Key Takeaways:
-
HIPAA compliance must be designed into the architecture from day one, not patched later.
-
Data breaches in healthcare average $10.93 million, making PHI protection a financial necessity.
-
PHI appears across eligibility, coding, claims, authorizations, payments, and every AI workflow touchpoint.
-
Role-based access, AES-256 encryption, audit trails, and MFA are non-negotiable compliance requirements.
-
Intellivon builds HIPAA-aligned AI RCM platforms with secure pipelines, explainable AI, and payer integrations.
Healthcare revenue cycle teams are under pressure to process claims faster, reduce denials, verify eligibility, support coding, manage prior authorizations, and recover payments with fewer manual steps. AI can deliver on all of that, but only when it is built into infrastructure that protects patient health information at every stage of the revenue cycle.
A HIPAA-compliant AI RCM platform is a secure revenue intelligence system where patient data, claim data, payer rules, AI models, access controls, audit trails, encryption, human review workflows, and compliance controls operate together as one architecture. AI can meaningfully improve claim scrubbing, denial prediction, coding support, payment variance detection, and appeal workflows.
HIPAA must be designed into the architecture from the ground up. Organizations that skip that step expose themselves to audit risk, payer penalties, and patient data liability that no amount of billing efficiency can offset.
Intellivon builds HIPAA-aligned AI RCM platforms with secure data pipelines, AI-assisted workflows, payer integrations, audit controls, and revenue analytics for healthcare businesses that need both performance and compliance built into the same system. By the end of this blog, you will get an idea of how we build such platforms from the ground up.
Why Healthcare Businesses Are Building HIPAA-Compliant AI RCM Platforms
Healthcare businesses are building HIPAA-compliant AI RCM platforms because the financial risk of non-compliance is not theoretical. It is immediate, measurable, and in many cases, irreversible.
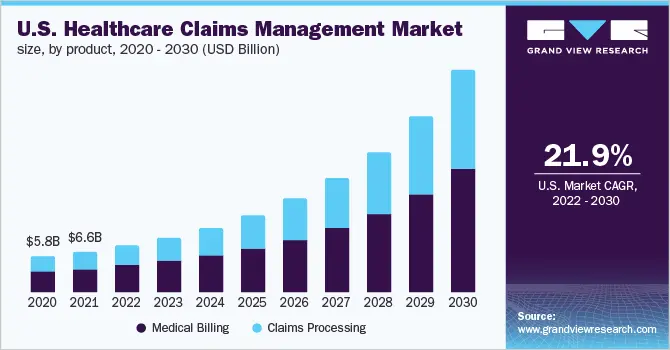
1. The Stakes Of HIPAA Non-Compliance Are Existential
Over 30,000 HIPAA violations are reported annually, with data breaches affecting 48.5 million individuals in 2023 alone. The average breach costs USD 10.93 million, the highest of any industry.
Penalties range from USD 100 to USD 50,000 per violation, rising to USD 50,000 or more for willful neglect with mandatory criminal exposure. For healthcare businesses building AI RCM infrastructure, compliance is therefore a legal and financial foundation, not an afterthought.
2. Why Generic AI Platforms Cannot Handle Healthcare Data
PHI protection requires de-identification using the Safe Harbor method, which removes 18 specific identifiers before any AI processing occurs. Generic AI platforms, however, lack built-in de-identification workflows.
Furthermore, encryption mandates require AES-256 at rest and TLS 1.3 in transit, while access controls demand unique user IDs, role-based permissions, and multi-factor authentication. Standard commercial AI tools consistently fall short on all three requirements.
3. Key Compliance Features Driving Custom Builds
Custom AI RCM platforms embed automatic PHI redaction, end-to-end encryption, immutable audit trails, and complete data ownership through controlled Business Associate Agreements.
Off-the-shelf vendors frequently claim HIPAA compliance but lack transparent security documentation, SOC 2 Type II audits, or verifiable data ownership guarantees.
That gap is precisely why serious healthcare businesses build rather than buy.
What Is A HIPAA-Compliant AI RCM Platform?
A HIPAA-compliant AI RCM platform brings three operational layers together into one secure system. AI improves decision-making across coding, claim validation, denial prediction, and payment variance detection.
RCM manages the full patient financial journey from registration through final payment. HIPAA safeguards ensure that every interaction with patient health information meets federal privacy and security requirements.
Those three layers must operate together, not independently. Compliance, therefore, cannot be limited to data storage. It must extend across:
- Data collection and intake: PHI captured and de-identified at the point of entry
- Storage and encryption: AES-256 at rest, TLS 1.3 in transit
- AI model processing: models trained and operated on de-identified or consented data
- Access and authentication: role-based permissions, unique user IDs, and multi-factor authentication
- Audit trails: immutable logs capturing every action across the platform
- Vendor management: Business Associate Agreements with every third-party integration
A platform that satisfies billing performance but handles PHI without proper safeguards is not a compliant system. It is a liability.
What Makes It Different From Regular RCM Software?
Traditional RCM software acts as a digital filing cabinet with a basic workflow engine attached.
