As enterprises move from crypto exploration to real operations, they must secure digital asset custody without risking loss, regulatory issues, or operational failure. Traditional custody models lack the governance, access controls, and audit trails enterprises require. At the same time, many off-the-shelf solutions force a trade-off between security and scalability.
Creating a dedicated digital asset custody platform changes everything. Unlike patched-up banking systems or generic SaaS tools, it is built from scratch to meet high security standards, follow regulations, and handle operational scale, all at once. It not only protects what enterprises hold today but also establishes a strong base for their future digital asset goals.
At Intellivon, we have partnered with large companies to develop custody infrastructure that meets high security standards, fits into existing compliance processes, and grows as your digital asset strategy evolves. This blog explains how we develop these platforms from the ground up.
Why Digital Asset Custody Has Become Critical Infrastructure
Digital asset custody has evolved from a niche security concern into the bedrock of modern corporate finance. Establishing this infrastructure is the first step toward long-term institutional resilience and strategic growth. Therefore, understanding the factors driving this shift is essential for any enterprise looking to secure its digital future.
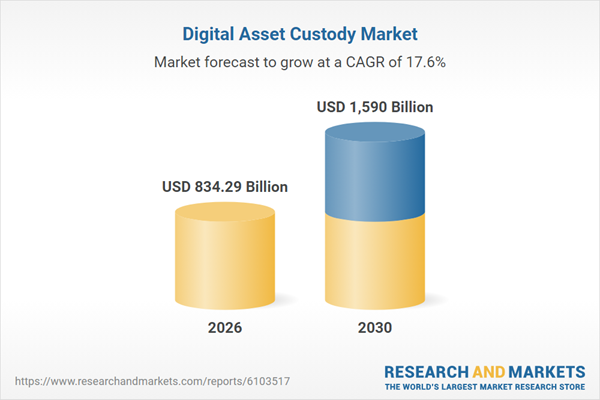
The digital asset custody market has expanded quickly in recent years. In 2025, the market size is estimated at $708.09 billion. It is expected to reach $834.29 billion in 2026. This represents a compound annual growth rate (CAGR) of 17.8%, highlighting strong institutional demand for secure digital asset storage infrastructure.
1. Institutional Adoption Is Driving Custody Demand
The landscape of institutional investment underwent a seismic shift over the last year. According to the Digital Asset Custody Market Report 2026, the global market for these services is projected to grow to $834.29 billion in 2026.
Institutional-grade custody has become the primary prerequisite for this participation. Recent data from Morgan Stanley Research indicates that crypto ETPs briefly exceeded $200 billion in assets under management in early 2026.
These funds received over $40 billion in fresh inflows despite market volatility. This demand is transforming custody from a back-office technicality into a strategic front-office enabler.
2. Why Enterprises Cannot Rely on Exchange Custody
Relying on a centralized exchange for asset safekeeping introduces a concentration of risk that most enterprise risk committees find unacceptable. In 2025, security breaches remained a critical threat. Specifically, the Bybit breach resulted in a $1.5 billion loss. When you store assets on an exchange, you hold a legal claim against the provider rather than direct ownership.
3. Operational Risks Enterprises Must Eliminate
Security in the digital asset space is not just about stopping external hackers. It is also about managing internal vulnerabilities effectively. Many businesses still face significant single-point-of-failure risks.
For instance, the loss of a single private key could lead to a permanent loss of funds. Eliminating this risk requires moving toward advanced cryptographic solutions like Multi-Party Computation (MPC).
How Custody Platforms Support Institutional Participation
A professional custody platform does more than just lock assets away. It makes them productive for the business. By providing secure rails, these platforms allow institutions to participate in decentralized finance (DeFi).
They also enable firms to engage in staking for yield or utilize stablecoins for instantaneous cross-border payments. The custody layer becomes the operating system for the digital economy.
Furthermore, modern platforms solve the regulatory alignment puzzle. They bake compliance, such as Anti-Money Laundering (AML) and Know Your Customer (KYC) checks, directly into the transaction flow.
What Is an Enterprise Digital Asset Custody Platform?
An enterprise digital asset custody platform is a specialized financial infrastructure designed to secure, manage, and settle blockchain-based assets. Unlike retail wallets, these systems integrate Multi-Party Computation (MPC) to eliminate single points of failure.
They provide granular governance frameworks, automated compliance engines, and seamless API connectivity. This allows large organizations to hold digital assets while maintaining the highest standards of institutional-grade risk management and 100% audit readiness.
Core Purpose of Institutional Custody Systems
Institutional custody systems serve as the critical bridge between decentralized assets and traditional corporate governance. These platforms transform the raw technical power of blockchain into a structured environment where digital asset custody remains secure, transparent, and fully auditable.
Consequently, they allow organizations to engage with the digital economy without compromising on internal risk mandates.
