Digital wallets are now a fiduciary responsibility for enterprises with considerable digital assets. As digital assets move from balance sheet experiments to core treasury operations, the infrastructure holding them demands the same rigor your organization applies to any mission-critical financial system. Yet most enterprises discover too late that consumer-grade wallets and hastily integrated custody tools were never built to survive an institutional audit, let alone a regulatory inquiry.
The stakes are unambiguous, where a single architectural flaw in wallet design can mean irreversible asset loss. Developing an enterprise wallet platform requires a fundamentally different approach, one where security architecture, compliance frameworks, and operational scalability are not afterthoughts but founding principles.
At Intellivon, we build wallet infrastructure that enterprises can stake their reputation on. This blog will walk you through the architecture decisions and compliance imperatives that separate institutional-grade wallet systems from everything else on the market.
Why Enterprises Are Building Digital Wallet Infrastructure
Modern organizations are moving beyond simple transaction processing to own the entire financial experience. Building internal digital asset custody and wallet systems allows for deeper data integration and reduced dependency on third-party processors.
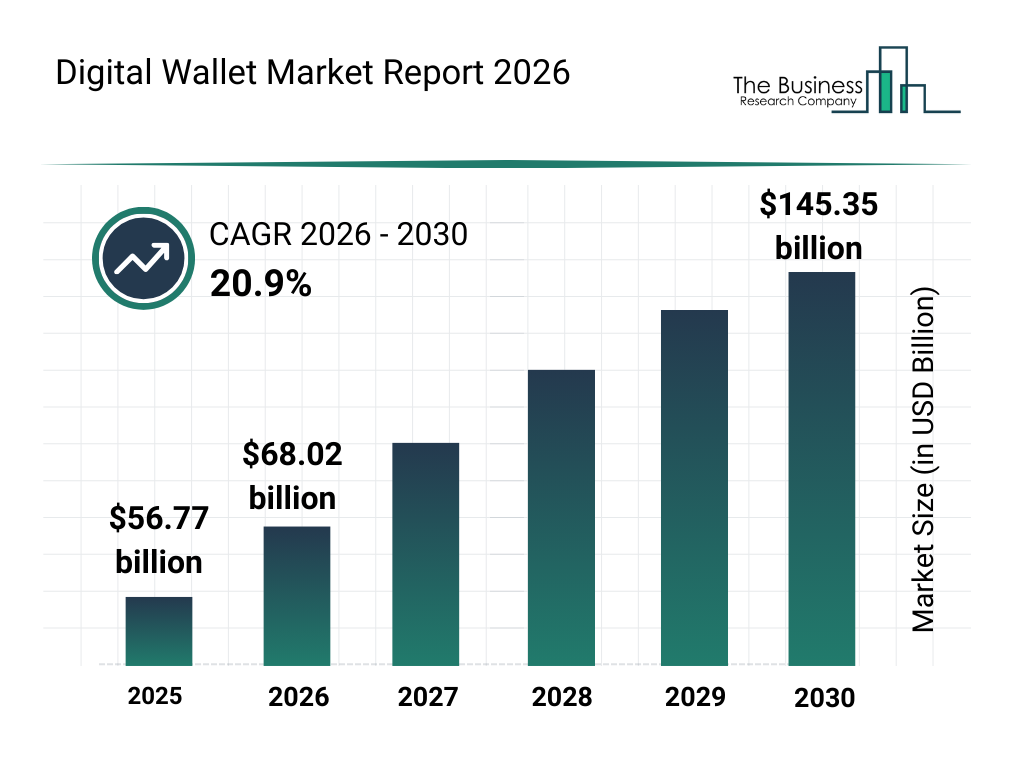
The global digital wallet market reached $56.77 billion in 2025. It is projected to grow to $145.35 billion by 2030. This reflects a 20.9% compound annual growth rate (CAGR). Growth is largely driven by the rise of embedded finance and the increasing demand for cross-border digital payments.
1. Shift From Payment Feature to Financial Infrastructure
Financial services were once considered a secondary feature for non-bank enterprises. Today, the architecture of a digital wallet is viewed as a core component of the corporate technology stack.
This shift occurs because businesses require a unified ledger to manage complex value flows across global borders. By internalizing this infrastructure, companies can automate reconciliation and reduce the friction associated with traditional banking rails.
2. Embedded Finance Is Driving Wallet Adoption
The rise of embedded finance has fundamentally changed how customers interact with brands. Organizations now integrate financial services directly into their existing product ecosystems to keep users within their environment.
Providing a native wallet experience increases user “stickiness” and creates a seamless path from intent to purchase. This integration allows a retail or logistics firm to act as a functional fintech provider without the overhead of a traditional bank.
3. Enterprise Control Over Payments and Stored Value
Managing stored value internally offers a significant strategic advantage regarding liquidity and fund oversight. Enterprises gain total transparency into transaction histories and user balances, which is often obscured when using external gateways.
This level of digital asset custody ensures that the organization maintains the “float” while providing instant settlement for internal transfers. It also empowers the business to set its own security parameters and risk thresholds.
How Wallet Platforms Unlock New Revenue Models
Custom wallet infrastructure enables sophisticated monetization strategies that are impossible with off-the-shelf payment tools.
Companies can launch tiered loyalty programs where rewards carry actual cash value or implement automated micro-payments for IoT-driven services.
These platforms also facilitate the creation of closed-loop ecosystems where transaction fees are eliminated for the user, but data value is captured by the enterprise.
What Is an Enterprise Wallet Platform?
An enterprise wallet platform is a financial infrastructure that allows organizations to store, manage, and transfer digital funds within a controlled system. It maintains wallet balances through a transaction ledger and supports payments, transfers, and integrations with banks or payment networks.
In addition, the platform includes identity verification, security controls, and compliance monitoring. As a result, enterprises can manage digital money flows safely while maintaining financial accuracy and regulatory oversight.
How Enterprise Wallets Differ From Consumer Wallet Apps
Enterprise wallet platforms serve a very different purpose from consumer wallet apps. Consumer wallets focus on convenience for individual users. They allow people to store cards, send money, and make everyday payments.
Enterprise wallets, however, function as financial infrastructure. They manage large volumes of transactions, maintain accurate ledgers, and support integrations with banks, payment networks, and internal financial systems.