It relies on humans to spot errors and manually follow up on unpaid claims. While these systems manage workflows, they are fundamentally reactive.
| Feature | Regular RCM Software | HIPAA-Compliant AI RCM |
| Primary Function | Data entry and workflow tracking | Predictive automation and intelligence |
| Handling Denials | Manual review after a rejection | Predictive flagging before submission |
| Security Focus | Standard encryption and passwords | Rigorous PHI governance and audit trails |
| Operational Logic | Static rules based on user input | Adaptive learning from historical data |
| Compliance | Basic regulatory adherence | Full explainability for AI decisions |
The inclusion of HIPAA compliance transforms the AI from a simple tool into a secure fortress. Regulatory standards require that every action taken by an algorithm be auditable and transparent. This ensures privacy remains intact while the machine optimizes the revenue stream.
What Makes It Different From A Generic AI Healthcare Tool?
Generic AI tools are often designed for broad tasks like summarizing notes or answering administrative questions. They provide assistance but lack the specialized logic required for complex financial operations and payer contract nuances.
| Feature | Generic AI Healthcare Tool | HIPAA-Compliant AI RCM Platform |
| Primary Objective | General administrative assistance | Revenue optimization and accuracy |
| Domain Logic | NLP for general text | Intelligence for coding and payers |
| Data Integration | Often operates as a standalone | Embedded in EHR and clearinghouse APIs |
| Financial Literacy | Minimal reimbursement knowledge | Expert knowledge of CPT and payer rules |
| Workflow Focus | Task-based (e.g., summaries) | Lifecycle-based (e.g., claim to settlement) |
These platforms do not operate in a vacuum and require deep technical integration with healthcare infrastructure. For example, the AI must communicate directly with Electronic Health Records and pull data from payer APIs.
Where PHI Appears In AI RCM Workflows
Protected Health Information is the lifeblood of the revenue cycle. It is present at every touchpoint from the moment a patient schedules an appointment until the final balance is settled.
PHI is frequently encountered in the following areas:
- Demographics and Insurance: Patient names and policy numbers used for eligibility.
- Clinical Records: Diagnosis and procedure codes extracted from physician notes.
- Financial Documents: Claim records and Explanation of Benefits with sensitive details.
- Authorization Files: Prior authorization documents, including medical histories.
- Communication Logs: Denial reasons and payer correspondence revealing care paths.
Understanding exactly where this data sits is critical for building a compliant architecture. Each of these data points must be encrypted both at rest and during transmission to prevent leakage.
Building these systems requires a deep understanding of how financial data flows through clinical environments. By securing these touchpoints, developers create a platform that balances automation with uncompromising patient privacy.
Core HIPAA Requirements To Understand
Building a platform that handles healthcare finances requires a deep commitment to federal regulatory standards. This section outlines the essential legal pillars that transform a standard AI tool into a trustworthy enterprise asset.
1. HIPAA Privacy Rule
The Privacy Rule establishes the baseline for protecting individually identifiable health information across all media. It dictates how healthcare providers and their partners can use or disclose sensitive patient data during the billing process.
- Regulated Entities: The rule applies to covered entities like hospitals and business associates like RCM vendors.
- Restricted Disclosure: It strictly limits PHI use to the minimum amount necessary for specific operations.
- Patient Rights: The rule supports the right of patients to access their records and request an accounting of disclosures.
- Operational Impact: These standards shape how RCM teams access, use, and share data with third-party payers.
HHS explains that the Privacy Rule establishes national standards to protect medical records and other individually identifiable health information. This creates a mandatory framework for any developer entering the healthcare space.
2. HIPAA Security Rule
The Security Rule focuses specifically on electronic protected health information (ePHI) and the technical environment where it lives. It requires a multilayered approach to ensure data remains confidential and unaltered.
- Administrative Safeguards: Policies and training that manage the selection and execution of security measures.
- Physical Safeguards: Controls that protect physical access to servers, data centers, and workstations.
- Technical Safeguards: Technology-driven solutions like encryption, multi-factor authentication, and automatic log-offs.
- Core Pillars: The focus remains on maintaining the confidentiality, integrity, and availability of all ePHI.
HHS states that the Security Rule requires regulated entities to implement administrative, physical, and technical safeguards to secure ePHI. This ensures that the infrastructure supporting your AI is as resilient as the code itself.
3. Covered Entity Vs Business Associate
Determining your legal status is the first step in establishing a compliant healthcare venture. Most AI RCM vendors operate as Business Associates because they provide specialized services to hospitals or clinics.
| Entity Type | Typical Examples | Role in PHI Ecosystem |
| Covered Entity | Hospitals, Private Practices, Health Plans | Directly provides care or pays for healthcare |
| Business Associate | AI Vendors, Billing Companies, Cloud Providers | Handles PHI on behalf of a Covered Entity |
HHS defines a business associate as a person or entity that performs functions or activities involving PHI on behalf of a covered entity. If your platform creates, receives, maintains, or transmits PHI, you fall into this territory.
4. Business Associate Agreement Readiness
A Business Associate Agreement (BAA) is a mandatory contract that defines the security responsibilities of the vendor. This document must be finalized and signed before a single byte of patient data enters the platform.
- Defined Scope: The BAA must clearly outline permitted uses of PHI and specific safeguard requirements.
- Downstream Protection: You must ensure that all subprocessors and cloud infrastructure providers have signed their own BAAs.
- Breach Obligations: The agreement sets the clock for reporting security incidents and coordinating with the covered entity.
- Data Lifecycle: It includes protocols for the return or destruction of data once the partnership ends.