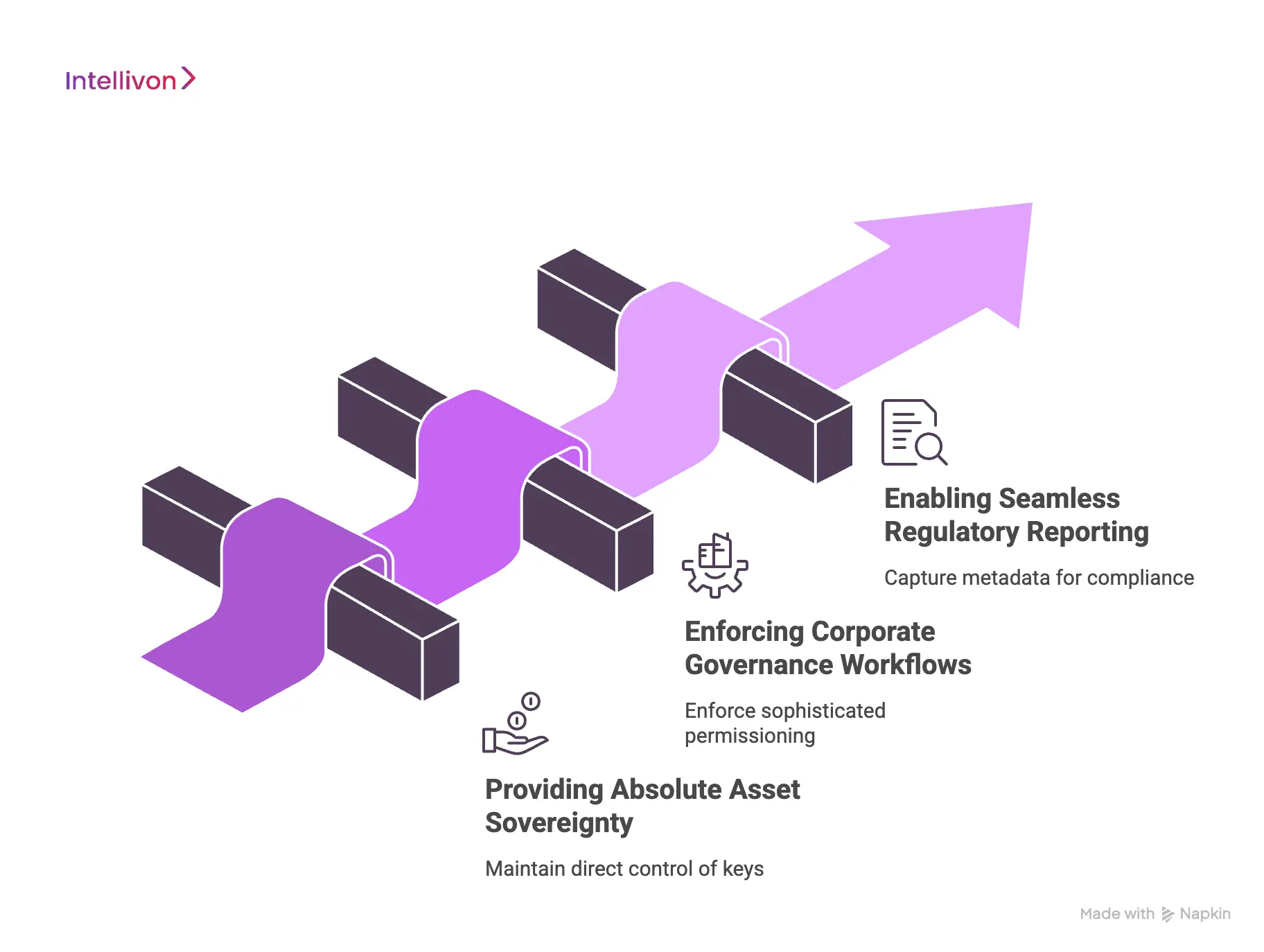
1. Providing Absolute Asset Sovereignty
A primary objective of any institutional system is to ensure the enterprise maintains direct control over its private keys. In the realm of digital asset custody, sovereignty means that no third party can freeze or move funds without explicit organizational approval.
Therefore, the system architecture must eliminate dependency on external providers while providing a user-friendly interface for complex cryptographic operations.
2. Enforcing Corporate Governance Workflows
Large organizations require sophisticated permissioning that reflects their actual management structure. Institutional systems allow leaders to build multi-signature approval chains where transactions only execute after reaching a specific consensus.
By embedding these rules into the digital asset custody layer, the platform prevents unauthorized transfers and ensures that every movement of capital aligns with board-approved policies.
3. Enabling Seamless Regulatory Reporting
Compliance is not an afterthought but a core function of institutional-grade infrastructure. These systems automatically capture the metadata required for tax, accounting, and Anti-Money Laundering (AML) reporting.
Because every transaction is recorded on a tamper-proof ledger, the digital asset custody platform provides a “golden record” that significantly simplifies the annual audit process for the finance department.
The successful deployment of these systems ensures that an enterprise can scale its digital operations with total confidence. By prioritizing these core purposes, a firm builds a resilient foundation for all future blockchain initiatives.
Difference Between Retail Wallets and Custody Platforms
Retail wallets and enterprise custody platforms serve different purposes. Retail wallets focus on individual users and simple asset storage. Custody platforms are designed for organizations managing large volumes of digital assets.
Because enterprises operate under regulatory and operational constraints, custody platforms include governance controls, approval workflows, and institutional security infrastructure.
Retail Wallets vs Enterprise Custody Platforms
| 1. Feature | Retail Wallets | Enterprise Custody Platforms |
| 2. Primary Users | Individual users managing personal digital assets | Financial institutions, fintech platforms, and asset managers |
| 3. Key Ownership | User directly controls the private keys | Keys managed through secure custody infrastructure |
| 4. Security Model | Basic encryption and user-controlled key storage | Multi-layer security using MPC, HSMs, and multi-signature policies |
| 5. Governance Controls | No structured approval workflows | Role-based access and multi-party transaction approvals |
| 6. Compliance Support | Minimal compliance and audit functionality | Built-in compliance reporting and audit trails |
| 7. Operational Scale | Designed for personal transactions | Designed for institutional asset management |
| 8. Integration Capabilities | Limited integrations with external systems | APIs and integrations with exchanges, banks, and trading systems |
Custody platforms extend beyond simple storage. They combine security, governance, and operational oversight to support enterprise digital asset management safely.