The difference is not only in scale. Enterprise wallets are designed for financial accuracy, regulatory oversight, and operational control, while consumer wallets prioritize simplicity and user experience.
| Feature | Enterprise Wallet Platform | Consumer Wallet App |
| Primary Purpose | Manage enterprise funds and financial flows | Enable everyday payments for individuals |
| Ledger System | Full transaction ledger for financial accuracy | Basic balance tracking |
| Compliance | Built with KYC, AML, and audit requirements | Limited compliance controls |
| Integrations | Banks, payment rails, treasury systems | Mostly payment cards and peer transfers |
| Governance | Role-based access, approvals, and audit logs | Minimal administrative control |
| Transaction Volume | Designed for high-volume financial operations | Designed for personal transactions |
| Operational Reporting | Financial reporting and reconciliation tools | Limited user-level activity history |
In summary, consumer wallet apps are designed for convenience, while enterprise wallet platforms operate as regulated financial infrastructure. They support large-scale financial operations, enforce governance policies, and maintain the transaction integrity required by modern enterprises.
Wallet Infrastructure vs Payment Processing Platforms
Wallet infrastructure and payment processing platforms support digital transactions. However, they perform different roles.
A wallet platform manages stored balances and internal transfers, while a payment processor authorizes and routes payments across external networks.
| Feature | Wallet Infrastructure | Payment Processing Platform |
| Primary Role | Store and manage digital balances | Authorize and process payments |
| Core Component | Transaction ledger and wallet accounts | Payment gateway and processor connections |
| Fund Storage | Maintains stored value inside the system | Does not store balances |
| Transaction Type | Wallet transfers, balance updates, and funding | Card payments, bank transfers, settlements |
| Financial Control | Provides balance management and fund tracking | Focuses on payment authorization |
| Integrations | Banks, treasury systems, payment rails | Card networks, payment gateways, and banks |
| Enterprise Use Case | Digital wallets, stored value systems | Merchant payment acceptance |
In summary, wallet infrastructure manages funds within the platform, while payment processors move money across external financial networks. Together, they form the backbone of many enterprise payment systems.
Closed Loop vs Open Loop Wallet Systems
Enterprise wallet platforms can operate as closed-loop or open-loop systems. The difference depends on where the stored funds can be used. Closed-loop wallets restrict transactions within a specific platform or ecosystem. In contrast, open-loop wallets allow payments across external financial networks such as banks or card systems.
| Feature | Closed Loop Wallet | Open Loop Wallet |
| Usage Scope | Payments within a single platform or ecosystem | Payments across external financial networks |
| Payment Methods | Platform-specific payments or services | Cards, bank transfers, and external merchants |
| Fund Movement | Internal transfers within the system | Transfers inside and outside the platform |
| Infrastructure Complexity | Simpler infrastructure | More complex integrations required |
| Regulatory Requirements | Often lighter compliance requirements | Stronger regulatory oversight |
| Example Use Case | Marketplace credits or loyalty wallets | Digital banking or payment wallets |
In summary, closed-loop wallets focus on internal transactions within a controlled ecosystem, while open-loop wallets connect to broader financial networks, enabling wider payment capabilities.
Role of Wallets in Embedded Finance Ecosystems
The integration of wallet layers allows organizations to embed financial services directly into their existing product workflows.
This shift ensures that the enterprise captures every financial touchpoint, turning simple user interactions into long-term revenue streams.
1. Unified Value Storage for Multi-Sided Platforms
A centralized wallet acts as the primary ledger for all internal participants. By maintaining digital asset custody, platforms can facilitate instant transfers between buyers and sellers without waiting for external bank clearing.
This internal settlement reduces operational delays and simplifies the reconciliation of complex, high-volume transactions.
2. Seamless Monetization of Non-Financial User Journeys
Embedded wallets allow non-financial companies to offer services like instant credit or specialized insurance. This transformation turns operational tools into profit centers by capturing fees that previously went to third-party processors.
The enterprise also gains exclusive access to transaction data, which informs better product development and risk assessment.
3. Strategic Loyalty and Incentivization Engines
Integrated wallets replace static points systems with dynamic, programmable rewards. Organizations can distribute digital value that users spend immediately within the ecosystem, increasing retention and brand loyalty.
Because the business owns the infrastructure, it can adjust incentive structures in real time to respond to shifting market demands.
Core Architecture of an Enterprise Wallet Platform
Building a resilient wallet system requires a modular approach that separates value accounting from transaction execution.
This architecture ensures high availability while maintaining the rigorous security standards necessary for digital asset custody at scale.
1. Ledger Infrastructure and Balance Management
The ledger serves as the immutable record of all financial activity and account states. It must handle high-concurrency updates to ensure that balances remain accurate across global regions.
- Double-Entry Accounting: Ensures every credit has a corresponding debit for total financial integrity.
- Atomic Transactions: Prevents partial updates that could lead to balance discrepancies or double-spending.
2. Transaction Processing and Authorization Layer
This layer validates every request against pre-defined business logic and compliance rules. It acts as the gatekeeper to ensure only authorized movements of value occur.
- Velocity Checks: Automatically flags or blocks transactions that exceed specific frequency or volume limits.
- Multi-Factor Approval: Requires secondary verification for high-value transfers to mitigate internal and external fraud risks.
3. Identity, Account, and Wallet Management
Managing the relationship between users and their digital assets requires a sophisticated identity mapping system. This component links real-world entities to their specific sub-wallets and permission tiers.
- KYC/KYB Integration: Connects user profiles to verified identity documents for regulatory compliance.
- Hierarchical Wallets: Allows for the creation of master accounts with multiple sub-wallets for specific budget categories.
4. Payment Rails and Banking Integrations
To move value in and out of the ecosystem, the platform must interface with traditional and decentralized financial networks. These bridges allow for seamless fiat on-ramps and off-ramps.
- Swift/ACH Connectivity: Facilitates bulk transfers and payroll through standard legacy banking systems.
- Blockchain Gateways: Enable the settlement of stablecoins or other digital assets via direct network nodes.
5. API Layer for Wallet Access
The API layer exposes wallet functionality to internal applications and third-party partners. It must be designed for developer ease while maintaining strict security protocols.
- OAuth2 & JWT: Standardized authentication methods to ensure secure access for mobile and web clients.
- Webhooks: Provides third-party systems with immediate confirmation of successful transactions or account changes.