Proactive BAA readiness builds immediate trust with enterprise prospects during the procurement phase. It signals that your platform is ready for the rigors of high-stakes healthcare environments.
5. Minimum Necessary Data Use
The “Minimum Necessary” standard is a core tenet of HIPAA that prevents over-exposure of patient data. AI models should only be granted access to the specific datasets required to perform their designated function.
- Task-Specific Access: A coding engine needs clinical notes but does not require a patient’s full payment history.
- Variance Detection: Tools identifying underpayments may need claim data but not unrestricted psychological evaluations.
- Denial Prediction: This function relies on structured payer data rather than every document in an EHR.
- Privacy by Design: Implementing granular data permissions ensures that AI training sets are lean and compliant.
By limiting data exposure, you reduce the overall risk profile of the platform. This strategic approach ensures that the AI remains effective without compromising the patient’s right to privacy.
6. Breach Notification Planning
No security system is perfect, which is why a robust breach notification plan is a legal necessity. Your platform must have a clear, documented workflow for detecting and responding to potential security incidents.
- Detection Systems: Real-time monitoring tools must be in place to flag unauthorized access or anomalies.
- Escalation Path: A predefined hierarchy ensures that the right security officers are alerted immediately.
- Evidence Collection: Forensic logs must be preserved to determine the scope and impact of the event.
- Notification Protocol: A clear process for informing customers and regulatory bodies within the required legal windows.
This planning requires deep coordination between the AI vendor and all underlying subprocessors. A prepared response can mitigate the financial and reputational damage that follows a data exposure event.
Solid breach planning proves to investors that the platform is managed with professional maturity. It transforms a potential crisis into a controlled, manageable operational process.
HIPAA-Compliant AI RCM Platform Architecture
Architecture for an enterprise RCM platform must balance high-performance computing with uncompromising data isolation.
This structural blueprint ensures that AI models can learn from sensitive data without ever risking a compliance breach.
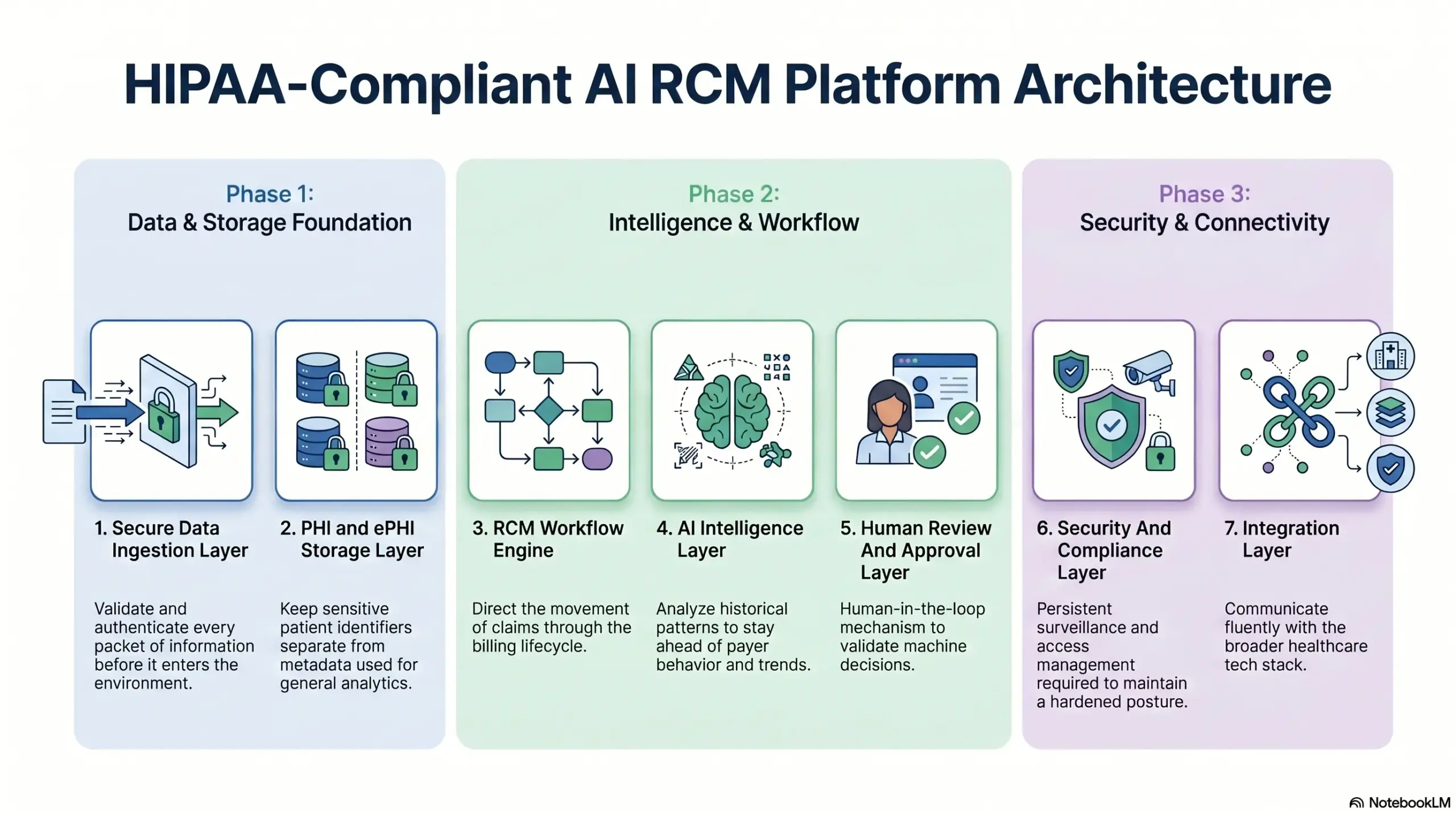
1. Secure Data Ingestion Layer
The ingestion layer acts as the primary gatekeeper for all incoming clinical and financial data points. It must validate and authenticate every packet of information before it enters the secure environment.