Key Participants in Enterprise Custody Ecosystems
Managing a digital asset custody architecture involves a diverse array of stakeholders and technical providers.
Therefore, identifying these key players is essential for any enterprise looking to build a resilient and fully integrated ecosystem.
1. Regulated Custodians and Sub-Custodians
Regulated custodians provide the legal and insurance framework necessary for institutional participation. These entities hold the appropriate licenses to safeguard assets on behalf of third parties.
By utilizing a regulated digital asset custody provider, an enterprise reduces its counterparty risk significantly.
2. Technology Infrastructure Providers
Infrastructure providers supply the underlying cryptographic engines, such as Multi-Party Computation (MPC) or Hardware Security Modules.
These firms focus on the technical side of securing private keys against sophisticated cyber threats.
3. Compliance and Risk Management Officers
Internal compliance teams use the custody platform to monitor for suspicious activity and maintain strict standards.
These participants define the risk parameters and approval thresholds that the system must enforce automatically. Their involvement ensures that every interaction within the digital asset custody environment aligns with legal obligations.
Types of Digital Asset Custody Models Enterprises Use
Before a single line of code is written or a vendor is evaluated, enterprises face one foundational decision: who controls the keys?
In digital asset management, key control is asset control. The custody model an enterprise selects shapes everything downstream, from security architecture and compliance posture to operational flexibility and counterparty risk.
The right model depends on asset scale, regulatory environment, internal technical capability, and board-approved risk tolerance. Understanding how each model performs under real operational pressure gives decision-makers the clarity to choose with confidence.
1. Self-Custody Platforms for Institutional Control
Self-custody means the enterprise holds and manages its own private keys with no third party involved. For organizations with the technical infrastructure to do this responsibly, it delivers the highest degree of control available.
Institutional self-custody typically involves MPC key management, hardware security modules, role-based access controls, and air-gapped signing environments.
2. Third-Party Institutional Custody Providers
Third-party custody transfers key management to a regulated, purpose-built custodian. The enterprise retains legal ownership while the custodian handles the operational burden of securing assets.
Leading institutional custodians offer segregated cold storage, insurance coverage, regulatory licensing, and SOC 2 Type II audit reports. These factors often satisfy fiduciary obligations more cleanly than self-custody, particularly for publicly listed enterprises.
The trade-off is dependency. This is because enterprises cede direct control over transaction speed and workflow customization. Therefore, rigorous vendor selection and strong contractual protections are non-negotiable, not optional considerations.
3. Hybrid Custody Infrastructure Models
Hybrid custody separates assets by liquidity need and risk profile. Enterprises keep frequently transacted assets accessible in hot or warm wallet layers while cold-storing long-term holdings under tighter controls.
This tiered approach delivers operational agility for daily treasury functions without exposing the full asset base to online risk.
Hybrid models suit enterprises managing diverse digital asset portfolios across multiple use cases. Clear governance policies and automated monitoring are prerequisites, not afterthoughts.
4. Multi-Jurisdiction Custody Structures for Enterprises
For enterprises operating across borders, custody is as much a regulatory challenge as a technical one. A structure that satisfies US requirements may create compliance exposure under MiCA in Europe or FCA guidance in the UK.
Multi-jurisdiction structures address this by deliberately distributing custody infrastructure across legal entities and geographic locations. They also enable geographic redundancy.
If one jurisdiction’s regulatory environment shifts, the enterprise adapts without disrupting global operations.
The custody model an enterprise selects today directly determines its regulatory resilience, operational agility, and security posture tomorrow. Choosing the right structure from the outset is not a technical decision.
Custody Risk Frameworks Used by Enterprises For Digital Assets
Enterprises must approach digital asset custody with a rigorous risk management mindset that mirrors traditional financial controls. Transitioning into the digital realm requires a shift from physical vaulting to cryptographic and operational defense strategies.
Therefore, a comprehensive framework addresses five primary domains to ensure institutional resilience and capital preservation.
