Key Takeaways
-
Rule-based fraud systems fail against AI-driven attacks because static logic cannot adapt to synthetic identities, deepfakes, and real-time payment rails where losses are irreversible.
-
AI detects fraud through layered signals, including transaction velocity, device fingerprinting, geolocation mismatches, and graph relationships that map entire fraud ring networks.
-
Gradient boosting, graph neural networks, sequence models, and unsupervised anomaly detection each serve distinct fraud types.
-
Build costs range from $10,000 for a basic MVP to $80,000 and above for an enterprise-grade system with sub-200ms decisioning.
-
How Intellivon builds AI-driven fraud detection systems that your payment platform fully owns, with compliance-ready architecture built in from day one.
Payment infrastructure in banks is faster than ever. The reality right now functions on the fact that payment settlement windows have collapsed, transaction volumes have scaled beyond what any manual process can touch, and the attack surface has expanded in step with every new rail added to the ecosystem.
The detection systems built for old systems were designed around a different assumption, which is to catch fraudulent activity after the damage is done. However, this assumption does not favor fintech enterprises that are trying to get ahead of the curve. The gap between how fraud operates today and how most detection stacks were built is where losses accumulate.
What the payment enterprises pulling ahead understand is that fraud detection is now a core product decision, one that shapes conversion, customer trust, regulatory standing, and operational cost simultaneously.
Building an AI-powered fraud detection system that performs across all four dimensions requires deliberate architecture choices and expertise. At Intellivon, we have built AI-driven fraud detection systems for payment enterprises that need to operate at that standard. This guide covers exactly how we approach building from the ground up.
Why Are Payment Fraud Systems Failing in 2026?
Modern fraud operates at machine speed, rendering traditional rule-based defenses completely ineffective against AI-driven tactics. Decision makers must pivot from reactive monitoring to real-time, identity-led prevention to protect their capital and reputation.
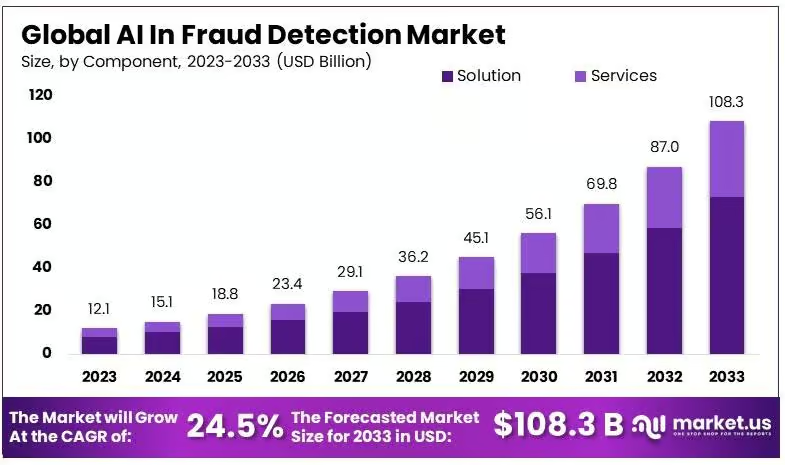
AI-driven fraud detection tools are gaining rapid traction as cyber threats grow alongside digital transaction volumes. As a result, enterprise adoption continues to rise, with the market expected to see strong expansion through 2033.
1. Legacy Systems Cannot Stop AI Attacks
Static rules fail because fraudsters now use deepfakes and synthetic identities to mimic genuine user behavior perfectly.
These automated attacks bypass traditional filters, requiring adaptive systems that learn and respond to new threats instantly.
2. Instant Payments Require Instant Defense
Real-time settlement leaves no room for manual review or post-transaction recovery efforts. Therefore, your platform must verify the legitimacy of every participant and transaction within milliseconds to prevent irreversible financial loss.
- Machine-Speed Fraud: Attackers use generative AI to scale phishing and impersonation efforts across multiple channels.
- Verification Gaps: Many enterprises fail to continuously validate bank details, leading to successful vendor impersonation scams.
- Vanishing Recovery: The shift toward instant payment rails means that undetected fraud results in immediate, permanent capital flight.
- Adaptive Intelligence: Modern security requires neural networks that update their threat models without waiting for human intervention.
Investment in sophisticated prevention is no longer optional for those building competitive financial platforms. By prioritizing sub-second identity proofing and behavioral analytics, you transform security from a cost center into a core business advantage.
What Fraud Threats Must Your System Handle Today?
Modern payment systems face a new breed of automated threats that traditional security measures simply cannot detect. To protect your investment, you must understand how these sophisticated attacks exploit gaps in speed and identity.