6. Event Streaming and Real-Time Notifications
Modern enterprises require instant visibility into ledger changes to trigger downstream workflows. Event-driven architecture ensures that users and systems remain synchronized.
- Kafka/RabbitMQ Integration: Pushes transaction data to analytics engines and fraud detection models in real time.
- Push Notifications: Send immediate alerts to end-users regarding deposits, withdrawals, or suspicious login attempts.
7. Security and Key Management Architecture
Protecting the cryptographic keys that authorize movement is the most critical aspect of digital asset custody. This layer isolates sensitive credentials from the rest of the application stack.
- Hardware Security Modules (HSM): Stores private keys in tamper-proof physical hardware to prevent digital theft.
- Multi-Party Computation (MPC): Splits keys into fragments so that no single party can ever access the full credential.
A robust architecture provides the foundation for trust and reliability in any financial product. By prioritizing these core modules, an organization can scale its financial operations without compromising on security or performance.
Wallet Types Enterprises Deploy Today
Choosing the right wallet architecture depends on the level of control and liability an organization is willing to assume.
Most modern frameworks for digital asset custody now support hybrid models to balance user experience with institutional security.
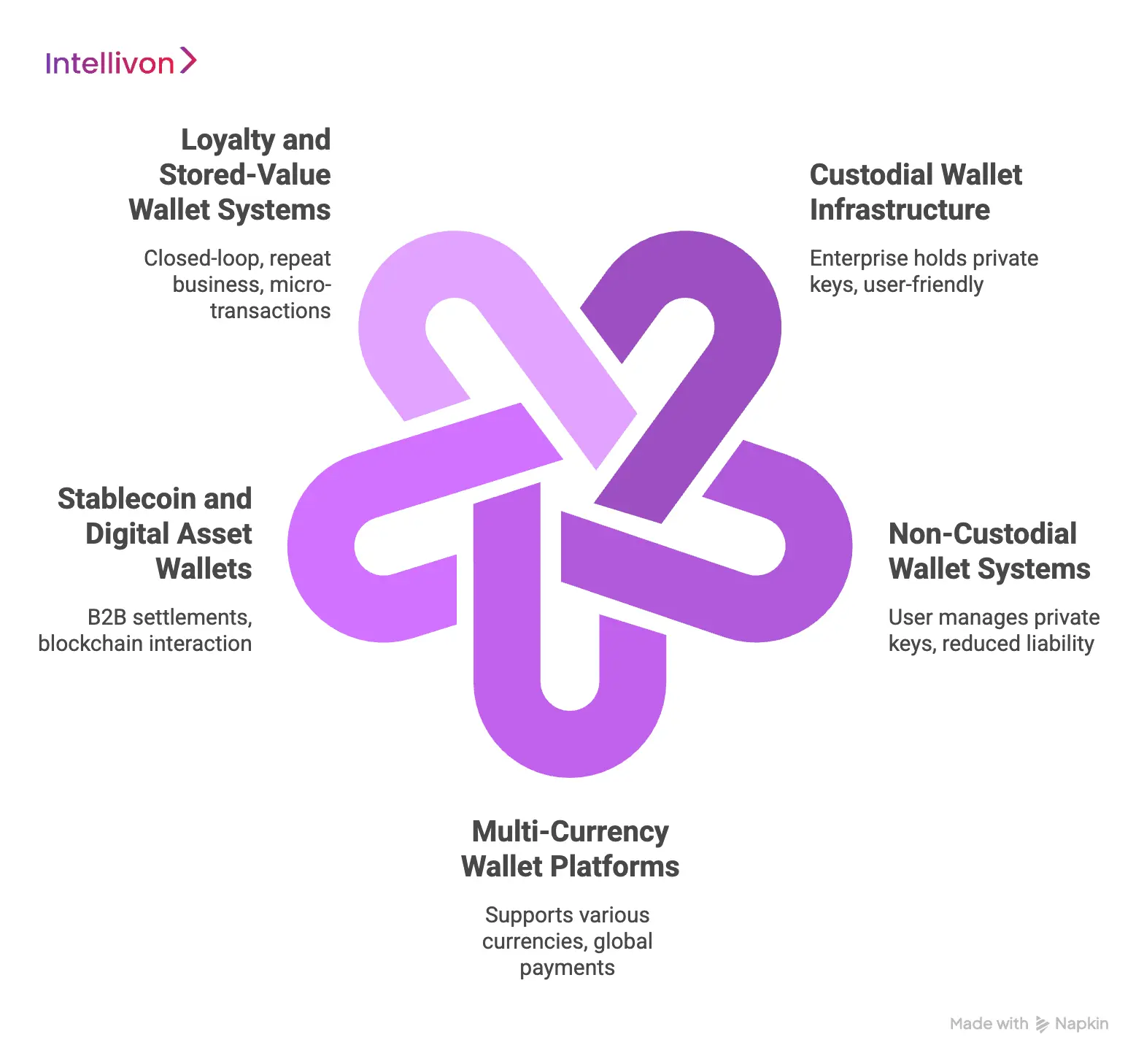
1. Custodial Wallet Infrastructure
In a custodial model, the enterprise holds the private keys and manages assets on behalf of its users. This approach offers the most user-friendly experience, as the organization can facilitate password recoveries and provide a familiar banking interface.
- Full Control: The enterprise maintains total oversight of fund movements and internal ledger balancing.
- Simplified UX: Users do not need to manage complex cryptographic keys or seed phrases to access their funds.
2. Non-Custodial Wallet Systems
Non-custodial systems shift the responsibility of key management directly to the end-user. This model is often preferred by privacy-conscious users and reduces the enterprise’s regulatory burden regarding the direct possession of funds.
- User Sovereignty: Customers have sole access to their assets, ensuring they remain in control even if the platform is offline.
- Reduced Liability: The business avoids the significant security risks associated with storing massive amounts of private key data.
3. Multi-Currency Wallet Platforms
These platforms are designed to hold and exchange various fiat and digital currencies within a single interface. They are essential for global enterprises that need to manage cross-border payments and reduce foreign exchange friction.
- Real-Time Conversion: Integrated liquidity providers allow users to swap currencies instantly at market rates.
- Global Reach: Supports localized payment methods across different geographic regions through a unified API.