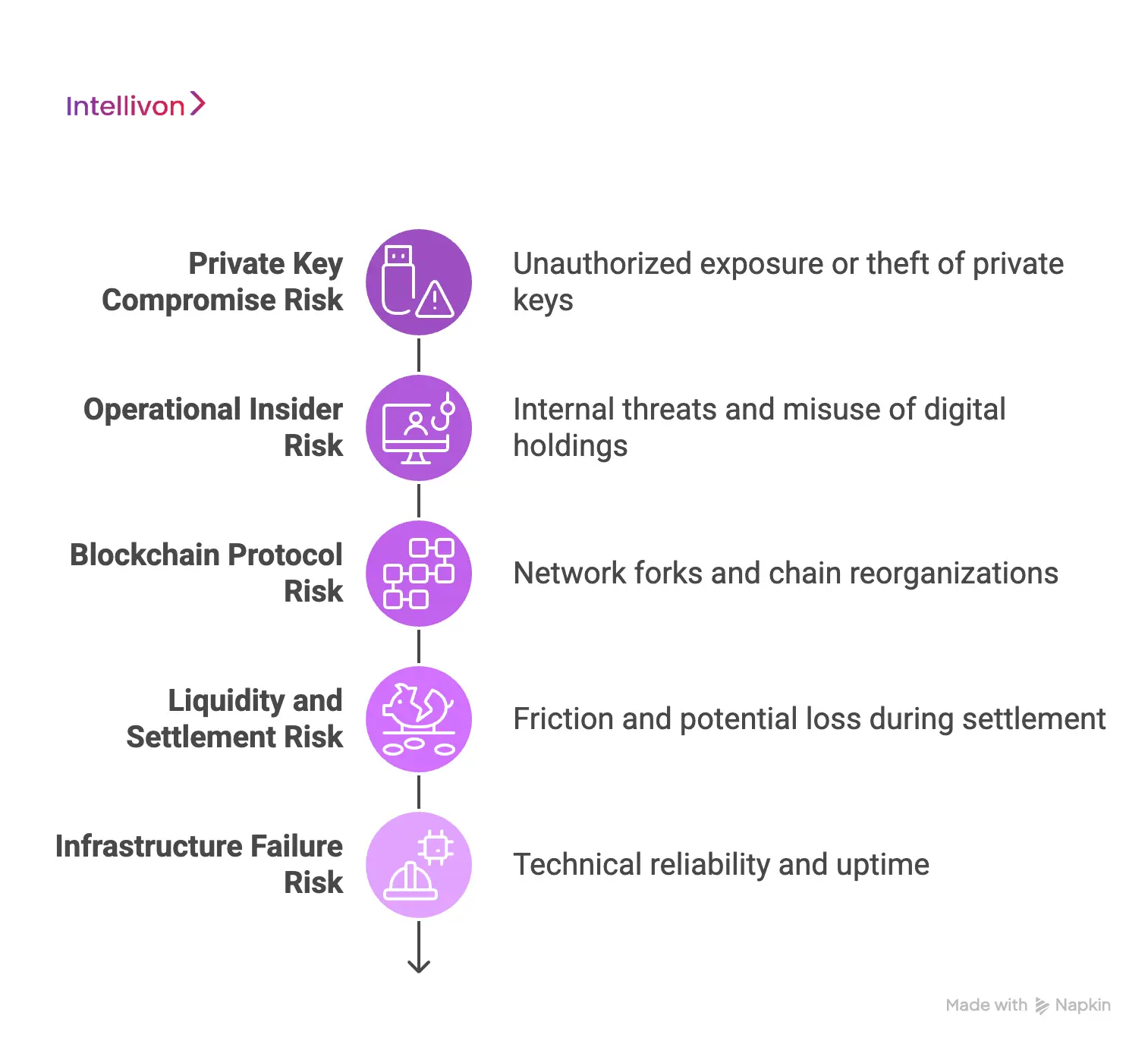
1. Private Key Compromise Risk
The most immediate threat in digital asset custody is the unauthorized exposure or theft of private keys. Because blockchain transactions are immutable, a compromised key leads to an irreversible loss of funds.
Therefore, modern systems utilize Multi-Party Computation to break the private key into encrypted shards.
- Distributed Sharding: Distributes key fragments across multiple isolated environments to prevent single points of failure.
- Hardware Protection: Employs Hardware Security Modules to provide a physical root of trust for key generation.
- Redundant Security: Combines hardware with multi-signature policies to ensure no single person can jeopardize the treasury.
2. Operational Insider Risk
Internal threats remain a significant concern for large organizations managing high-value digital holdings. Preventing misuse requires a strict separation of duties where no individual possesses the authority to both initiate and approve a transaction.
Consequently, digital asset custody platforms must enforce multi-user approval workflows that align with the company’s existing corporate hierarchy.
- Quorum Requirements: Implements mandatory multi-user consensus for any sensitive administrative changes or fund transfers.
- Audit Transparency: Records every transaction attempt in a tamper-proof log to ensure full accountability and detection.
- Role-Based Access: Limits system permissions based on specific corporate roles to minimize the internal attack surface.
3. Blockchain Protocol Risk
Beyond the custody platform itself, enterprises face inherent risks from the underlying blockchain networks. Events such as network forks or chain reorganizations can create temporary uncertainty regarding the finality of a transaction.
A professional digital asset custody solution monitors these protocol-level changes in real-time to prevent double-spend attacks.
- Fork Management: Provides automated tools to handle network splits and ensure assets remain secure on the correct chain.
- Finality Monitoring: Tracks block confirmations to confirm that transactions are mathematically irreversible before updating internal ledgers.
- Smart Contract Safety: Evaluates protocol-level security to protect the organization from catastrophic coding failures in decentralized apps.
4. Liquidity and Settlement Risk
Moving assets between different venues introduces friction and potential loss during the settlement window. When an enterprise transfers capital from a digital asset custody provider to an exchange, the assets are often temporarily unprotected.
This gap creates a window of vulnerability where counterparty insolvency could freeze the funds.
- Atomic Settlement: Utilizes simultaneous asset exchange technology to eliminate the need for risky pre-funding on exchanges.
- Off-Chain Networks: Connects to liquidity providers via secure settlement layers to reduce the time assets spend in transit.
- Counterparty Assessment: Integrates risk scoring to ensure that assets only move to verified and solvent trading desks.
5. Infrastructure Failure Risk
The technical reliability of the custody stack is essential for maintaining constant access to digital capital. Failures at the node level or data corruption within the internal ledger can stall critical business operations.
Therefore, a resilient digital asset custody architecture includes redundant node clusters to ensure 99.9% uptime.
- Node Redundancy: Maintains geographically distributed clusters to prevent service interruptions during local network or hardware failures.