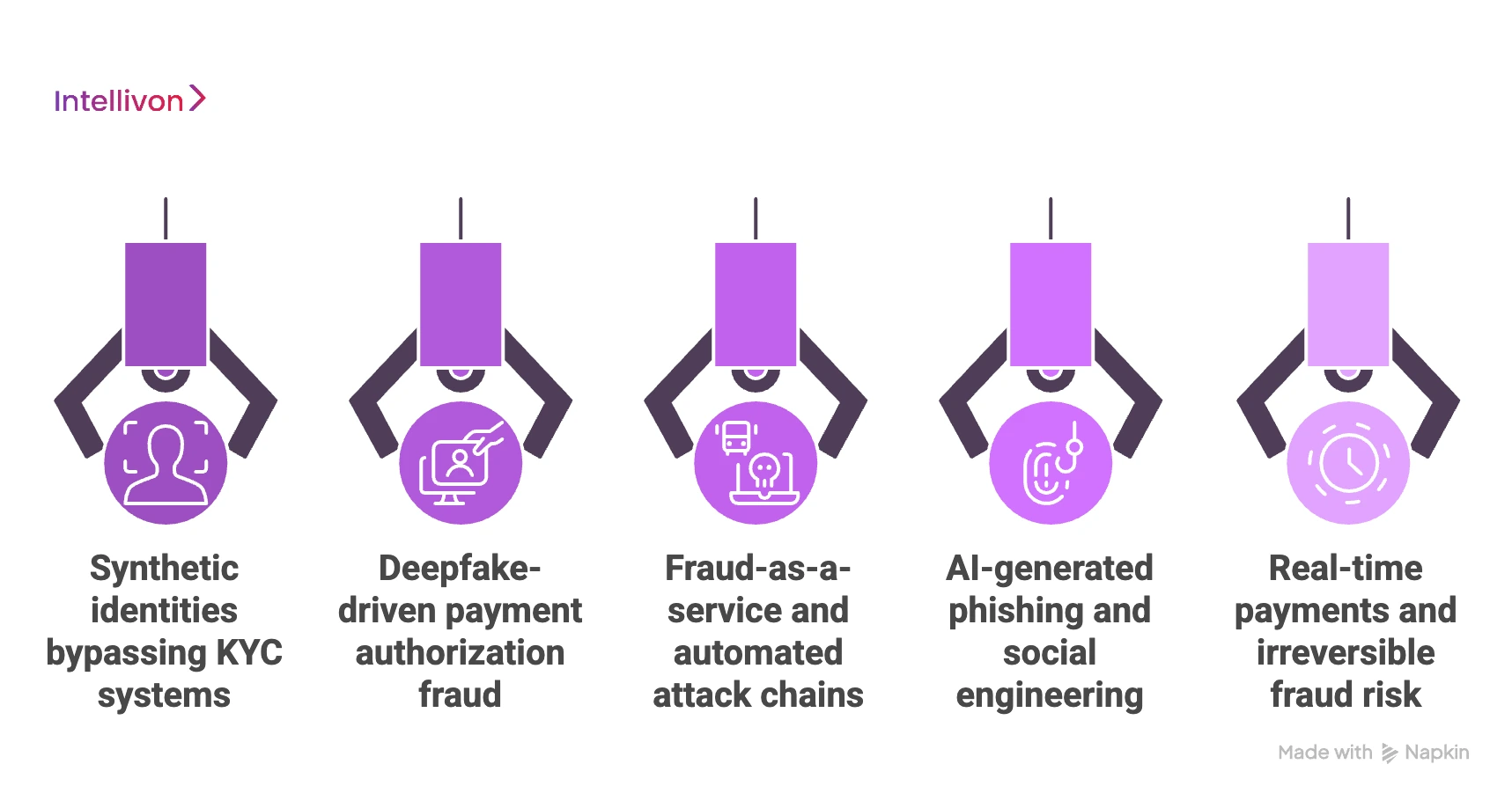
1. Synthetic identities bypassing KYC systems
Fraudsters combine real and fake data to create entirely new digital personas that look like perfect customers. These identities easily pass basic background checks and build credit over time before executing a large-scale theft.
2. Deepfake-driven payment authorization fraud
Advanced AI can now clone voices and faces to bypass video or audio verification during high-value transfers. This allows criminals to impersonate executives or account holders, tricking your staff or automated systems into authorizing fraudulent payments.
3. Fraud-as-a-service and automated attack chains
Cybercriminals now sell ready-to-use attack toolkits, allowing even low-skilled hackers to launch massive, coordinated strikes. These automated chains probe your system for weaknesses 24/7, searching for any small entry point to exploit.
4. AI-generated phishing and social engineering
Generative AI creates highly personalized and grammatically perfect messages that are impossible to distinguish from legitimate corporate emails. These attacks target the human element of your business, manipulating employees into revealing credentials or changing payment details.
5. Real-time payments and irreversible fraud risk
Instant payment rails leave zero time for your team to flag or reverse a suspicious transaction once it starts. In this environment, any detection that happens after the “send” button is clicked is essentially useless for capital recovery.
- Identity Blending: Using a mix of stolen social security numbers and fake names to create “sleeper” accounts.
- Media Manipulation: High-fidelity deepfakes used to trick biometric “liveness” checks during onboarding.
- Speed Vulnerability: The transition to instant settlement means your defense must live at the point of authorization.
- Social Deception: AI tools that research your employees on LinkedIn to craft the perfect, believable scam message.
Building a platform without addressing these specific risks is like building a vault with an open door. Focus your resources on defensive AI that can think as fast as the attackers trying to penetrate your system.
Why Do Rule-Based Fraud Systems Create More Risk?
Legacy systems rely on rigid “if-then” logic that acts as a stationary fence rather than a smart filter. For a growing platform, these static barriers often block legitimate revenue while failing to stop modern, adaptive criminals.
1. Static rules vs dynamic fraud behavior
Traditional rules look for specific, known patterns, but modern fraud constantly changes its shape to avoid detection. When your system is fixed and the enemy is fluid, you are essentially protecting your business with yesterday’s news.
| Feature | Rule-Based Systems | AI-Driven Systems |
| Logic | Fixed “if-then” thresholds | Adaptive pattern recognition |
| Response | Manual updates required | Self-learning in real-time |
| Accuracy | High rates of error | High precision with low noise |
| Speed | Slow to adjust to new threats | Instant detection of anomalies |
2. High false positives and customer drop-offs
Strict rules often flag honest customers as suspicious, forcing them through frustrating verification loops or declining their payments entirely. This friction kills the user experience, driving high-value users straight to your competitors who offer a smoother onboarding process.
3. Delayed detection in real-time payment flows
Rules take time to process and even longer for humans to review once an alert is triggered. In a world of instant transfers, a system that flags fraud five minutes after the money has left the account is a liability.
4. Inability to adapt to concept drift
Market conditions and consumer habits change over time, rendering old rules obsolete and ineffective overnight. Without AI, your team will spend more time manually fixing broken rules than they do growing the actual business or improving the product.
- Friction Points: Unnecessary payment declines represent lost lifetime value and damage your brand’s reputation for reliability.
- Maintenance Burden: Legacy systems require expensive teams of analysts to constantly write, test, and deploy new manual rules.
- The “Grey” Area: Rigid rules only see black and white, failing to interpret the subtle behaviors that signal professional fraud.
- Scalability Limits: As your transaction volume grows, the number of manual reviews becomes an impossible operational bottleneck.
Relying on outdated rules creates a false sense of security that actually invites sophisticated attackers to test your limits. Moving toward an AI-powered adaptive architecture is the only way to ensure your security scales as fast as your ambition.
How Does AI Detect Fraud in Payment Transactions?