4. Stablecoin and Digital Asset Wallets
Enterprises are increasingly using stablecoins for B2B settlements due to their speed and low transaction costs. These wallets are built to interact with blockchain networks while maintaining a peg to stable fiat currencies like the US Dollar.
- Instant Settlement: Bypasses traditional banking hours and intermediary banks for 24/7 value transfer.
- Programmable Money: Enables the use of smart contracts to automate escrow and conditional payouts.
5. Loyalty and Stored-Value Wallet Systems
Closed-loop wallets allow customers to store value that is only redeemable within the enterprise’s own ecosystem. This is a powerful tool for driving repeat business and managing high-volume, low-value micro-transactions.
- Brand Ecosystems: Encourages users to keep their capital within the company’s network of products and services.
- Prepaid Growth: Provides the enterprise with upfront liquidity while offering customers discounts or exclusive rewards.
Selecting the appropriate wallet type ensures that the technical infrastructure aligns with the broader business strategy. This alignment allows for a scalable financial product that meets both user expectations and regulatory requirements.
Key Features of an Enterprise Wallet Platform
A high-performance wallet platform must balance sophisticated financial controls with a frictionless user experience. These core features provide the transparency and agility necessary to manage digital asset custody across a global organization.
1. Multi-Wallet Account Management
Modern systems allow a single entity to maintain numerous sub-wallets for distinct operational purposes. This structure enables precise budgeting and departmental fund allocation without creating separate bank accounts.
- Granular Partitioning: Users can segregate funds into specific buckets like payroll, marketing, or research.
- Hierarchical Oversight: Administrators maintain a bird’s-eye view of all sub-wallets from a central parent account.
2. Real-Time Transaction Ledger
The ledger provides an instantaneous and immutable record of every movement within the system. This ensures that the enterprise always has an accurate picture of its current liabilities and assets.
- Instant Reconciliation: Balances update the moment a transaction is initiated to prevent overdrawing.
- Double-Entry Standards: Every entry follows strict accounting principles to ensure the system is always in balance.
3. Internal Transfers and Wallet-to-Wallet Payments
Moving value between users on the same platform should be instantaneous and cost-free. This capability eliminates the delays and fees typically associated with third-party payment processors.
- Off-Chain Settlement: Transfers occur on the internal database rather than a public blockchain or bank network.
- Seamless Payouts: Businesses can distribute rewards or salaries to thousands of users with a single API call.
4. External Payment Rail Connectivity
To be useful, a wallet must interact with the broader financial world for deposits and withdrawals. Bridging internal ledgers with external networks is critical for maintaining liquidity.
- Fiat On-Ramps: Integration with ACH, Swift, or SEPA allows users to fund their wallets with traditional currency.
- Crypto Gateways: Direct connections to digital asset networks facilitate the movement of stablecoins and other tokens.
5. Smart Transaction Rules and Limits
Enterprises require automated safeguards to prevent fraud and accidental overspending. These rules act as a programmable layer of defense that monitors every transaction in real time.
- Custom Velocity Limits: Platforms can restrict the number or value of transfers within a specific timeframe.
- Whitelist Management: Administrators can limit outgoing payments to pre-approved addresses or verified vendor accounts.
6. Treasury and Liquidity Controls
Managing the “float” and ensuring enough capital is available for withdrawals is a primary treasury function. These tools allow finance teams to optimize their cash positions and earn yield on idle assets.
- Automated Rebalancing: Systems can move funds between hot and cold storage based on predicted demand.
- Liquidity Alerts: Notifications trigger when account balances fall below a specified threshold to prevent service interruptions.
7. Admin Controls and Operational Dashboards
A centralized command center allows non-technical staff to manage the platform’s daily operations. This interface should provide clear visualizations of system health and financial performance.
- Role-Based Access: Different permission levels ensure that only authorized staff can perform sensitive actions.
- System Health Monitoring: Dashboards track API uptime, transaction success rates, and potential security threats.
8. Audit Logs and Financial Reporting
Compliance demands a transparent trail of every action taken by both users and administrators. Detailed logging ensures that the enterprise can survive rigorous external audits and regulatory reviews.
- Immutable Logs: Every change to a wallet’s status or permissions is recorded and cannot be altered.
- Exportable Reports: Finance teams can generate CSV or PDF summaries for tax filings and internal board reviews.
These features collectively transform a simple digital container into a powerful financial engine. By choosing a platform that prioritizes these capabilities, an enterprise can significantly reduce its operational overhead while increasing its market agility.
Compliance Requirements for Enterprise Wallet Platforms
Regulatory alignment is the primary differentiator between an experimental project and a scalable financial service.
For any organization undertaking digital asset custody, navigating the 2026 landscape requires a proactive approach to evolving global standards.
1. KYC and Customer Identity Verification
Identity verification serves as the first line of defense against financial crime. Enterprises must implement automated, multi-tiered “Know Your Customer” workflows that adapt to the user’s risk profile and transaction volume.
- Biometric Authentication: Utilizing liveness detection and facial recognition to match users against government-issued identification.
- Watchlist Screening: Running continuous checks against global sanctions lists, PEP (Politically Exposed Persons) databases, and adverse media.
2. AML Transaction Monitoring and Risk Controls
Anti-Money Laundering (AML) protocols require sophisticated systems to detect and report suspicious behavioral patterns. Organizations must maintain a “risk-based approach” that monitors both the source and the destination of all funds.
- Velocity and Threshold Alerts: Automatically flagging transfers that deviate from a user’s typical spending behavior or historical patterns.
- Travel Rule Compliance: Ensuring that originator and beneficiary information is securely transmitted for cross-border digital asset transfers, as mandated by FATF.
3. Custody and Safeguarding Requirements
Safeguarding ensures that customer assets remain protected and separate from the enterprise’s operational capital. Regulatory bodies increasingly mandate a “one-to-one” reserve ratio to prevent the commingling of funds.
- Asset Segregation: Maintaining distinct on-chain and off-chain environments to ensure user assets are never used for corporate liabilities.
- Insolvency Protection: Structuring custody agreements so that assets are held in a remote bankruptcy vehicle, protecting users in the event of corporate failure.
4. PCI DSS Requirements for Payment Data
If an enterprise wallet interacts with traditional credit or debit cards, it must adhere to the latest PCI DSS 4.0 standards. This framework focuses on the continuous protection of sensitive authentication data.