- Automated Recovery: Employs backup systems that can restore access to funds instantly if the primary interface fails.
- Gas Optimization: Uses automated tools to manage network fees and ensure urgent transactions are never stuck in a queue.
A well-structured risk framework turns digital asset custody from a security burden into a competitive advantage. Leaders who prioritize these five domains build the trust necessary to scale their digital initiatives globally.
Security Architecture for Digital Asset Custody Platforms
Building a resilient security architecture is the primary challenge for any enterprise-grade digital asset custody solution. Therefore, designers must move beyond traditional perimeter defenses and adopt a “Zero Trust” model for cryptographic operations.
This structure ensures that every transaction is verified through multiple independent layers before it reaches the blockchain.
1. Multi-Party Computation (MPC) Key Management
MPC represents the current gold standard in cryptographic security for digital asset custody. Breaking the private key into encrypted shards, it ensures that a full key never exists in a single memory location.
Consequently, an attacker would need to breach multiple isolated servers simultaneously to compromise any funds.
- Mathematical Security: Uses advanced protocols to generate signatures without ever reconstructing the private key itself.
- Eliminating Single Failures: Removes the risk of a single server or administrator being a point of vulnerability.
- Flexible Deployment: Allows the enterprise to distribute key shards across different cloud providers or geographic regions.
2. Hardware Security Modules and Cold Storage
Enterprises often augment software-based security with physical Hardware Security Modules to create a hardened root of trust. These specialized devices generate and store cryptographic material within a tamper-proof physical boundary.
In addition, cold storage remains an essential layer for protecting long-term treasury reserves from online threats.
- Physical Isolation: Keeps a significant portion of assets completely offline to prevent remote hacking attempts.
- Tamper Resistance: Erases cryptographic material immediately if the physical hardware is compromised or opened.
- Strict Access Control: Requires physical presence and multiple authorized personnel to initiate transfers from deep storage.
3. Multi-Signature Transaction Authorization
Multi-signature (Multi-sig) protocols provide a layer of operational consensus that is fundamental to institutional digital asset custody.
These systems require a specific number of authorized participants to sign off on a transaction before it is broadcast. Therefore, the technology effectively digitizes the “two-key” vault system used in traditional finance.
- Quorum Logic: Configures the system to require a “M-of-N” approval ratio for any movement of capital.
- Policy Enforcement: Automatically blocks transactions that do not meet the predefined organizational approval criteria.
- Dynamic Workflows: Adjusts the number of required signers based on the transaction value or destination risk.
4. Key Recovery and Disaster Recovery Frameworks
A robust digital asset custody strategy must account for the permanent loss of access due to technical failure or personnel turnover.
Disaster recovery frameworks ensure that the organization can reconstruct its access to funds under extreme circumstances. Consequently, these plans must be tested regularly to ensure operational continuity.
- Social Recovery: Distributes recovery fragments among trusted executives or legal entities to prevent total asset loss.
- Offline Backups: Maintains encrypted physical copies of recovery materials in high-security, geographically separated vaults.
- Testing Protocols: Conducts simulated “fire drills” to ensure the recovery process works as intended during a crisis.
5. Threat Monitoring and Incident Response Systems
Proactive monitoring allows an enterprise to detect and neutralize threats before they result in a breach. Modern digital asset custody platforms integrate with Security Information and Event Management (SIEM) systems to track all administrative activity.
In addition, an incident response plan dictates the exact steps to take if an anomaly is detected.
- Real-Time Alerts: Notifies security teams immediately of any unauthorized login attempts or policy change requests.
- Automated Lockdowns: Freeze all outbound transactions automatically if the system detects suspicious behavioral patterns.
- Forensic Auditing: Provides a detailed, immutable record of every action taken within the platform for post-incident analysis.
This multi-layered architecture ensures that the enterprise maintains absolute control over its digital wealth. By investing in these security pillars, leaders can scale their operations without the fear of catastrophic technical failure.
Governance and Policy Controls in Custody Platforms
Effective digital asset custody demands a rigorous governance framework. Therefore, institutional leaders must implement policy controls that mirror the sophisticated hierarchies of traditional finance.
This structure ensures that every movement of capital is intentional, authorized, and fully documented for internal stakeholders.
1. Role-Based Access Controls for Institutional Teams
Role-Based Access Control (RBAC) is the primary tool for managing human interaction within a digital asset custody environment. It ensures that employees only access the specific functions required for their professional responsibilities.
Consequently, this granular approach limits the potential impact of a single compromised credential.
- Granular Permissions: Assigns specific read or write access based on the user’s role in the organization.
- Identity Integration: Connects with existing enterprise identity providers like Okta or Azure AD for seamless management.
- Credential Security: Mandates hardware-based multi-factor authentication for every login attempt to the custody platform.
2. Transaction Approval Workflows and Policy Rules
Approval workflows act as the automated guardians of an organization’s digital wealth. By defining “If-Then” logic, a digital asset custody platform can automatically flag or block transactions that fall outside of normal parameters.
Therefore, the system enforces corporate policy without requiring constant manual oversight from leadership.
- Threshold Logic: Requires additional executive approvals for any outgoing transfer that exceeds a specific dollar amount.
- Whitelisting Addresses: Restricts fund movements to a pre-approved list of verified counterparty wallets to prevent phishing.
- Time-Locking: Implements mandatory delays for large withdrawals to allow security teams time to investigate anomalies.