AI transforms the uncertainty of transaction monitoring into a transparent, high-speed decision engine. By processing thousands of data points simultaneously, it identifies risks that are invisible to the human eye before the capital ever leaves the account.
1. Real-time transaction scoring using risk signals
Every payment is instantly converted into a multidimensional risk vector that measures variables like location, device health, and historical behavior.
The AI assigns a probability score in milliseconds, allowing the system to approve, flag, or block the transaction without causing a delay for the user.
- Vectorization: Turning complex data into mathematical coordinates for instant comparison.
- Probability Models: Moving from “yes/no” rules to nuanced risk percentages.
- Speed of Thought: Scoring occurs in the blink of an eye to support instant payment rails.
2. Behavioral analysis to detect user anomalies
Instead of looking for specific “bad” actions, AI focuses on what “normal” looks like for each specific user profile.
By establishing a unique baseline for every customer, the system can instantly spot subtle deviations that suggest an account has been compromised.
- Spend Velocity: Detecting an unnatural number of transactions within a short window.
- Environmental Shifts: Identifying logins from unfamiliar devices or unusual geographic locations.
- Biological Patterns: Analyzing how a user interacts with their device, such as typing speed or touch pressure.
3. Pattern recognition across millions of transactions
The intelligence layer of AI allows it to scan the entire ecosystem to find hidden signatures that suggest a coordinated attack.
These models can correlate merchant risks and micro-patterns across millions of data points to stop fraud before it reaches a massive scale.
- Micro-pattern Detection: Spotting tiny, repeated behaviors that indicate a bot or testing phase.
- Cross-Merchant Intelligence: Using data from one attack to protect all other participants in the network.
- Feature Engineering: Automatically identifying which transaction details are the strongest indicators of risk.
4. Graph analysis to uncover fraud networks
Enterprise-grade AI uses graph technology to map the relationships between disparate accounts, IP addresses, and hardware IDs.
This reveals the hidden structures of fraud rings, allowing you to dismantle entire networks rather than just blocking a single transaction.
- Entity Linking: Connecting seemingly unrelated accounts through shared digital footprints.
- Community Detection: Identifying clusters of accounts that act in a suspicious, synchronized manner.
- Ring Fencing: Isolating an entire group of compromised accounts once a single link is proven fraudulent.
5. Anomaly detection for new fraud types
One of the greatest strengths of AI is its ability to flag behavior that doesn’t match any known historical data.
This proactive stance is essential for stopping “zero-day” fraud and new attack strategies that have never been seen by the industry before.
- Unsupervised Learning: Finding outliers in data without needing a previous example of the crime.
- Zero-Day Protection: Shielding your platform from innovative scams the moment they launch.
- Future-Proofing: Reducing the reliance on historical data sets that may be outdated.
6. Continuous learning from confirmed fraud cases
The system operates on a constant feedback loop where every chargeback and flagged transaction acts as a training lesson. This ensures the model is never static, as it re-trains itself to adapt to the most recent tactics used by global criminal organizations.
- Closed-Loop Feedback: Automatically feeding outcome data back into the decision engine.
- Model Evolution: Ensuring the “intelligence” of the platform grows in lockstep with your transaction volume.
- Accuracy Refinement: Reducing future false positives by learning from past mistakes in real-time.
Modern AI understands the intent behind them. By deploying these layers of defense, you ensure your platform remains a trusted environment for legitimate users while becoming an impossible target for criminals.
What Does an AI-Driven Fraud Detection Architecture Look Like?
Building an enterprise-grade AI-driven fraud detection system requires a sophisticated, layered technical stack that processes data at lightning speed. This architecture transforms raw payment signals into actionable intelligence, ensuring every transaction is scrutinized without compromising user experience.
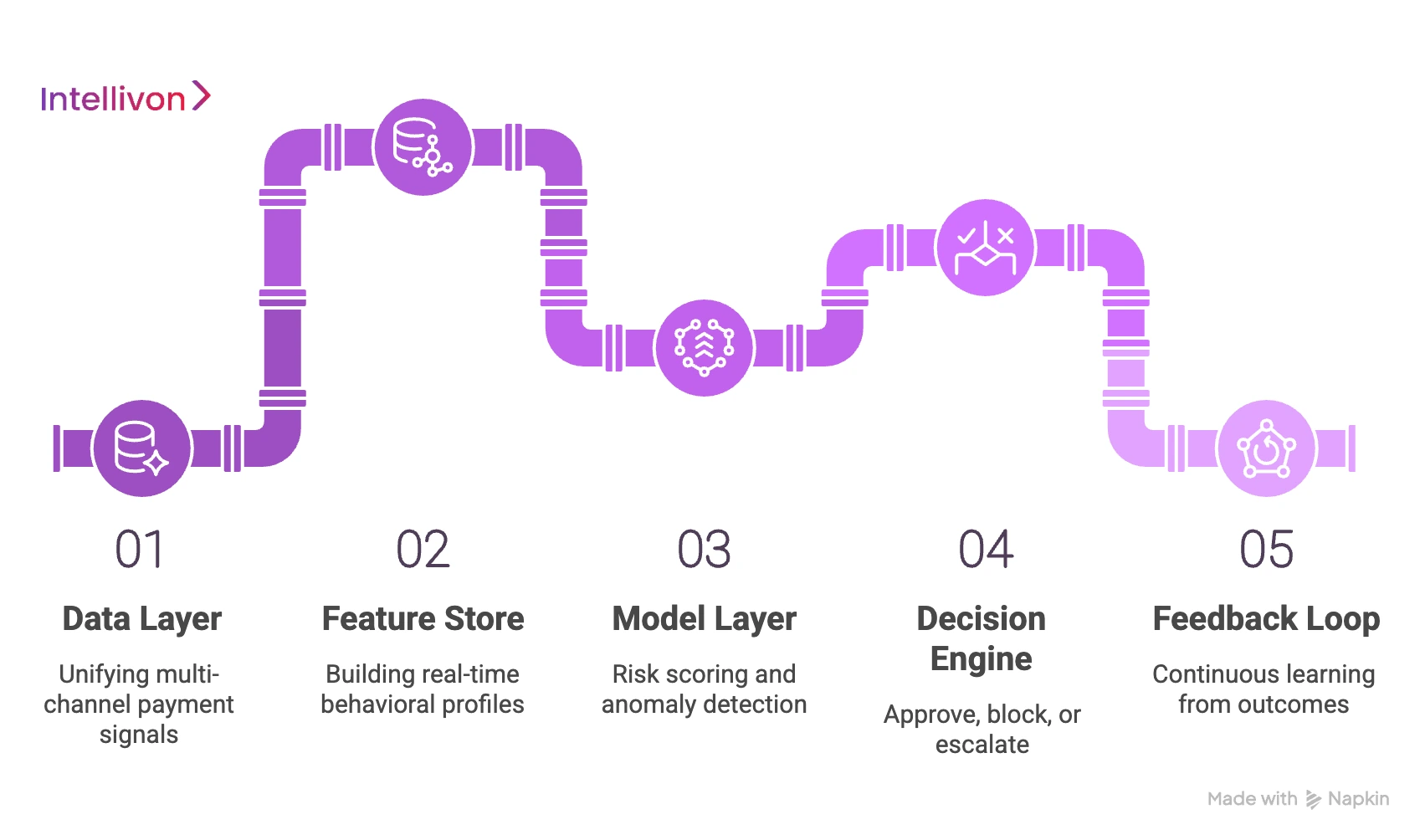
1. Data layer: unifying multi-channel payment signals
The foundation of the system aggregates fragmented data from mobile apps, web portals, and third-party APIs into a single stream.