- Diverse Data Streams: The system pulls from patient intake, EHR records, and direct payer APIs.
- Authentication: Robust API authentication protocols ensure only verified sources can transmit data.
- Validation: Incoming document uploads and claims data undergo rigorous validation to prevent corruption.
- Encrypted Transport: All data is protected by TLS encryption during the transition from the source to the platform.
2. PHI and ePHI Storage Layer
Storing protected health information requires more than simple encryption; it requires a strategy of compartmentalization. This layer keeps sensitive patient identifiers separate from the metadata used for general analytics.
- Segmented Storage: PHI is stored in isolated databases to limit the “blast radius” of any potential incident.
- Metadata Separation: Non-identifiable data is decoupled from clinical records to facilitate safer AI training.
- Resilience: The architecture includes automated backups and a comprehensive disaster recovery plan.
- Retention Management: Automated policies ensure that data is only kept for as long as legally required.
3. RCM Workflow Engine
The workflow engine is the operational heart of the platform, directing the movement of claims through the billing lifecycle. It automates the transition from a patient encounter to a finalized payment.
- Pre-submission Tasks: The engine handles eligibility verification and prior authorization workflows automatically.
- Queue Management: It routes coding tasks and claim scrubbing results to the appropriate human teams.
- Post-submission Actions: The system manages denial routing, appeal tasks, and payment reconciliation.
- AR Optimization: Automated AR follow-up ensures that no outstanding balance is ignored.
4. AI Intelligence Layer
The AI layer provides the predictive “brain” that differentiates this platform from standard billing software. It analyzes historical patterns to stay ahead of payer behavior and documentation trends.
- Predictive Scoring: The AI assigns a risk score to every claim, flagging potential denials before they are submitted.
- Coding Assistance: Machine learning models suggest the most accurate codes based on clinical documentation.
- Financial Strategy: The layer provides underpayment detection and sophisticated revenue forecasting.
- Actionable Insights: It prioritizes AR tasks and assists in drafting highly effective appeal letters.
5. Human Review And Approval Layer
Despite the power of AI, human oversight remains a mandatory component of a compliant RCM strategy. This layer provides a “human-in-the-loop” mechanism to validate machine decisions.
- Quality Control: Coders and billers review AI-generated suggestions to ensure clinical accuracy.
- Accountability: The system captures override reasons whenever a human user disagrees with an AI recommendation.
- Audit History: A complete approval history is maintained for every claim processed by the system.
- Compliance Check: Dedicated managers can review high-risk cases to ensure adherence to internal policies.
6. Security And Compliance Layer
The security layer provides the persistent surveillance and access management required to maintain a “hardened” posture. It operates silently across all other architectural components.
- Access Management: Multi-factor authentication (MFA) and Role-Based Access Control (RBAC) restrict data access.
- Persistent Monitoring: Audit logs and session controls track every user interaction within the platform.
- Loss Prevention: Data Loss Prevention (DLP) tools prevent sensitive information from leaving the secure perimeter.
- Incident Response: Real-time monitoring triggers alerts for any anomalous activity or potential security breach.
7. Integration Layer
No RCM platform can thrive in isolation; it must communicate fluently with the broader healthcare tech stack. The integration layer provides the bridges to external systems.
- Clinical Hooks: Deep connections to EHR/EMR and Practice Management Systems ensure seamless data flow.
- Financial Channels: Integrations with clearinghouses and payer APIs facilitate high-speed claim transmission.
- Banking Rails: Connections to payment gateways and accounting platforms simplify the reconciliation process.
- Document Management: The system integrates with existing document storage to pull relevant clinical evidence.
Strong integration capabilities reduce manual data entry and eliminate the silos that cause billing delays. It ensures that the AI has a 360-degree view of the patient’s financial and clinical journey.
A well-designed architecture is the only way to scale a healthcare technology business safely. By building on these layers, you create a platform that is both innovative and legally sound.
AI Use Cases In A HIPAA-Compliant RCM Platform
The integration of AI into the revenue cycle fundamentally changes the financial trajectory of a healthcare organization. By applying machine learning to high-volume transactional data, these platforms turn reactive billing into proactive revenue management.
1. AI Denial Prediction
Denial prediction is the primary defense against revenue leakage. By analyzing historical data, the AI identifies patterns that lead to rejections before the claim ever reaches the payer.
- Risk Variables: The model evaluates payer history, specific claim fields, and authorization status in real-time.
- Actionable Insights: Rather than just a score, the AI provides specific reason codes or risk factors for each potential denial.
- Smart Routing: High-risk claims are automatically diverted from the submission queue to a specialist’s worklist for manual intervention.