- Network Segmentation: Isolating the cardholder data environment (CDE) from the rest of the enterprise network to minimize security scope.
- MFA Everywhere: Implementing mandatory multi-factor authentication for all administrative and user-level access to the payment environment.
5. Regional Regulatory Frameworks Enterprises Must Follow
The regulatory environment is highly fragmented, requiring a localized strategy for every market an enterprise enters. Understanding these frameworks is essential for maintaining “passporting” rights and legal standing.
- European Union (MiCA): The Markets in Crypto-Assets regulation provides a unified rulebook for digital asset service providers across all EU member states.
- Singapore (Payment Services Act): A robust licensing regime governed by the MAS that focuses heavily on interoperability and consumer protection.
6. Auditability and Financial Recordkeeping
Maintaining an immutable audit trail is no longer optional for highly regulated industries. Enterprises must be able to produce detailed historical reports for regulators at a moment’s notice.
- Immutable Logging: Ensuring that all ledger changes, administrative actions, and permission updates are cryptographically signed and stored.
- Independent Quarterly Audits: Engaging third-party firms to verify that actual asset holdings match the liabilities recorded on the internal ledger.
Operating within these guardrails transforms regulatory pressure into a competitive advantage. A compliant infrastructure builds the necessary trust for institutional partners and high-value customers to engage with the platform.
Security Architecture for Enterprise Wallet Platforms
A resilient security posture is the only way to maintain trust and protect the high-value assets within an organization.
Implementing a multi-layered defense ensures that digital asset custody remains secure against both sophisticated external attacks and internal vulnerabilities.
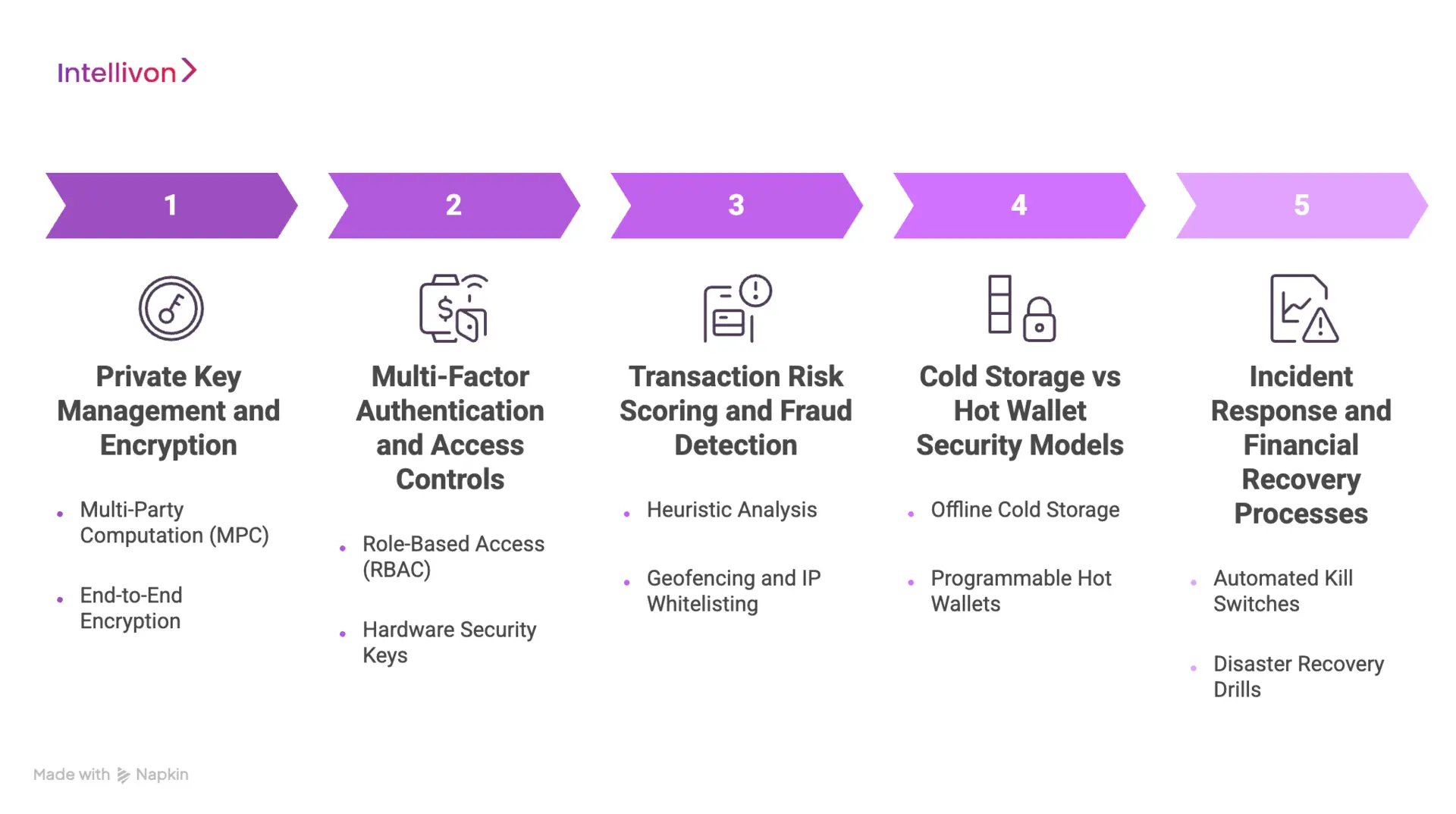
1. Private Key Management and Encryption
Private keys are the ultimate credentials that authorize the movement of every digital asset. Protecting these keys requires an environment where no single individual or system can access the full cryptographic secret.
- Multi-Party Computation (MPC): This technique splits a private key into multiple shards distributed across isolated servers.
- End-to-End Encryption: All sensitive data is encrypted at rest and in transit using industry-standard AES-256 protocols.
2. Multi-Factor Authentication and Access Controls
Strong identity management prevents unauthorized users from gaining entry to the wallet infrastructure. Organizations must move beyond simple passwords to hardware-based security tokens and biometric verification.
- Role-Based Access (RBAC): Permissions are strictly limited to the specific functions required for an employee’s job.
- Hardware Security Keys: Requiring physical FIDO2 tokens for all administrative actions eliminates the risk of remote phishing.