3. Separation of Duties Across Custody Operations
Separation of duties is a fundamental principle of internal control that prevents any single individual from having total power. In the context of digital asset custody, this means the person who initiates a transaction cannot be the one who approves it.
This protocol effectively eliminates the risk of a “rogue actor” within the corporate structure.
- Dual Control: Mandates that at least two distinct authorized users participate in any sensitive system change.
- Operational Segregation: Separates the technical administrators from the financial officers who manage the actual asset movements.
- Verification Chains: Requires a series of independent checks before the final cryptographic signature is ever generated.
4. Audit Trails and Regulatory Reporting Systems
A professional digital asset custody solution must be “audit-ready” at all times to satisfy global regulators. The platform generates a comprehensive, tamper-proof record of every login, policy change, and transaction attempt.
This transparency is essential for maintaining the “Golden Record” required by CFOs and external auditors.
- Immutable Logs: Stores all activity on a protected ledger that cannot be altered or deleted by any user.
- Automated Reporting: Generates real-time tax and compliance reports to simplify the burden of regulatory filings.
- Counterparty Tracking: Links every transaction to verified KYC data to ensure the firm meets all AML requirements.
Establishing these governance layers transforms digital asset custody into a predictable business process. When policy dictates technology, the enterprise achieves the balance between innovation and institutional safety.
Step-by-Step Process Of How We Build a Custody Platform
Developing an enterprise-grade digital asset custody platform is a multi-phase journey that balances cryptographic rigor with operational usability. Therefore, the build process must move systematically from conceptual governance to hardened technical execution.
By following this six-step blueprint, Intellivon helps organizations transition from initial strategy to a production-ready environment that satisfies both internal auditors and global regulators.
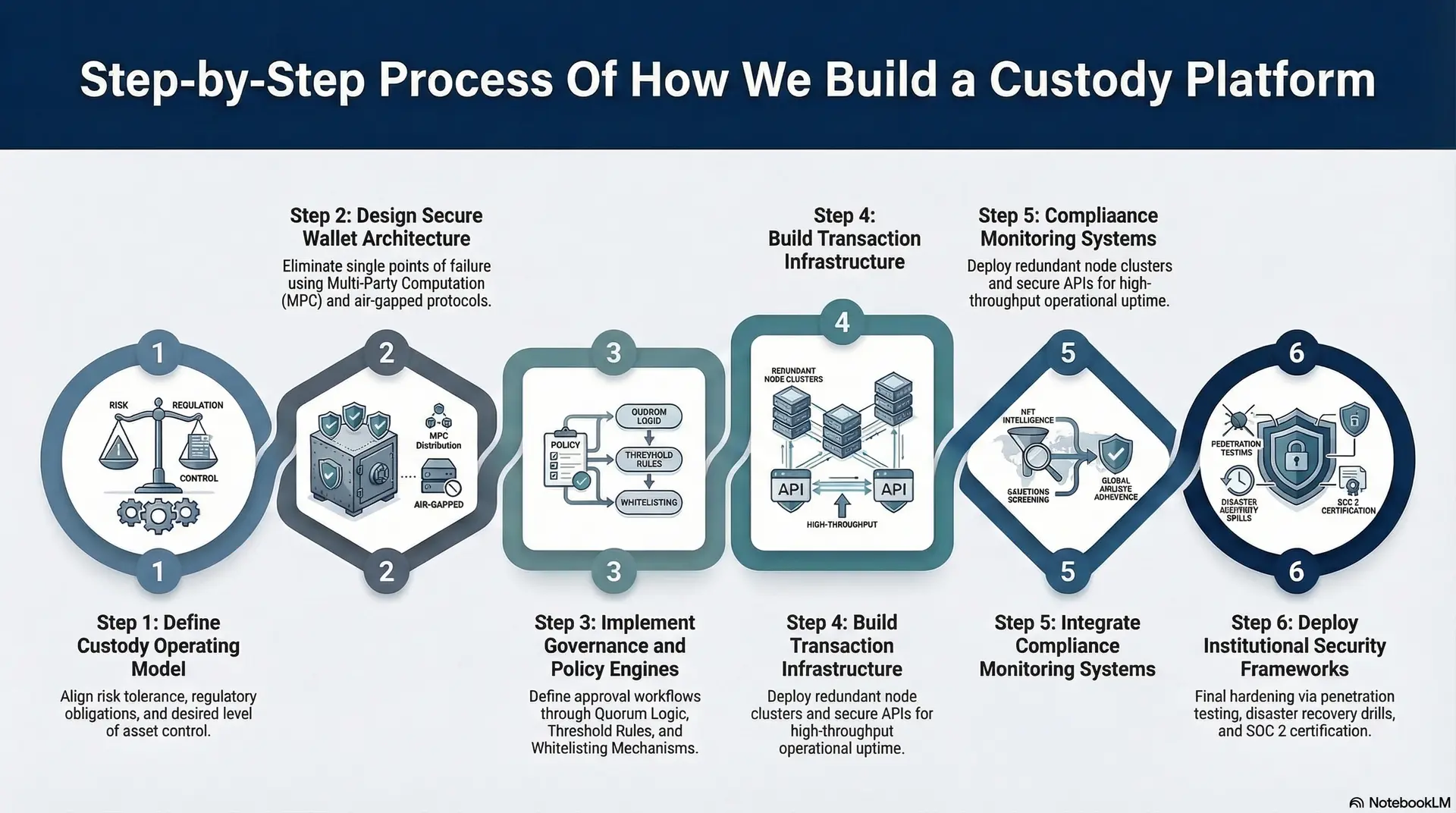
Step 1: Define Custody Operating Model
The first step involves determining whether your enterprise will utilize self-custody, a third-party provider, or a hybrid model. This decision dictates the entire technical and legal architecture of the platform we build for you.