By unifying device fingerprints, IP metadata, and transaction history, the architecture creates a complete picture of the environment where the payment originates.
- Ingestion Engines: High-throughput pipelines that handle thousands of events per second from diverse sources.
- Normalization: Converting messy, inconsistent data into a structured format for immediate machine analysis.
- Signal Enrichment: Adding external context like geolocation data or known proxy lists to the incoming transaction.
2. Feature store: building real-time behavioral profiles
The feature store is the brain’s memory, calculating and storing “features” like a user’s average spend or most frequent login times. These real-time profiles allow the system to compare the current transaction against years of historical behavior in a matter of milliseconds.
- Streaming Aggregations: Calculating window-based metrics, such as how many transactions occurred in the last hour.
- Low-Latency Retrieval: Ensuring the model can access complex behavioral data without slowing down the checkout process.
- Consistency: Maintaining the same data definitions across both the training phase and the live production environment.
3. Model layer: risk scoring and anomaly detection
In this layer, sophisticated machine learning models analyze the enriched data to identify patterns indicative of fraud. By utilizing ensemble methods, the system cross-references multiple model outputs to ensure the highest possible accuracy for every risk score.
- Ensemble Modeling: Combining different algorithms to catch both known fraud patterns and brand-new anomalies.
- Risk Vectoring: Mapping the transaction into a mathematical space to see how far it drifts from “normal” behavior.
- Explainable AI: Providing internal teams with clear reasons why a specific transaction was flagged or blocked.
4. Decision engine: approve, block, or escalate
The decision engine applies business logic to the model’s score to determine the final outcome of the transaction. It acts as the ultimate gatekeeper, deciding whether to authorize the payment, block it entirely, or trigger a secondary verification step like biometrics.
- Dynamic Thresholds: Adjusting the strictness of the system based on current threat levels or specific merchant profiles.
- Orchestration: Seamlessly routing the user to Multi-Factor Authentication (MFA) only when the risk score justifies the friction.
- Actionable Outcomes: Executing pre-defined protocols like freezing an account or alerting a dedicated security team.
5. Feedback loop: continuous learning from outcomes
The system’s intelligence is maintained through a closed-loop process where actual fraud results are fed back into the models. By learning from every chargeback or confirmed legitimate transaction, the architecture constantly refines its accuracy to stay ahead of evolving threats.
- Labeling: Tagging transactions as “fraud” or “safe” based on real-world outcomes and manual reviews.
- Automated Retraining: Updating model weights regularly to account for new attack vectors or shifting consumer habits.
- Performance Monitoring: Tracking the “drift” of the model to ensure it remains effective as the payment landscape changes.
Investing in a robust architecture ensures your platform can scale without becoming a target for professional fraud syndicates. A well-integrated stack builds the trust necessary for high-volume enterprise growth.
What Data Signals Actually Improve Fraud Detection Accuracy?
Precision in fraud detection depends entirely on the quality of the data signals fed into your AI engine.
Moving beyond simple credit scores, elite platforms ingest multi-dimensional layers of context to differentiate between a high-spending loyalist and a professional thief.
1. Transaction velocity and behavioral baselines
Velocity tracking measures how often a user initiates transactions within a specific timeframe compared to their historical average. Sudden spikes in activity or “card testing” behavior, which is small, rapid purchases used to verify stolen data, trigger immediate alerts before significant capital is drained.
- Volume Anomalies: Identifying a 500% increase in purchase frequency that deviates from established monthly patterns.
- Bursty Behavior: Detecting rapid-fire micro-transactions typically used by botnets to validate account access.
- Temporal Consistency: Recognizing when a user who typically shops at noon suddenly attempts a high-value transfer at 3:00 AM.
2. Device fingerprinting and session anomalies
Every device has a unique digital signature comprised of its OS version, battery level, installed fonts, and hardware specs. By analyzing these signals, the system can detect “man-in-the-middle” attacks or recognize when a single device is trying to access hundreds of different accounts.
- Hardware DNA: Creating a persistent ID that tracks a device even if the user clears their cookies or uses a VPN.
- Session Hijacking: Spotting subtle changes in browser attributes that suggest an active session has been stolen by a third party.
- Emulation Detection: Identifying mobile devices that are actually virtual machines running automated fraud scripts.
3. Geolocation mismatch and IP intelligence
The system cross-references the user’s declared location with their IP address and GPS data to identify impossible travel scenarios.
If a transaction originates from a high-risk data center IP rather than a residential ISP, the risk score is automatically adjusted to reflect the potential for proxy-based masking.
- Impossible Travel: Flagging a login from London just twenty minutes after a successful purchase in New York.
- Proxy Piercing: Using advanced network analysis to see past VPNs and reveal the true origin of a transaction.
- IP Reputation: Checking the history of an IP address to see if it has been associated with previous cyberattacks or bot activity.