3. Transaction Risk Scoring and Fraud Detection
Every transaction must undergo a real-time risk assessment before it is committed to the ledger. This automated layer identifies anomalies that suggest fraudulent activity or a compromised account.
- Heuristic Analysis: The system compares new transactions against historical user behavior to spot outliers.
- Geofencing and IP Whitelisting: Payments can be restricted to known secure locations or specific corporate network ranges.
4. Cold Storage vs Hot Wallet Security Models
Balancing liquidity with security requires a tiered approach to how assets are stored. While “hot” wallets handle immediate transactions, the majority of funds should remain in offline environments.
- Offline Cold Storage: Assets not needed for daily liquidity are kept in air-gapped hardware that is never connected to the internet.
- Programmable Hot Wallets: Small amounts of capital are kept online but are governed by strict daily withdrawal limits.
5. Incident Response and Financial Recovery Processes
No security model is perfect, making a robust recovery plan essential for operational continuity. Enterprises must have pre-defined protocols to freeze assets and restore services during a security event.
- Automated Kill Switches: Administrators can instantly pause all outgoing transfers if the system detects a breach.
- Disaster Recovery Drills: Regular simulations ensure that the technical team can restore the ledger from backups without data loss.
A proactive security architecture provides the stability required for long-term growth. When security is baked into the core design, it becomes a silent enabler of every financial transaction.
Integration Layer: Connecting Wallets to the Financial Ecosystem
A standalone wallet provides limited value without deep connectivity to the broader economic landscape.
The integration layer serves as the bridge that allows digital asset custody systems to interact with legacy banking and modern decentralized networks.
1. Banking Infrastructure and Settlement Accounts
To facilitate fiat movements, the wallet platform must interface directly with core banking systems. These connections allow for automated clearing and real-world settlement of internal ledger balances.
- Virtual IBANs: Providing users with unique bank identifiers simplifies the process of receiving external wire transfers.
- Direct Clearing Access: Deep integrations with ACH or SEPA networks enable faster fund availability for the enterprise.
2. Payment Processors and Card Networks
Connecting to global card schemes allows users to spend their wallet balances at millions of merchant locations. This integration is essential for creating a versatile financial product that functions in the physical world.
- Card Issuing APIs: Enterprises can instantly provision virtual or physical debit cards linked to specific wallet sub-accounts.
- Merchant Acquiring: Integrating with processors ensures that the platform can accept credit card deposits with minimal friction.
3. Stablecoin and Blockchain Integrations
Modern wallets must support the programmable nature of digital assets to remain competitive in a global market. These bridges allow for 24/7 settlement without the delays inherent in traditional banking hours.
- On-Chain Settlement: Direct node connectivity enables the transfer of value across Ethereum, Polygon, or other major networks.
- Smart Contract Interaction: Automated escrow and conditional payments can be executed based on real-time data triggers.
4. KYC and Compliance Data Providers
Maintaining a secure ecosystem requires real-time data feeds from specialized identity and risk vendors. These integrations automate the “gatekeeping” process to ensure only verified participants can transact.
- Identity Orchestration: Connecting to global databases allows for instant verification of government IDs and biometric data.
- Transaction Monitoring: Real-time feeds from chain analysis tools help identify and block high-risk or illicit fund movements.
5. Treasury and Liquidity Management Systems
For an enterprise, managing the “float” across multiple currencies and jurisdictions is a complex operational task. Integration with treasury tools ensures that capital is always deployed efficiently to maximize yield.
- Liquidity Aggregation: Systems can automatically pull liquidity from multiple exchanges to ensure competitive conversion rates.
- Automated Rebalancing: Treasury triggers can move funds between operational accounts and long-term storage based on demand.
This connectivity transforms a private ledger into a globally accessible financial hub. When the integration layer is robust, the enterprise can move value across any network with the same level of ease and security.
How We Develop Enterprise Wallet Platforms Step-By-Step
Building a resilient financial product requires a shift from rapid prototyping to high-assurance engineering. At Intellivon, our development methodology for digital asset custody and wallet systems prioritizes security, scalability, and regulatory alignment at every phase of the lifecycle.
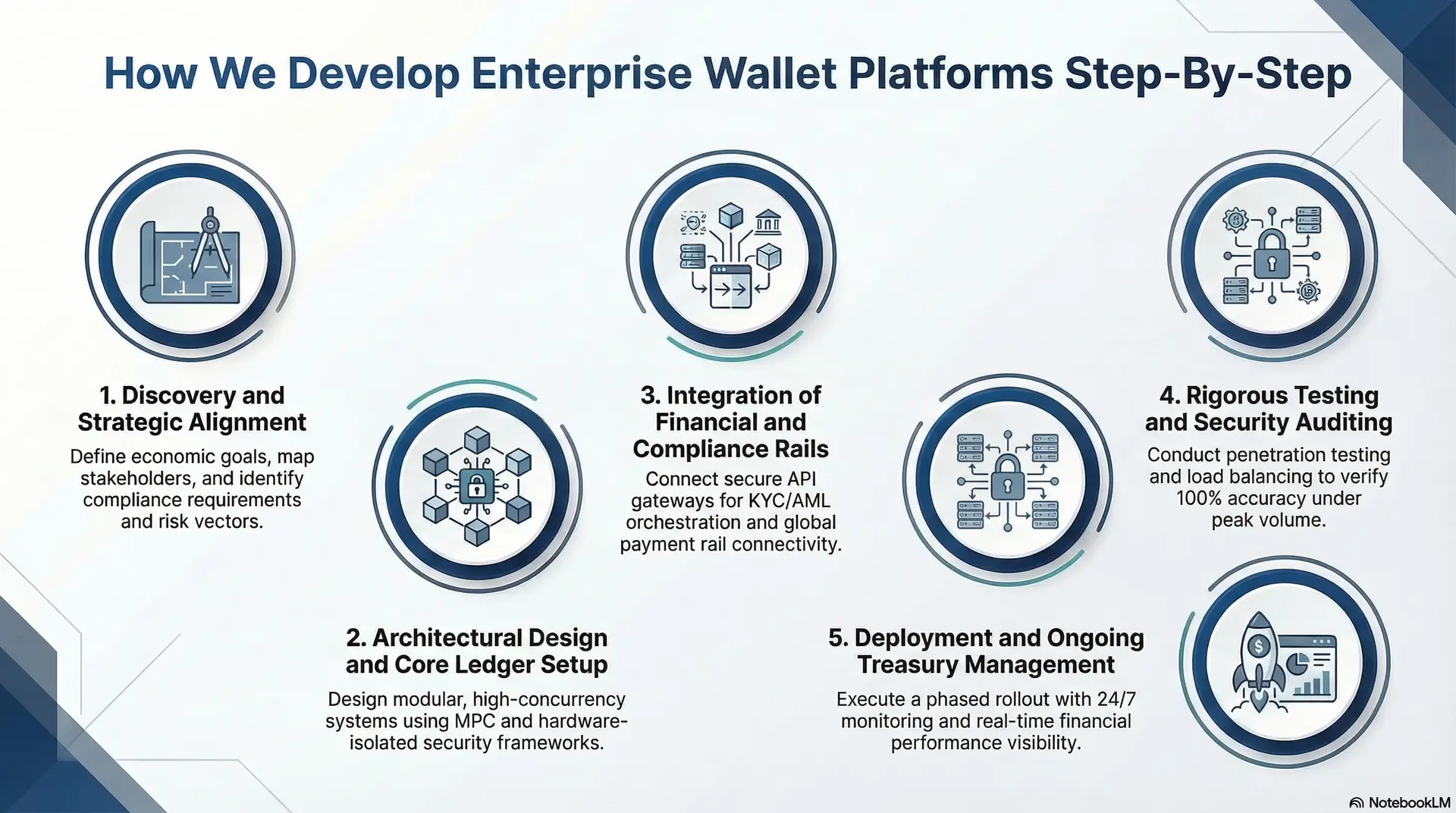
1. Discovery and Strategic Alignment
Every engagement begins by defining the specific economic goals and compliance requirements of the enterprise. We identify the necessary payment rails and jurisdiction-specific regulations that will govern the platform’s architecture.