Consequently, our team aligns this model with your specific risk tolerance, regulatory obligations, and desired level of asset control.
- Sovereignty Assessment: We help you decide if your firm will maintain direct control over private keys or delegate that responsibility to a qualified custodian.
- Asset Scope: Intellivon identifies the specific cryptocurrencies, stablecoins, or tokenized real-world assets the platform must support in its initial phase.
- Jurisdictional Alignment: We map the operating model to the legal requirements of the regions where you operate to ensure long-term compliance.
Step 2: Design Secure Wallet Architecture
Once the model is defined, our focus shifts to the underlying cryptographic structure of your wallets. Intellivon prioritizes a layered approach that combines hot wallets for immediate liquidity with cold storage for long-term reserves.
Therefore, our design eliminates any single point of failure through advanced technologies like Multi-Party Computation (MPC).
- MPC Distribution: We design a shard-management strategy that distributes key fragments across multiple isolated cloud and on-premise environments.
- Cold Storage Integration: Our engineers establish air-gapped protocols for high-value holdings to protect against remote cyber threats and internet-based exploits.
- Hardware Anchoring: We select FIPS 140-2 Level 3 certified Hardware Security Modules (HSMs) to provide a physical root of trust for key generation.
Step 3: Implement Governance and Policy Engines
A secure wallet is only effective if it is governed by strict organizational rules. In this stage, Intellivon builds the policy layer that defines who can move assets, under what conditions, and with whose approval.
Consequently, the platform transforms from a technical vault into a manageable corporate tool that reflects your actual management hierarchy.
- Quorum Logic: We implement “M-of-N” approval workflows where a specific number of your executives must sign off on any outgoing transfer.
- Threshold Rules: Our system sets automated limits on transaction values that trigger additional security checks or mandatory delays if exceeded.
- Whitelisting Mechanisms: Intellivon configures the system to only allow transfers to pre-verified and trusted counterparty addresses to prevent fraud.
Step 4: Build Transaction Infrastructure
With the security and governance layers in place, our focus turns to the digital plumbing that connects your platform to blockchain networks.
This stage involves building the APIs and node clusters required to broadcast transactions and monitor their status in real-time. Therefore, the infrastructure we deploy is designed for high throughput and 99.9% operational uptime.
- Node Cluster Deployment: We set up redundant full nodes across multiple geographic regions to ensure your platform can always communicate with the blockchain.
- API Development: Intellivon creates secure, high-speed interfaces that allow your internal treasury and portfolio systems to trigger transactions automatically.
- Gas Management Engines: We build automated tools to calculate optimal network fees, ensuring that your urgent institutional transfers are never stuck in a queue.
Step 5: Integrate Compliance Monitoring Systems
Institutional-grade digital asset custody requires real-time visibility into the risk profile of every transaction. This step involves integrating blockchain intelligence tools to screen for illicit activity and ensure adherence to global AML and KYC standards.
Consequently, the platform becomes compliance by design, protecting your firm from interacting with sanctioned or high-risk entities.
- KYT Intelligence: We link your platform to providers like Chainalysis or TRM Labs to score the risk of every incoming and outgoing transaction.
- Sanctions Screening: Intellivon automatically blocks interactions with wallet addresses appearing on global watchlists or associated with criminal activity.
- Travel Rule Readiness: Our team implements the protocols necessary to securely exchange originator and beneficiary information during cross-border transfers.
Step 6: Deploy Institutional Security Frameworks
The final step is the hardening of the entire ecosystem through rigorous testing and external audits. This ensures that the platform is not only technically sound but also resilient against a wide array of operational and cyber threats.
Therefore, the deployment phase marks the transition from a development project to a permanent pillar of your firm’s financial infrastructure.
- Penetration Testing: We subject the platform to simulated attacks from elite security firms to identify and patch any potential vulnerabilities.
- Disaster Recovery Drills: Intellivon conducts regular fire drills to verify that your team can reconstruct access to funds even during a catastrophic failure.
- SOC 2 Certification: We guide you through independent audits to prove that the platform’s security, availability, and confidentiality controls meet global standards.
By following this systematic process, we ensure that no critical security or compliance gap is overlooked.
Real Platforms Providing Digital Asset Custody
Enterprise adoption of digital asset custody has shifted from speculative holding to functional, day-to-day business operations.
Therefore, understanding these real-world use cases helps leaders visualize how to integrate these solutions into their own strategic roadmaps.
1. J.P. Morgan’s Kinexys (Formerly Onyx)
J.P. Morgan uses institutional-grade digital asset custody to power Kinexys, a blockchain-based platform for wholesale payments and tokenized collateral.
The system allows multinational corporations to move millions of dollars across borders instantly using JPM Coin. Consequently, the platform reduces settlement times from days to minutes by keeping assets within a secure, bank-led custody environment.
- Atomic Settlement: Enables simultaneous exchange of assets and cash to eliminate delivery risk during high-value trades.
- Intraday Repo Financing: Allows clients to use tokenized collateral for short-term borrowing, maximizing capital efficiency.
- Programmable Payments: Uses smart contracts to trigger fund transfers automatically when specific business conditions are met.
2. Ripple’s Enterprise Payments and Liquidity Hub
Ripple provides a comprehensive suite of digital asset custody and payment tools for financial institutions looking to modernize their “digital plumbing.”