4. Merchant risk scoring and transaction context
Not all merchants carry the same risk profile, and AI factors in the reputation of the receiving party to assess the danger level.
By understanding the typical transaction size and category for a specific merchant, the system can flag outliers that suggest a payment is being laundered or sent to a fraudulent storefront.
- Category Analysis: Increasing scrutiny for transactions involving high-risk assets like crypto, gift cards, or luxury electronics.
- Merchant Longevity: Assigning higher trust to established entities versus newly created or unverified payment links.
- Mismatched Context: Questioning a $5,000 office equipment purchase made by a user who traditionally only spends on personal groceries.
5. Graph relationships across users and devices
Graph signals are the most potent tools for uncovering organized fraud rings by mapping the hidden links between seemingly unrelated accounts.
If ten different accounts share the same physical address or have logged in from the same device ID, the system identifies them as a single coordinated entity.
- Link Analysis: Visualizing the “degree of separation” between a new user and a previously blacklisted fraudster.
- Shared Attributes: Identifying clusters of accounts that use the same phone number or recovery email across different platforms.
- Network Contagion: Automatically flags all associated accounts the moment a single node in the network is confirmed as fraudulent.
Harnessing these signals allows your platform to move from “guessing” to “knowing” the intent behind every click. When you layer behavioral DNA with network intelligence, you create a system that is virtually impossible for a human criminal to mimic.
Which AI Models Work Best for Payment Fraud Detection?
Selecting the right mathematical engine is critical for balancing the speed of transactions with the accuracy of your security.
Most modern platforms use a combination of these specific architectures to cover different types of criminal behavior.
1. Gradient boosting for real-time scoring
Gradient Boosting Machines (GBMs) are the industry standard for processing structured transaction data at high speeds. These models are exceptionally good at handling tabular data, like transaction amounts and timestamps, to provide a definitive risk score in a fraction of a second.
- XGBoost and LightGBM: These specific algorithms are favored for their ability to process millions of rows of data with minimal computing power.
- High Interpretability: They allow your team to see exactly which factors, such as a sudden location change, contributed most to a high risk score.
- Efficiency: They excel at finding non-linear relationships in data that simple rules would completely miss.
2. Graph neural networks for fraud rings
Graph Neural Networks (GNNs) are designed to analyze the relationships between different data points, making them perfect for spotting organized crime. By looking at how accounts, devices, and addresses are linked, these models can identify an entire fraud ring even if each individual transaction looks “normal.”
- Relationship Mapping: GNNs treat data as a web of connections rather than isolated events.
- Collective Intelligence: The model learns from the behavior of a user’s “neighbors” in the network to predict if that user is likely to be a fraudster.
- Ring Detection: They are the most effective tool for stopping coordinated “bust-out” fraud where multiple accounts are drained at once.
3. Sequence models for behavioral fraud patterns
Sequence models, like Recurrent Neural Networks (RNNs), are built to understand the “story” behind a series of actions over time. They analyze the entire journey a user took to get there, which helps in spotting account takeovers or bot-driven activity.
- Temporal Patterns: Tracking the specific order of events, such as a password change followed immediately by a high-value transfer.
- User DNA: Building a unique “signature” of how a person navigates your app, from typing rhythm to scroll speed.
- Bot Detection: Identifying the mechanical, repetitive sequences that signal a machine is controlling the account rather than a human.
4. Unsupervised models for unknown fraud types
Unsupervised learning models are unique because they simply find things that are “weird.” These are essential for detecting “zero-day” attacks, new fraud strategies that haven’t been documented or seen before by your team.
- Clustering: Grouping normal transactions together and isolating outliers that don’t fit any known pattern.
- Zero-Day Defense: Providing a safety net against creative new scams that bypass your trained models.
- Noise Reduction: Helping analysts focus on the most unusual cases rather than sifting through thousands of standard alerts.
5. Hybrid models for layered fraud detection
A hybrid approach combines the strengths of multiple models into a single “ensemble” system to provide the most comprehensive protection possible. By running different algorithms in parallel, your platform can catch everything from simple card testing to complex, multi-year money laundering schemes.
- Consensus Scoring: Requiring multiple models to “agree” before a high-value transaction is blocked, which reduces false positives.
- Specialized Layers: Using one model for identity verification and another for transaction logic to ensure every angle is covered.
- Adaptive Switching: Automatically prioritizing different models based on the current threat level or the type of payment rail being used.
The most successful platforms deploy a layered defense where different models work in harmony to protect every stage of the customer journey.
Solving the False Positive Problem in Fraud-Detection Systems
High false-positive rates are the “silent killers” of digital platforms, turning away legitimate customers and destroying your marketing ROI. For a founder, the goal is to find the perfect balance where security is invisible to the honest user but an impenetrable wall for the criminal.
1. Why false positives destroy payment conversion
Every time your system incorrectly flags a valid transaction, you lose customer trust and future lifetime value. A “transaction declined” message is often the last thing a user sees before they switch to a competitor who offers a more seamless experience.
- Customer Churn: Users rarely return to a platform that makes them feel like a criminal through unnecessary blocks.
- Wasted Acquisition: You spend significant capital to acquire a lead, only to have a rigid security filter reject their money at the finish line.
- Brand Reputation: Word spreads quickly if your payment gateway is perceived as “unreliable” or “too difficult” to use.
2. Dynamic risk scoring vs static thresholds
Static thresholds are binary “yes/no” switches that fail to account for the nuance of human behavior, leading to massive error rates.
Dynamic scoring, however, uses AI to adjust its sensitivity based on real-time context, allowing for “grey” areas where a user can be verified rather than just blocked.
- Contextual Sensitivity: Lowering the barrier for known devices while increasing it for high-value transactions from new locations.
- Sliding Scales: Using a 1-100 risk score that allows for secondary “step-up” authentication instead of an outright decline.
- Adaptive Logic: The system automatically relaxes rules during high-traffic periods like Black Friday to maintain high conversion rates.
3. Champion-challenger model frameworks
To prevent mistakes, elite systems run two models at once: a proven “Champion” that makes live decisions and a “Challenger” that tests new theories in the background.
This allows you to prove a new, more accurate model works on real data before you let it touch your actual customer transactions.