- Documentation Patterns: It detects inconsistencies between clinical narratives and the submitted claim data that usually trigger audits.
2. AI Claim Scrubbing
Standard claim scrubbers use static rules, but AI-driven scrubbing evolves with the payer. It recognizes shifting requirements and subtle nuances that hard-coded systems often miss.
- Logic Verification: The system checks for incompatible codes and ensures all required modifiers are present.
- Payer-Specific Edits: It identifies unique “edits” or rules specific to individual insurance companies to ensure the claim is “clean.”
- Completeness Checks: The AI ensures that every field required for adjudication is filled with validated, accurate data.
- Rejection Reduction: By catching errors locally, the platform reduces the cycle time wasted on preventable electronic rejections.
This layer of intelligence serves as the final quality control check. It ensures that the submission process is frictionless, leading to faster payment cycles and less administrative rework.
3. AI-Assisted Medical Coding
Medical coding is a complex, high-stakes task where errors lead to both financial loss and compliance risk. AI assists human coders by providing a structured, intelligent starting point.
- Code Suggestions: The AI scans clinical documentation to suggest relevant CPT, ICD-10, and HCPCS codes.
- Discrepancy Detection: It highlights areas where the selected codes do not match the evidence found in the provider’s notes.
- Efficiency Gains: Coders can process higher volumes of encounters by reviewing and validating AI suggestions rather than starting from scratch.
- Compliance Guardrails: Human approval remains mandatory, ensuring that a professional always verifies the AI’s logic for medical necessity.
By streamlining the coding process, the platform reduces the backlog of unbilled encounters. It allows the organization to capture the full complexity of care provided while maintaining a high standard of accuracy.
4. AI Prior Authorization Support
Prior authorization is often the most significant delay in the healthcare revenue cycle. AI automates the discovery and tracking of these requirements to prevent unauthorized services.
- Requirement Detection: The system automatically determines if a specific procedure requires authorization based on the patient’s insurance plan.
- Evidence Mapping: It provides a checklist of the clinical documentation required to support the authorization request.
- Expiration Alerts: The AI tracks active authorizations and alerts teams before they expire to prevent gaps in covered care.
- Status Monitoring: It eliminates manual portal checks by automatically updating the status of pending requests.
Automating these workflows ensures that patient care is not delayed by administrative hurdles. It protects the provider from performing services that will ultimately be denied for lack of authorization.
5. AI Appeal Drafting Support
When denials do occur, the speed and quality of the response determine if the revenue is ever recovered. AI streamlines the appeal process by synthesizing the necessary data into a persuasive argument.
- Reason Summarization: The AI parses the payer’s denial code and explains it in plain language for the billing staff.
- Evidence Retrieval: It automatically pulls relevant clinical notes and previous correspondence to support the appeal.
- Drafting Engine: The system generates a customized appeal letter based on the specific denial reason and payer preferences.
- Success Analytics: It tracks which appeal arguments are most successful with specific payers to refine future strategies.
This support reduces the time spent on administrative drafting by over 50%. It ensures that every appeal is professional, evidence-backed, and optimized for success.
6. AI Payment Variance And Underpayment Detection
Payers do not always reimburse according to their own contracts. AI provides a systematic way to identify and recover these “silent” revenue losses.
- Contract Comparison: The system compares actual reimbursement amounts against the expected rates defined in payer contracts.
- Variance Flagging: It automatically identifies accounts where the payment differs from the expected amount by a specific threshold.
- Mismatch Detection: The AI flags instances where the payer’s internal rules conflict with the agreed-upon contract terms.
- Recovery Prioritization: It highlights the high-value variances where the probability of successful recovery is highest.
Detecting underpayments ensures that the organization receives every dollar it has earned. It provides the data needed to hold payers accountable during contract negotiations.
7. AI AR Prioritization
Not all outstanding accounts are created equal. AI moves away from simple chronological sorting to prioritize the Accounts Receivable (AR) based on the likelihood of collection.
- Predictive Scoring: Each account is scored based on value, age, payer behavior, and current claim status.
- Intelligent Routing: High-priority accounts are routed to senior collectors, while simpler tasks are handled by junior staff or automation.
- Manual Triage Reduction: The system eliminates the need for managers to manually assign worklists every morning.
- Outcome Optimization: By focusing on the most “collectible” debt first, the platform maximizes the cash recovered within each billing cycle.
8. AI Revenue Forecasting
Predicting future cash flow is critical for the stability of any healthcare enterprise. AI uses historical trends and current claim data to provide a clear view of the financial future.
- Cash Flow Projections: The system estimates when payments will arrive based on average payer turnaround times.
- Delay Prediction: It identifies seasonal or payer-specific trends that might cause temporary revenue slowdowns.
- Exposure Estimation: The AI forecasts the total value of potential denials currently sitting in the pipeline.
- Financial Planning: These insights help finance leaders plan for capital expenditures or operational expansions with confidence.
Accurate forecasting removes the guesswork from financial management. It allows healthcare leaders to operate with a proactive mindset rather than reacting to monthly fluctuations.
A platform equipped with these use cases does more than just bill claims; it acts as a strategic financial advisor. By deploying these tools, organizations can ensure long-term viability in an increasingly complex reimbursement landscape.
HIPAA Safeguards To Build Into AI RCM Software
Building a compliant platform requires a layered defense strategy that addresses both digital and physical vulnerabilities.