- Stakeholder Mapping: We align technical requirements with the strategic needs of treasury, legal, and product teams.
- Risk Assessment: Identifying potential fraud vectors and liquidity bottlenecks before a single line of code is written.
2. Architectural Design and Core Ledger Setup
We design a modular system that separates the user-facing application from the sensitive transaction engine. This ensures that the core ledger remains immutable and protected from external vulnerabilities.
- High-Concurrency Engineering: Building the infrastructure to handle thousands of simultaneous balance updates without latency.
- Security-First Modeling: Implementing digital asset custody frameworks that utilize MPC and hardware-isolated environments.
3. Integration of Financial and Compliance Rails
The platform is then connected to the broader financial ecosystem through secure API gateways. This phase focuses on creating seamless bridges between internal accounts and external banking or blockchain networks.
- KYC/AML Orchestration: Automating identity verification and transaction monitoring to ensure continuous compliance.
- Payment Rail Connectivity: Linking the wallet to ACH, SWIFT, and stablecoin networks for global value movement.
4. Rigorous Testing and Security Auditing
Before deployment, the platform undergoes extensive stress testing and third-party security reviews. We simulate high-load scenarios and potential attack vectors to verify the system’s resilience.
- Penetration Testing: Specialized teams attempt to breach the infrastructure to identify and patch vulnerabilities.
- Load Balancing: Verifying that the ledger maintains 100% accuracy during peak transaction volumes.
5. Deployment and Ongoing Treasury Management
Once the platform is live, we focus on optimizing liquidity flows and ensuring operational stability. Our dashboards provide real-time visibility into system health and financial performance for the enterprise team.
- Gradual Rollout: Implementing a phased release to monitor user behavior and system performance in a live environment.
- Continuous Monitoring: 24/7 oversight of API uptime and transaction success rates to prevent service interruptions.
Following a disciplined development path mitigates the inherent risks of launching a financial service. This structured approach ensures that the final product is not just functional, but a foundational asset for the organization’s digital future.
Cost Of Developing An Enterprise Wallet Platform
At Intellivon, enterprise wallet platforms are designed as regulated financial infrastructure, not as payment features layered onto existing systems. The focus stays on building platforms that manage digital balances, transactions, and compliance across regions and financial networks.
However, security controls, transaction integrity, settlement logic, and compliance monitoring are never reduced. As a result, enterprises avoid costly remediation after launch and maintain predictable long-term ROI.
Estimated Phase-Wise Cost Breakdown
| Phase | Description | Estimated Cost Range (USD) |
| Discovery & Regulatory Alignment | Wallet model definition, jurisdiction mapping, compliance, and payment scope assessment | $8,000 – $15,000 |
| Secure Architecture Design | Ledger design, wallet structure, identity flows, transaction processing logic | $12,000 – $20,000 |
| Governance & Policy Framework | Transaction limits, authorization policies, audit workflows, risk controls | $10,000 – $18,000 |
| Backend & Financial Integrations | Bank APIs, payment rails, compliance providers, treasury integrations | $18,000 – $35,000 |
| Frontend & Role-Based Interfaces | User wallets, admin dashboards, operational monitoring tools | $12,000 – $20,000 |
| Wallet Ledger & Balance Management | Transaction ledger, reconciliation logic, and balance tracking systems | $12,000 – $20,000 |
| Security & Financial Controls | Encryption, fraud monitoring, access control, transaction risk rules | $12,000 – $20,000 |
| Testing & Compliance Validation | Functional testing, financial accuracy testing, and security validation | $8,000 – $14,000 |
| Deployment & Scale Readiness | Cloud infrastructure, monitoring systems, and performance tuning | $10,000 – $16,000 |
Total initial investment: $100,000 – $200,000
Ongoing maintenance and optimization:
Approximately 15–20% of the initial development cost per year.
Hidden Costs Enterprises Should Plan For
- Even well-planned wallet programs face pressure when indirect costs are ignored.
- Integration complexity increases as banks, payment networks, and financial partners expand.
- Compliance overhead grows due to regulatory updates, reporting requirements, and periodic audits.
- Governance requires ongoing policy adjustments, transaction monitoring, and exception management.
- Infrastructure costs increase as transaction volume, analytics workloads, and monitoring systems expand.
- Change management involves onboarding finance, operations, compliance, and support teams.
- Continuous monitoring becomes critical as fraud risks and financial exposure increase.
Best Practices To Avoid Budget Overruns
Based on Intellivon’s experience building enterprise fintech platforms, several practices consistently help organizations control costs.