- Shadow Testing: Running new AI models in “read-only” mode to see how many false positives they would have prevented.
- Safe Innovation: Rolling out updates to 5% of traffic first to ensure the change doesn’t accidentally block legitimate revenue.
- Data-Driven Confidence: Only promoting a Challenger model to Champion status when it proves it is more accurate than the incumbent.
4. Human-in-the-loop decision design
AI is powerful, but complex enterprise cases often require a human touch to provide the final “sanity check” on high-value alerts.
By designing a workflow where AI does the heavy lifting and humans handle the nuances, you ensure that your most important clients never face a robotic rejection.
- Tiered Review: Automatically routing “grey area” transactions to a human analyst for a 30-second review.
- Augmented Intelligence: Providing the human reviewer with the exact data points the AI found suspicious to speed up the decision.
- Final Authority: Ensuring that for high-stakes business payments, a human always has the power to override a machine-generated flag.
5. Continuous model tuning with feedback loops
The only way to keep false positives low over time is to tell the AI when it was wrong so it can learn from its mistakes. By feeding data from customer support resolutions and manual overrides back into the model, the system becomes smarter and more precise with every transaction.
- Resolution Tracking: Marking a previously flagged transaction as “safe” once a customer verifies their identity.
- Model Recalibration: Automatically adjusting the weight of specific signals if they are found to be causing too many “false alarms.”
- Precision Training: Focusing the model’s learning on the specific user segments that are currently experiencing the most friction.
Solving the false positive problem transforms your fraud system from a defensive cost center into a powerful growth engine. When your security is smart enough to recognize your best customers, you can scale your platform with the confidence that your revenue is protected, not blocked.
How We Build An AI-Driven Fraud Detection System
At Intellivon, we approach fraud detection as a precision engineering challenge rather than a simple software installation.
Our methodology focuses on creating a responsive, high-speed ecosystem that protects your capital while ensuring your legitimate users experience zero friction.
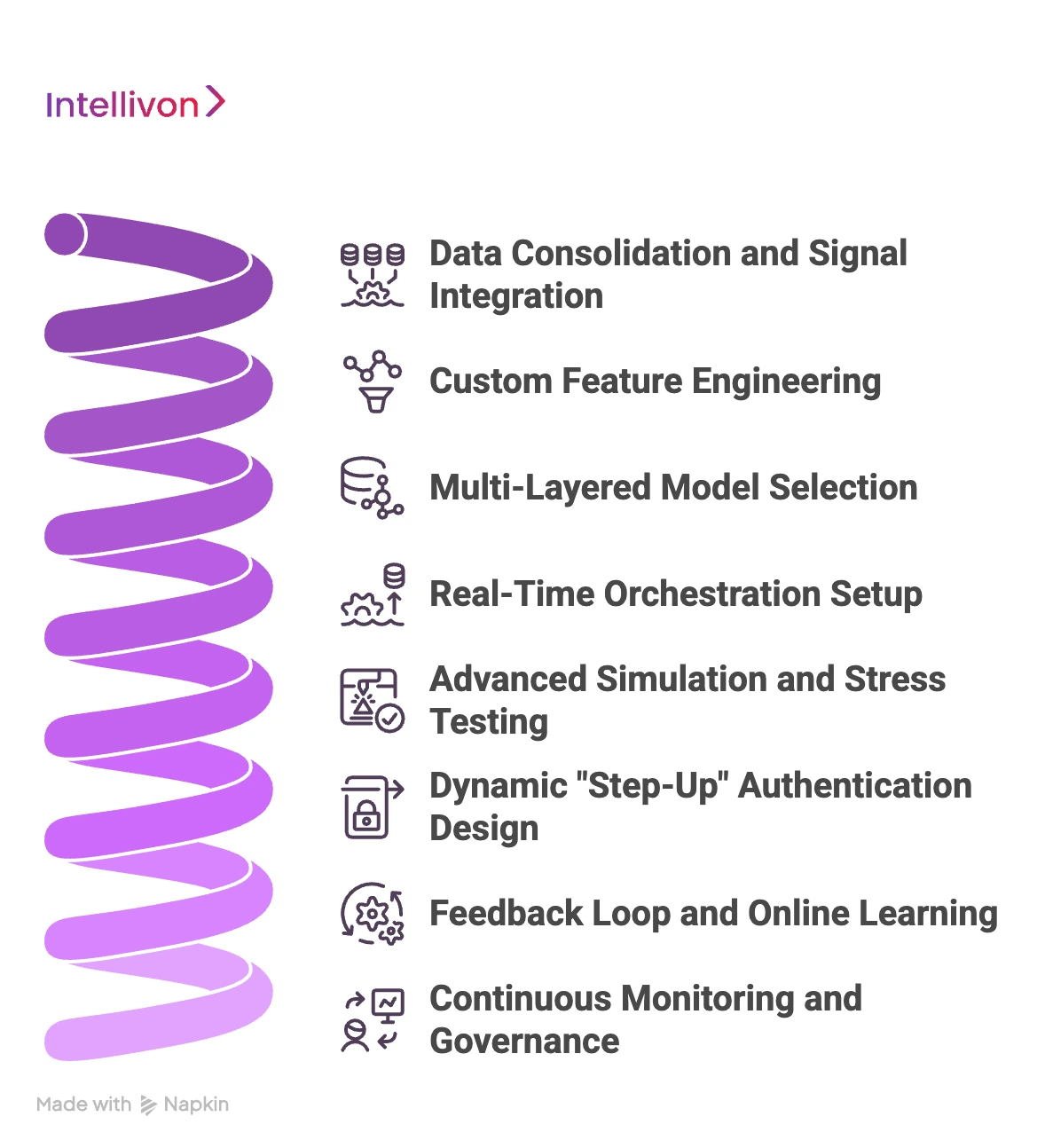
Step 1: Data Consolidation and Signal Integration
We begin by breaking down data silos to create a unified stream of every interaction on your platform. By integrating payment metadata, device fingerprints, and behavioral biometrics, we build the foundation for a 360-degree view of risk.
- Universal Ingestion: Collecting data from mobile, web, and API channels simultaneously.
- Contextual Enrichment: Adding external intelligence like IP reputation and global blacklists to every transaction.