In early 2026, Ripple expanded its platform to support end-to-end stablecoin management, allowing fintechs to collect, hold, and payout funds globally. Therefore, businesses can operate on-chain while maintaining the same rigor as traditional finance.
- Global Stablecoin Rails: Facilitates real-time cross-border settlements using licensed infrastructure that treats digital money with institutional oversight.
- Managed Custody Services: Provides secure, virtual accounts and wallets that allow firms to hold both fiat and digital assets in a single interface.
- Deep Liquidity Integration: Connects enterprises to global markets, ensuring they can exchange assets at scale without significant price slippage.
3. HSBC’s Orion and Tokenized Gold Platform
HSBC has pioneered the use of digital asset custody to transform how physical assets are traded and stored.
Through its HSBC Orion platform, the bank issues digital bonds and manages HSBC Gold Tokens, which represent physical gold held in its London vaults.
Consequently, this application brings a new level of liquidity and accessibility to the trillion-dollar gold market.
- Fractional Ownership: Allows institutional and retail investors to own small portions of physical gold bars through secure digital tokens.
- Blockchain Bond Issuance: Streamlines the entire lifecycle of a bond, from initial creation and recording to settlement and secondary trading.
- Next-Gen Custody: Integrates digital asset safekeeping directly into the bank’s existing global custodial network across 90+ markets.
4. Stripe’s B2B Crypto Payment Infrastructure
Stripe has integrated digital asset custody into its core product suite to enable faster and cheaper B2B cross-border transactions.
By utilizing stablecoins like USDC, Stripe allows businesses to bypass the slow and expensive correspondent banking system. Therefore, a company in the US can pay a supplier in Singapore in minutes rather than days.
- Automated On/Off Ramps: Converts local fiat currency into stablecoins and back again, handling the technical complexity for the user.
- ERP Synchronization: Feeds on-chain transaction data directly into accounting tools like QuickBooks or NetSuite for seamless reconciliation.
- Compliance at Scale: Embeds real-time wallet screening and AML monitoring into every payment to ensure regulatory certainty for the enterprise.
These applications demonstrate that digital asset custody is no longer a “crypto-only” technology. It is a fundamental tool for any organization seeking to lead in the multi-trillion-dollar digital economy.
Conclusion
Digital asset custody has transitioned from a security hurdle into a primary driver of institutional growth. By implementing MPC-based architectures and rigorous governance, your organization achieves the resilience required for the modern economy.
Therefore, securing your digital future is a strategic investment in long-term capital preservation. These platforms enable you to scale operations with absolute confidence and regulatory certainty. This infrastructure is the essential foundation for global financial leadership.
Build an Enterprise Custody Platform With Intellivon
At Intellivon, digital asset custody platforms are designed as institutional financial infrastructure, not as simple wallet systems layered onto blockchain networks. Every platform is built to support secure asset storage, governed transaction approvals, and regulatory readiness across complex enterprise environments.
Each solution is engineered for regulated financial ecosystems. Platforms remain secure under operational load, interoperable with financial systems, and adaptable as new blockchain networks and tokenized assets emerge.
Why Partner With Intellivon?
- Governance-First Custody Architecture: Custody systems are designed with embedded policy controls, approval workflows, and access governance. As a result, institutional oversight becomes part of the platform itself.
- Institutional Key Management Infrastructure: Our platforms integrate MPC, HSM-backed storage, and multi-signature transaction controls. This ensures secure private key protection across distributed operational environments.
- Multi-Chain Asset Support: Enterprises increasingly manage assets across multiple blockchain networks. Therefore, our custody platforms support secure storage and transfers across major digital asset ecosystems.
- Compliance-Ready Custody Infrastructure: Audit trails, reporting systems, and transaction monitoring tools are built directly into the platform. This enables enterprises to maintain regulatory visibility across custody operations.
- Enterprise Integration Capabilities: Custody platforms integrate with exchanges, trading systems, treasury platforms, and portfolio management tools. Consequently, digital asset operations remain aligned with existing financial workflows.
- Scalable Infrastructure for Institutional Growth:
Architecture is designed to support expanding asset volumes, new blockchain integrations, and global operational requirements without compromising security or governance.
If your organization is exploring institutional digital asset custody, Intellivon can help design and deploy a secure enterprise-grade platform built for long-term operational control and regulatory confidence.
FAQs
Q1. What is a digital assets custodian?
A1. A digital assets custodian is a service that securely stores cryptocurrencies and other blockchain-based assets for users or institutions. Custodians protect private keys and manage asset transfers. Institutional custodians also provide governance controls, transaction approvals, and compliance reporting. This helps enterprises manage digital assets securely.
Q2. How to build a digital asset management system?
A2. Building a digital asset management system starts with secure wallet infrastructure and private key management. The platform must support asset storage, transaction processing, and authorization workflows. Enterprises also integrate compliance monitoring, APIs, and security layers such as MPC or multi-signature controls.
Q3. What are the different types of digital asset custody?
A3. There are three main types of digital asset custody. They are self-custody (allows organizations to control their own private keys), third-party custody (involves regulated custodians storing assets for clients), and hybrid custody (combines internal control with external custody services).
Q4. Who is the largest crypto custodian?
A4. Several companies offer institutional crypto custody, including Coinbase Custody, BitGo, Anchorage Digital, and Fireblocks. Among them, Coinbase Custody is widely considered one of the largest custodians serving institutional investors.