These safeguards ensure that as the AI processes millions of data points, the underlying infrastructure remains a fortress for patient privacy.
1. Administrative Safeguards
Administrative safeguards form the policy-driven backbone of the organization. They define how staff and systems interact with sensitive data to ensure that compliance is a deliberate, managed process rather than a secondary thought.
- Risk Analysis and Management: The system must undergo regular assessments to identify and mitigate potential security vulnerabilities.
- Workforce Controls: Strict access policies ensure that employees only see the data necessary for their specific job functions.
- Security Training: Continuous education programs keep the team updated on the latest phishing threats and data handling protocols.
- Contingency Planning: Formal procedures must be in place to ensure business continuity and data protection during an emergency.
HHS requires these administrative measures to ensure that the human element of the revenue cycle is as secure as the technical one. By formalizing these workflows, an enterprise can prove its commitment to data integrity during any regulatory audit.
2. Physical Safeguards
Physical safeguards protect the actual hardware and facilities that house sensitive medical data. Even in a cloud-first world, the physical location of servers and the devices used to access them must be strictly controlled.
- Secure Hosting: Data must reside in a facility with restricted physical access, surveillance, and biometric security.
- Workstation Security: Policies must govern the placement and use of screens to prevent unauthorized viewing of PHI in office environments.
- Device Controls: Every laptop or tablet used to access the RCM platform must be encrypted and capable of being wiped remotely.
- Media Handling: Protocols for the disposal and movement of hardware ensure that no data remains on old drives or backup tapes.
Controlling the physical perimeter prevents “low-tech” breaches that can be just as devastating as a cyberattack.
3. Technical Safeguards
Technical safeguards are the software-based controls that protect the data as it moves through the AI RCM platform. These tools provide the granular visibility and protection needed to manage a modern, distributed workforce.
- Identity Management: Each user must have a unique ID paired with Multi-Factor Authentication (MFA) for every login.
- Access and Integrity: Role-Based Access Control (RBAC) limits visibility, while integrity controls ensure data is not altered without authorization.
- Encryption Standards: All data must be encrypted using AES-256 at rest and TLS 1.2 or higher during transmission.
- Audit and Logoffs: Automatic logoffs prevent sessions from being hijacked, while audit controls record every single data interaction.
These technical barriers are the primary defense against external hackers and internal misuse.
4. AI-Specific Safeguards
Integrating AI introduces unique risks that traditional HIPAA frameworks may not fully cover. Builders must implement specific guardrails to ensure that LLMs and machine learning models do not inadvertently expose or leak PHI.
- Prompt Governance: The system must prevent the inclusion of PHI in unmanaged or public AI prompts.
- Model Training Ethics: PHI should never be used to train underlying models unless explicitly permitted by a contract or through rigorous de-identification.
- AI Audit Trails: Every recommendation made by the AI, and the data used to reach that conclusion, must be recorded for compliance review.
- Human Gatekeeping: AI outputs must be validated by a professional before they lead to clinical or financial actions.
Building these safeguards into the architecture from day one is a requirement for enterprise-grade software. It provides the legal and technical assurance that high-net-worth investors and healthcare partners demand.
Data Protection Features Of An AI RCM Platform
A robust data protection strategy is what separates a prototype from a market-ready enterprise solution.
These features ensure that patient data remains a locked asset, accessible only to authorized entities and resilient against external threats.
1. Encryption At Rest And In Transit
Encryption acts as the final line of defense, rendering data useless to unauthorized parties. An enterprise RCM platform must secure information, whether it is sitting in a database or moving across a network.
- Storage Security: All databases and physical files containing PHI are protected with AES-256 encryption.
- Communication Security: API traffic and data transfers use high-level TLS protocols to prevent “man-in-the-middle” attacks.
- Backup Integrity: Off-site backups are encrypted before they leave the primary environment to ensure total lifecycle security.
- Key Management: Robust internal protocols manage encryption keys, ensuring they are rotated regularly and never stored with the data they protect.
By implementing comprehensive encryption, the platform meets the highest technical standards of HIPAA.
2. Role-Based Access Control
In a large healthcare organization, not every user needs to see every data point. Role-Based Access Control (RBAC) ensures that staff members only interact with the information required for their specific professional tasks.
| User Role | Access Level | Primary Responsibility |
| Coders | Clinical notes and codes | Assigning and validating medical codes |
| Billers | Claims and insurance data | Submission and payment tracking |
| Denial Managers | Denial codes and appeals | Recovering lost revenue and analyzing trends |
| Finance Leaders | High-level analytics | Forecasting and strategic planning |
| Compliance Admins | Audit logs and system settings | Maintaining regulatory oversight |
Limiting access through RBAC significantly reduces the risk of internal data misuse. It creates a structured environment where responsibilities are clear and sensitive data exposure is kept to an absolute minimum.
3. Multi-Factor Authentication
Passwords alone are insufficient for modern security. This is because Multi-Factor Authentication (MFA) adds a critical second layer of verification. This is especially vital for administrative accounts and remote users accessing the platform from outside the hospital network.
- Privileged Access: Every administrator and super-admin must use MFA to prevent account takeover.
- Remote Work: Staff logging in from home or off-site locations are required to verify their identity via a secondary device.