- Identity Mapping: Linking disparate events to a single persistent user profile to track behavior over time.
Step 2: Custom Feature Engineering
Our team identifies the specific variables that define “normal” behavior for your unique business model. We build specialized feature stores that track everything from transaction velocity to subtle navigation patterns, providing the AI with the context it needs.
- Behavioral Baselines: Calculating moving averages for spend, frequency, and geographic patterns.
- Temporal Windows: Analyzing how current actions relate to the last 60 minutes of account activity.
- Signal Isolation: Removing “noise” from the data to ensure the models focus on high-impact indicators of risk.
Step 3: Multi-Layered Model Selection
We deploy a sophisticated ensemble of models tailored to your specific threats. From Gradient Boosting for speed to Graph Neural Networks for uncovering fraud rings, we match the math to the mission.
- Algorithm Diversity: Using a mix of supervised and unsupervised learning to catch all fraud types.
- Score Calibration: Ensuring that different models communicate their findings in a standardized risk format.
- Resource Optimization: Tuning models to provide high-accuracy results within your specific infrastructure limits.
| Build Strategy | Standard Vendor Approach | Intellivon Engineering |
| Model Type | One-size-fits-all API | Custom ensemble architecture |
| Data Usage | Basic transaction details | Deep behavioral + device signals |
| Adaptability | Manual rule updates | Real-time online learning |
| Latency | Variable/Slow | Guaranteed sub-200ms |
Step 4: Real-Time Orchestration Setup
We configure a high-performance decision engine that can process complex risk scores in milliseconds. This layer ensures that every transaction is scrutinized against your business logic without adding a single second of delay to the user experience.
- High-Throughput Processing: Building pipelines capable of handling thousands of transactions per second.
- Logic Routing: Directing transactions to different workflows based on their specific risk profile.
- Fail-Safe Protocols: Ensuring the system remains operational even during peak traffic or infrastructure stress.
Step 5: Advanced Simulation and Stress Testing
Before going live, we run your historical data through the new system to prove its accuracy. This “backtesting” phase allows us to fine-tune thresholds and ensure the system catches fraud while maintaining high approval rates for honest users.
- Precision Testing: Measuring exactly how many fraud cases the system would have caught in the past.
- Recall Analysis: Identifying any “blind spots” in the model before they affect live revenue.
- User Impact Audit: Estimating the friction legitimate users might face under the new security settings.
Step 6: Dynamic “Step-Up” Authentication Design
We implement intelligent friction, triggered only when the AI detects genuine uncertainty. This might include automated biometric checks or SMS codes, ensuring high security only appears when the risk score justifies the intervention.
- Adaptive Friction: Allowing low-risk users to check out instantly while challenging suspicious ones.
- Multi-Modal Verification: Supporting face ID, fingerprints, or secure push notifications.
- Experience Optimization: Reducing “cart abandonment” by only asking for verification when absolutely necessary.
Step 7: Feedback Loop and Online Learning
We build a closed-loop system where every confirmed fraud case or manual override retrains the model. This ensures your defense isn’t a static wall, but a living organism that evolves alongside the latest criminal tactics.
- Automated Labeling: Integrating chargeback and support data directly back into the training set.
- Model Evolution: Updating weights and features automatically to counter new “zero-day” attack strategies.
- Accuracy Verification: Constantly auditing the system to ensure it becomes more precise with every transaction.
Step 8: Continuous Monitoring and Governance
Post-deployment, our team provides ongoing oversight to manage model drift and adapt to changing market conditions. We ensure your system remains compliant with global regulations while consistently hitting your performance and revenue targets.
- Drift Detection: Monitoring if user behavior shifts and adjusting the models accordingly.
- Compliance Alignment: Ensuring your data handling meets GDPR, PCI-DSS, and local financial laws.
- Performance Reporting: Providing C-suite dashboards that show saved revenue and operational efficiency gains.
Partnering with Intellivon means moving from a reactive “catch-me-if-you-can” posture to a proactive, data-driven defense. We handle the technical complexity so you can focus on scaling your platform with absolute confidence in your financial integrity.
How Much Does It Cost to Build an AI Fraud Detection System?
There is no fixed cost, because fraud detection systems vary widely in complexity, scale, and regulatory requirements. However, most enterprise payment systems fall within a predictable investment range based on scope.
The key cost drivers are real-time infrastructure, data pipelines, model complexity, and compliance requirements, not just development effort.
Cost Range Based on System Scope
| Build Scope | Timeline | Investment Range | What’s Included |
| MVP (Basic ML + Rules) | 2–3 months | $10,000 – $25,000 | Basic transaction scoring, limited signals, batch or near real-time detection |
| Mid-Level System | 3–5 months | $25,000 – $50,000 | Real-time scoring, feature engineering, behavioral analysis, basic explainability |
| Enterprise-Grade System | 5–8 months | $50,000 – $80,000 | Multi-model AI, <200ms decisioning, full payment integration, compliance-ready architecture |
Cost Breakdown by System Components
| Component | % of Total Cost | Why It Matters |
| Data Pipelines & Engineering | 20–25% | Collecting and processing payment, device, and behavioral data |
| Model Development | 15–20% | Training and optimizing fraud detection models |
| Real-Time Infrastructure | 20–25% | Streaming, low-latency scoring, and scaling systems |
| Integration with Payment Systems | 15–20% | Connecting with gateways, processors, and banking systems |
| Compliance & Explainability | 10–15% | Audit trails, SHAP explanations, and regulatory readiness |
Key Cost Drivers You Should Expect
- Real-Time Infrastructure: Streaming systems like Kafka or Kinesis, low-latency APIs, and scalable cloud architecture significantly impact cost.
- Data Engineering and Feature Pipelines: Building reliable pipelines for transaction, behavioral, and device data often takes more effort than model development.
- Model Development and Tuning: Costs increase with model complexity, especially when combining multiple models for higher accuracy and lower false positives.
- Integration With Payment Systems: Connecting fraud detection to gateways, processors, and core systems requires careful engineering to avoid transaction delays.
- Compliance and Explainability: Implementing audit logs, explainability (like SHAP), and regulatory reporting adds both development and infrastructure overhead.