- Start with a clearly defined wallet model before expanding features or regions.
- Embed governance, auditability, and financial controls directly into the platform architecture.
- Use modular infrastructure so new services can scale without redesign.
- Plan integrations early to avoid expensive retrofitting later.
- Maintain observability across performance, fraud monitoring, and compliance systems.
- Design the platform for regulatory evolution instead of one-time certification.
Organizations planning to build an enterprise wallet platform can work with Intellivon’s fintech experts to define a delivery roadmap aligned with budget constraints, regulatory exposure, and long-term financial infrastructure strategy.
Operational Challenges in Enterprise Wallet Development
Scaling a financial platform introduces complexities that go beyond simple software engineering.
Managing digital asset custody requires navigating a landscape of high-concurrency data, volatile liquidity, and shifting global regulations.
1. Maintaining Ledger Consistency at Scale
As transaction volumes grow, ensuring that every debit perfectly matches a credit across distributed databases becomes increasingly difficult. Any latency in ledger updates can lead to overspending or inaccurate balance reporting for the user.
How We Solve It: We utilize a high-performance, double-entry accounting engine built on event-sourcing principles. This architecture ensures that every state change is recorded as an immutable event, providing a perfect audit trail and sub-millisecond consistency.
2. Managing Multi-Currency Liquidity
Enterprises operating globally must maintain sufficient reserves across various fiat and digital currencies to facilitate instant withdrawals. Fluctuating exchange rates and fragmented banking rails can trap capital in the wrong jurisdictions, leading to service delays.
How We Solve It: Our platform integrates automated treasury rebalancing tools that monitor liquidity levels in real time. We connect with multiple liquidity providers to ensure competitive FX rates and use predictive analytics to move funds before a shortfall occurs.
3. Preventing Fraud and Unauthorized Transfers
Sophisticated bad actors constantly look for vulnerabilities in the transaction authorization layer. Without robust defenses, a single compromised credential could lead to significant financial loss and a total breakdown of user trust.
How We Solve It: We implement a “Zero Trust” security model that requires multi-party computation (MPC) for all high-value movements. Every transaction is subjected to a real-time risk scoring engine that flags anomalies based on biometrics, geolocation, and historical spending patterns.
4. Handling Regulatory Complexity Across Regions
A wallet that is compliant in one country may violate financial laws in another, especially regarding digital asset custody and stablecoins. Manually tracking these changes across dozens of markets is prone to error and incredibly resource-intensive.
How We Solve It: We treat “Compliance-as-Code” by embedding regional regulatory rules directly into our API layer. Our system automatically adjusts KYC requirements and transaction limits based on the user’s verified residency and the specific legal framework of their region.
5. Ensuring Real-Time System Availability
Financial services are expected to be available 24/7, as any downtime results in lost revenue and damaged reputation. Maintaining this level of uptime during system upgrades or high-traffic events requires a highly resilient infrastructure.
How We Solve It: We deploy our wallet platforms using a geo-distributed, multi-cloud architecture that eliminates single points of failure. This allows for “hot” updates where we can deploy new features or security patches without ever taking the ledger offline.
Addressing these challenges early in the development process prevents costly pivots later. A platform designed to handle these operational hurdles is one that can truly support enterprise-grade expansion.
Conclusion
Adopting an enterprise wallet infrastructure is a strategic move toward financial sovereignty. This shift allows organizations to internalize value exchange, reduce dependency on legacy processors, and unlock innovative revenue streams through embedded finance.
By prioritizing digital asset custody and a robust security architecture, businesses can scale their operations globally with absolute confidence. Owning your financial stack ensures long-term agility and positions your enterprise as a leader in the digital economy.
Build an Enterprise Wallet Platform With Intellivon
At Intellivon, enterprise wallet platforms are engineered as regulated financial infrastructure, not as simple payment wallets layered onto existing systems. Each platform is designed to manage digital balances, transaction flows, and financial governance across complex enterprise environments.
Every solution is built for regulated fintech ecosystems. Wallet platforms remain reliable under high transaction volume, integrate with banking and payment networks, and maintain financial accuracy through governed ledger systems and compliance-ready infrastructure.
Why Partner With Intellivon?
- Governance-First Wallet Architecture: Wallet systems are designed with embedded policy controls, approval workflows, and role-based access governance.
- Enterprise-Grade Ledger Infrastructure: Our platforms include double-entry ledger systems, real-time balance management, and reconciliation logic.
- Secure Transaction and Risk Controls: Security layers include encryption, access enforcement, fraud monitoring, and configurable transaction limits.
- Provider-Agnostic Financial Integrations: Wallet platforms integrate with banks, payment processors, compliance providers, and treasury systems.
- Compliance-Ready Wallet Systems: KYC, AML monitoring, audit logs, and reporting systems are embedded directly into the platform.
- Scalable Infrastructure for Enterprise Growth: Architecture is designed to support expanding transaction volume, multi-currency operations, and new financial integrations without compromising performance, security, or governance.
If your organization is exploring enterprise wallet development, Intellivon can help design and deploy a secure, compliant, and scalable wallet platform built for long-term financial control and operational resilience.
FAQs
Q1. How do you develop an e-wallet?
A1. Developing an e-wallet starts with defining the wallet model and supported payment methods. Next, engineers design the platform architecture, including a transaction ledger, user identity management, and payment integrations. Security and compliance features such as KYC, AML monitoring, and encryption must also be included. After development, the platform goes through testing and regulatory validation before deployment.
Q2. How much does it cost to develop a crypto wallet?
A2. Developing a crypto wallet usually costs between $80,000 and $200,000 for an enterprise-grade platform. In addition, ongoing maintenance and security updates typically cost 15–20% of the initial build annually.
Q3. How do e-wallets make money?
A4. E-wallet platforms generate revenue through several monetization models. The most common source is transaction fees from payments and transfers. Many platforms also earn interchange revenue when users pay with linked cards. In addition, some wallets offer financial services such as lending, subscriptions, or premium features that create additional revenue streams.
Q5. What are the negative effects of e-wallets?
A5. E-wallet platforms can introduce risks if governance and security controls are weak. Fraud, unauthorized access, and account takeovers are common threats in poorly protected systems. In addition, high dependence on digital payments can increase exposure to system outages or cyberattacks. Therefore, strong security architecture and compliance monitoring are essential for safe wallet operations.