- Workflow Verification: High-stakes actions, such as approving large payment overrides, can be gated behind a second authentication factor.
- Security Resilience: MFA effectively neutralizes the threat of stolen credentials, which is a leading cause of healthcare data breaches.
Implementing MFA across the platform signals to enterprise clients that your security posture is proactive. It protects the organization’s most sensitive workflows from unauthorized interference.
4. Audit Logs And Activity Monitoring
Transparency is a core requirement of HIPAA compliance. Every action taken within the platform, whether by a human user or an AI agent, must be recorded in a tamper-proof audit log.
- User Tracking: The system logs every data access, claim edit, and report export with a user ID and timestamp.
- AI Accountability: All AI recommendations and the subsequent human approvals or rejections are tracked for quality control.
- Security Alerts: Failed login attempts and unusual data patterns trigger immediate alerts for the security team.
- Compliance Readiness: These logs serve as the primary evidence during a regulatory audit or internal investigation.
5. Data Segmentation And Tenant Isolation
For SaaS providers hosting multiple healthcare clients, data segmentation is a non-negotiable architectural requirement. Tenant isolation ensures that Client A can never accidentally access or view the data of Client B.
- Virtual Isolation: Each client operates in a logically separate environment, even within a shared cloud infrastructure.
- Schema Separation: Databases are partitioned to prevent cross-tenant data leakage during complex queries.
- Departmental Silos: Within a single organization, access can be further segmented by facility or department to match internal policies.
- Secure Testing: Development and staging environments are kept entirely separate from live production data.
Effective segmentation protects the platform from cascading failures.
6. De-Identification And Tokenization
To train AI models or perform large-scale analytics safely, the platform must be able to remove patient-identifying details. De-identification allows the AI to learn from patterns without ever “seeing” a specific person’s name or social security number.
- Analytics Workflows: High-level reports use aggregated, de-identified data to protect individual privacy.
- Model Training: Machine learning models are trained on tokenized datasets where sensitive identifiers have been replaced by random strings.
- Reduced Exposure: Minimizing the use of raw PHI during development reduces the overall risk profile of the platform.
- Safe Collaboration: De-identified data can be shared with researchers or third-party analysts without violating HIPAA rules.
By prioritizing de-identification, the platform achieves a balance between innovation and privacy.
7. Backup And Disaster Recovery
Healthcare revenue cycles cannot afford downtime. A robust backup and disaster recovery (DR) plan ensures that financial operations can continue even in the event of a major system failure or cyberattack.
- Reliable Backups: Encrypted backups are performed daily and stored in geographically diverse locations.
- Recovery Metrics: The platform is built to meet strict Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO).
- Failover Planning: Automated failover mechanisms switch operations to a secondary environment if the primary site goes offline.
- Business Continuity: Regular DR drills ensure that the team is prepared to restore services quickly and accurately.
Investing in resilience protects the organization from catastrophic financial loss. It guarantees that the AI RCM platform remains a reliable engine for the enterprise, regardless of external circumstances.
Building these data protection features creates a foundation of trust. For entrepreneurs, this technical excellence is the key to unlocking long-term partnerships with major healthcare systems.
Building A HIPAA-Compliant AI RCM Platform Process
Constructing an enterprise-grade financial engine requires a methodical approach that prioritizes security at every milestone.