What Impacts Long-Term Cost the Most
The highest ongoing cost is maintaining model accuracy over time.
- Fraud patterns evolve rapidly, requiring continuous retraining
- Data pipelines must remain stable under scale
- False positives need constant optimization to protect revenue
A poorly maintained system can quickly become ineffective, even if the initial build was strong.
How to Optimize Cost Without Compromising Performance
Instead of overbuilding from day one, most payment companies take a phased approach:
- Start with a focused ML model + key fraud signals
- Add real-time infrastructure as transaction volume grows
- Introduce advanced models (graph, anomaly detection) only when needed
This reduces upfront cost while ensuring the system evolves with your fraud exposure.
At Intellivon, we don’t give generic estimates. We map your fraud exposure, data readiness, and system complexity to give you a realistic cost range and architecture direction.
- Understand what your fraud system actually needs to include
- Identify cost drivers specific to your payment flows
- Get a clear estimate based on your scale and risk profile
If you’re evaluating whether to build, buy, or upgrade your fraud detection stack, this is the fastest way to get clarity. Request a custom quote and system breakdown from Intellivon.
Conclusion
Modern fraud moves at machine speed, requiring an adaptive, AI-driven defense to protect your growth. By prioritizing real-time prevention and seamless user experience, you transform security into a powerful competitive advantage.
Secure your future by investing in an intelligent infrastructure that identifies threats before they impact your bottom line.
Build AI-Driven Fraud Detection Systems With Intellivon
Building an AI-driven fraud detection system for payments is not just about models—it’s about designing a system that can make accurate decisions in milliseconds without disrupting legitimate transactions.
At Intellivon, we build fraud detection infrastructure where real-time intelligence, payment performance, and regulatory compliance operate as a single system.
Our approach ensures your platform can detect evolving fraud patterns while maintaining low false positives, fast approvals, and complete auditability.
A. Designing Real-Time Fraud Detection Architectures
Fraud detection in payments is a real-time problem. We design systems that score transactions instantly without introducing latency or friction in the payment flow.
- Low-latency scoring pipelines built for sub-200ms decisions
- Event-driven architecture using streaming systems like Kafka
- Tiered decision engines for approve, block, and escalation flows
- Seamless integration into card, ACH, and real-time payment rails
This ensures fraud checks happen within the transaction lifecycle, not after the damage is done.
B. Building Multi-Layered AI Detection Systems
Effective fraud prevention requires more than a single model. We design layered AI systems that combine multiple detection techniques for higher accuracy.
| Detection Layer | AI Implementation | Operational Benefit |
| Transaction Scoring | Gradient boosting models for real-time risk scoring | Fast and explainable fraud decisions |
| Behavioral Analysis | Sequence models for user activity patterns | Detects subtle deviations in user behavior |
| Network Detection | Graph models for fraud ring identification | Uncovers coordinated fraud attacks |
| Anomaly Detection | Unsupervised models for unknown fraud types | Captures new and evolving threats |
This layered approach reduces fraud risk while minimizing false positives that impact revenue.
C. Embedding Explainability and Compliance Into the System
Fraud detection systems must also be explainable and compliant under regulatory scrutiny.
- Transaction-level explanations using SHAP-based model outputs
- Complete audit trails for every fraud decision and system action
- PCI DSS and GDPR-aligned data handling and storage
- Role-based access and investigation workflows for compliance teams
This ensures your system is not just accurate, but defensible in audits and regulator reviews.
D. Integrating Fraud Detection Into Payment Infrastructure
Fraud detection is only effective when it works seamlessly with your payment systems. We build integration layers that connect intelligence directly to transaction flows.
- API-first architecture for real-time fraud checks
- Integration with gateways, processors, and core banking systems
- Unified fraud signals across card, ACH, and RTP transactions
- Zero-disruption deployment into existing payment environments
This allows your fraud system to operate as a native part of your payment stack, not an external dependency.
E. Continuously Improving Fraud Detection Performance
Fraud evolves constantly, and so should your system. We design feedback-driven architectures that improve detection accuracy over time.
- Automated feedback loops from chargebacks and confirmed fraud
- Continuous model retraining and drift detection
- Performance monitoring across fraud rates and false positives
- Optimization frameworks to balance risk and user experience
This ensures your fraud detection system stays effective as attack patterns change.
Planning to Build or Upgrade Your Fraud Detection System?
At Intellivon, we help you map your fraud exposure, transaction scale, and system complexity into a clear architecture and cost estimate.
Talk to our team to get a tailored fraud detection strategy and project estimate.
FAQs
Q1. How accurate are AI fraud detection systems?
A1. Modern systems achieve significantly higher accuracy than rule-based filters by analyzing thousands of variables simultaneously. Leading models can identify over 95% of fraudulent attempts while keeping false positives below 1%. This precision allows businesses to automate the vast majority of their transaction monitoring, reducing the need for expensive and slow manual review processes.
Q2. How long does it take to build one?
A2. A basic proof-of-concept can be deployed within eight to twelve weeks using existing data streams. However, a fully integrated, enterprise-grade architecture typically requires six months to refine. This timeline includes data consolidation, custom feature engineering, and rigorous stress testing to ensure the system handles real-world traffic volumes without compromising speed or security.
Q3. Can small fintechs build fraud systems in-house?
A3. While possible, building in-house requires a highly specialized team of data scientists and engineers, which is often cost-prohibitive. Small firms usually find more value in partnering with specialists to deploy a custom architecture. This approach provides access to sophisticated models and global threat intelligence without the massive overhead of maintaining a dedicated internal research department.
Q4. What data is required for fraud detection models?
A4. Successful models require a mix of transaction metadata, device fingerprints, and historical user behavior. Key signals include IP addresses, geolocation, session duration, and even behavioral biometrics like typing patterns. The more diverse the data points, the better the AI can differentiate between a legitimate account holder and a sophisticated bot or synthetic identity.
Q5. How do you reduce false positives in payments?
A5. Reducing false positives requires moving away from rigid thresholds toward dynamic risk scoring. By using “champion-challenger” frameworks, you can test new models against real data in a safe environment before going live. Additionally, implementing a feedback loop ensures that when a human overrides a flag, the AI learns to approve similar transactions in the future.