cloud Infrastructure (AWS/GCP/Azure) | Compute, storage, scaling | $10,000 – $25,000/year |
| Real-Time Data Pipelines | Streaming, event processing | $15,000 – $35,000 |
| API & Integration Layer | Banking systems, payment gateways, and KYC tools | $20,000 – $50,000 |
| Event-Driven Architecture | Real-time triggers and workflows | $15,000 – $40,000 |
A cloud-native, API-first setup ensures scalability and performance. However, costs increase with transaction volume and real-time decision requirements.
3. Security and Compliance Costs
| Component | Scope | Estimated Cost |
| Data Encryption & Access Control | PII protection, role-based access | $10,000 – $25,000 |
| Audit Logs & Explainability | Decision traceability for compliance | $8,000 – $20,000 |
| Regulatory Compliance Setup | AML, GDPR, regional regulations | $15,000 – $35,000 |
| Security Testing | Penetration testing, vulnerability scans | $8,000 – $15,000 |
Fraud systems operate in highly regulated environments. Therefore, compliance and security are core system requirements, not optional layers.
Hidden Costs Enterprises Often Miss
- Integration with legacy banking and payment systems
- Data normalization across fragmented financial sources
- Workflow redesign for automated fraud response
- Continuous model retraining and tuning
- Regulatory updates and audit requirements
These factors typically increase total project costs by 20–30%.
Estimated Total Cost Range
| Platform Scope | Estimated Cost |
| MVP (Single-Agent System) | $80,000 – $150,000 |
| Mid-Level Fraud Detection System | $150,000 – $300,000 |
| Enterprise Multi-Agent Platform | $300,000 – $400,000+ |
Most financial institutions underestimate fraud detection costs by focusing only on models. In reality, the majority of investment goes into integrations, real-time infrastructure, and compliance layers.
At Intellivon, fraud detection systems are built as financial infrastructure, not standalone tools. Therefore, they scale across channels, geographies, and regulatory environments without requiring constant rework.
Conclusion
Fraud detection is no longer a back-office function. It directly impacts revenue, trust, and operational scale. AI fraud detection agents enable faster decisions, reduce losses, and improve efficiency across systems.
Therefore, enterprises that invest early gain a measurable advantage. The focus should not be on tools, but on building a scalable decision infrastructure. With Intellivon, organizations can design systems that evolve with fraud and support long-term growth.
Build Fraud Detection AI Agents With Intellivon
At Intellivon, AI fraud detection agents are built as a financial risk infrastructure, not standalone models layered onto fragmented systems. The focus is to create a unified platform that connects data, risk intelligence, and execution across your entire fraud prevention workflow.
As a result, financial institutions reduce fraud losses, improve detection accuracy, and scale operations without increasing manual intervention.
Our engineering approach combines multi-agent architectures with API-first, cloud-native systems. This ensures seamless integration with core banking platforms, payment gateways, transaction monitoring systems, KYC/AML tools, and external fraud intelligence sources without disrupting ongoing operations.
Why Build With Intellivon
- Infrastructure-First Approach: We build systems that scale with your fraud operations, not short-term detection layers that fail under increasing transaction volumes.
- Built for Real Fraud Workflows: Every system is designed around how fraud detection, investigation, and response actually work within financial institutions.
- API-First, Integration-Ready Architecture: Seamless connectivity across banking systems, payment networks, and third-party tools without disrupting existing workflows.
- Compliance and Explainability Built In: Every decision is traceable, auditable, and aligned with global fraud and data protection regulations.
- Multi-Agent Orchestration at Scale: Coordinated AI agents detect, decide, and act across fraud scenarios while maintaining control and accuracy.
If you are planning to modernize your fraud detection systems, the next step is not adding another tool. It is building a decision system that scales with evolving fraud patterns.
Talk to Intellivon to design and deploy AI fraud detection agents tailored to your financial systems.
FAQs
Q1. What are AI agents in fraud detection?
A1. AI agents in fraud detection are autonomous systems that analyze transactions, user behavior, and contextual signals to identify suspicious activity in real time. Unlike traditional models, they do not just flag risks. They also take actions such as blocking transactions, triggering alerts, or initiating investigations. Therefore, they enable faster and more consistent fraud prevention across financial systems.
Q2. How long does development take?
A2. The development timeline depends on system complexity, integrations, and data readiness. A basic fraud detection system can take 8–12 weeks to build. However, enterprise-grade, multi-agent systems typically take 4–6 months. In addition, timelines may extend if legacy integrations or compliance requirements are complex.
Q3. What data is required for fraud AI?
A3. Fraud AI systems rely on multiple data sources to detect patterns accurately. This includes transaction data, user behavior, device information, and historical fraud records. In addition, external data such as credit signals or fraud intelligence feeds can improve detection. Clean, well-structured data significantly improves system performance and decision accuracy.
Q4. How accurate are AI fraud systems?
A4. AI fraud systems can achieve high accuracy when trained on quality data and deployed with proper feedback loops. They significantly reduce false positives compared to rule-based systems. However, accuracy depends on factors such as data quality, system design, and continuous learning. Therefore, ongoing monitoring and optimization are essential for maintaining performance.
Q5. How much does it cost to build?
A5. The cost to build AI fraud detection agents depends on system scale, integrations, and real-time processing needs. A basic system may cost between $80,000 and $150,000. Mid-level systems range from $150,000 to $300,000, while enterprise platforms can exceed $300,000. In addition, ongoing costs include infrastructure, maintenance, and model updates.