At Intellivon, we follow a rigorous lifecycle that moves from deep discovery to secure deployment, ensuring your investment is both scalable and compliant.
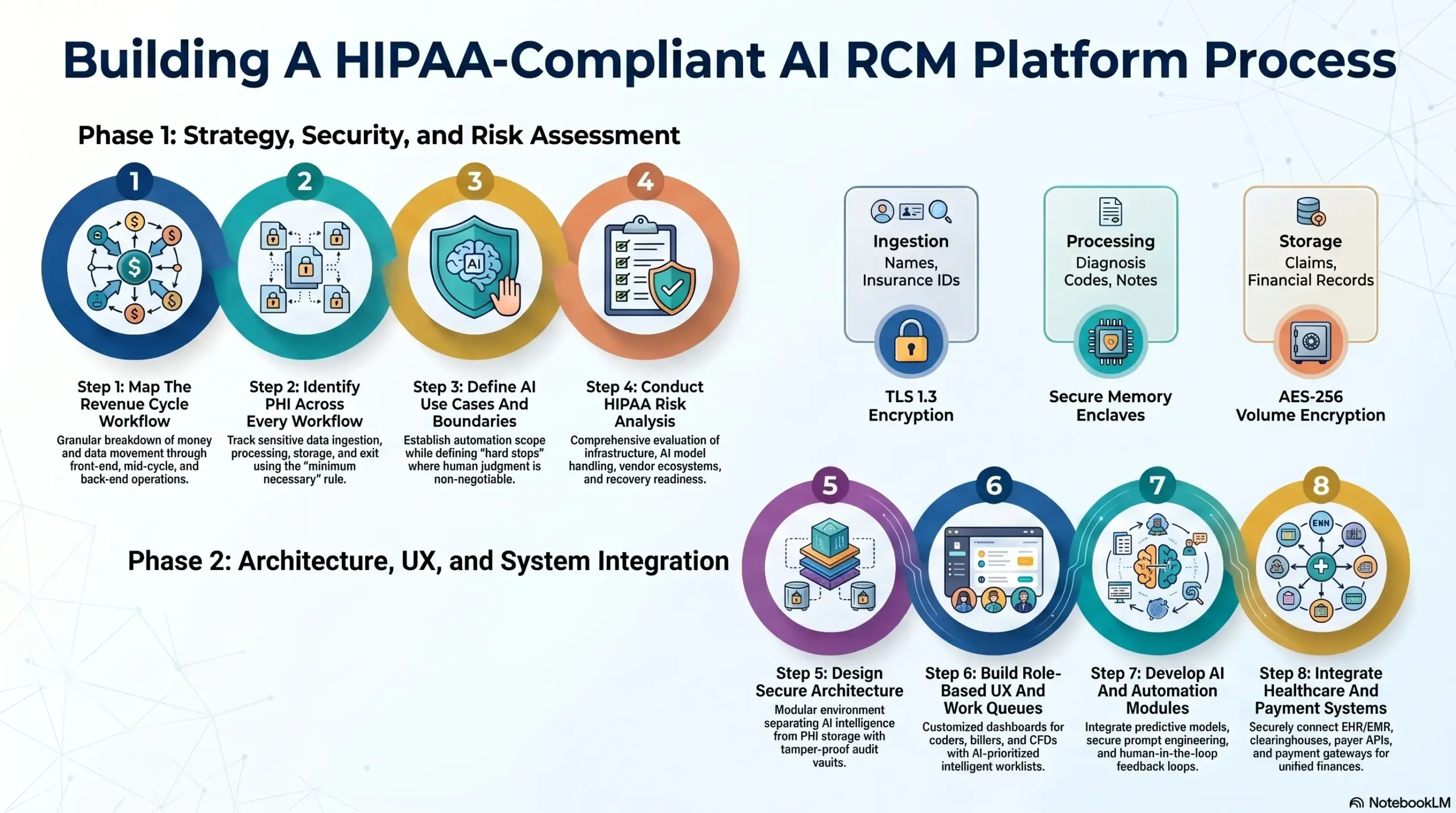
Step 1: Map The Revenue Cycle Workflow
The first phase involves a granular breakdown of how money and data move through the organization. We identify every touchpoint where a claim could stall or a documentation gap could occur.
- Front-End Operations: Mapping patient access, real-time eligibility, and prior authorization triggers.
- Mid-Cycle Processes: Analyzing the transition from clinical encounter to medical coding and claim scrubbing.
- Back-End Management: Documenting denial routing, payment posting, and intensive AR follow-up.
- Financial Oversight: Establishing the requirements for executive reporting and secondary collections.
By mapping the entire lifecycle, we eliminate operational silos. This ensures the AI has a clear “map” to follow, preventing data from falling through the cracks between departments.
Step 2: Identify PHI Across Every Workflow
Security is only as strong as its weakest link, so we perform a “census” of all Protected Health Information. We track exactly how sensitive data enters, sits within, and exits the platform.
| Data Stage | PHI Components | Security Measure |
| Ingestion | Names, Insurance IDs, Visit Reason | TLS 1.3 Transport Encryption |
| Processing | Diagnosis Codes, Provider Notes | Secure Memory Enclaves |
| Storage | Claims, EOBs, Financial Records | AES-256 Volume Encryption |
| Exit | Payer Submissions, Patient Statements | Secure EDI & Tokenized Links |
We identify which users and specific AI modules require access to these data points. This allows us to enforce the “minimum necessary” rule, ensuring no entity sees more than required for their task.
Step 3: Define AI Use Cases And Boundaries
Innovation must be balanced with practical boundaries to maintain auditability. We define the specific roles the AI will play while establishing “hard stops” where human judgment is non-negotiable.
- Automation Scope: Defining modules for denial prediction, coding support, and payment variance detection.
- Intelligence Boundaries: Ensuring the AI assists in appeal drafting but does not “click send” without a manager’s review.
- Risk Scoring: Implementing claim-level risk assessments to flag high-value or high-complexity cases for senior staff.
- Pre-authorization: Automating the rules engine to check payer requirements before service is rendered.
Setting these boundaries ensures the platform remains a tool for experts rather than a black box.
Step 4: Conduct HIPAA Risk Analysis
Before a single line of code is written for production, we conduct a comprehensive HIPAA Risk Analysis. This identifies potential vulnerabilities in the technology, the people, and the vendors involved.
- Infrastructure Risks: Evaluating cloud hosting security and data center compliance certifications.
- Processing Risks: Analyzing how AI models handle PHI during inference and training phases.
- Vendor Ecosystem: Reviewing the security posture of third-party APIs for payments or clearinghouses.
- Recovery Readiness: Stress-testing backup systems and disaster recovery protocols to ensure business continuity.
This proactive analysis is a core regulatory requirement. It provides the documentation necessary to prove that the platform was built with “security by design” from the very beginning.
Step 5: Design Secure Architecture
Our architectural philosophy at Intellivon centers on isolation and resilience. We build a modular environment where the AI intelligence layer is separated from raw PHI storage.
- Secure Ingestion: A hardened gateway that validates and authenticates all incoming healthcare data.
- Workflow Engine: A central orchestrator that moves claims through work queues based on real-time AI insights.
- Audit Vault: A tamper-proof logging system that records every user and system action for seven years.
- Persistent Monitoring: Real-time threat detection that flags anomalous data access or failed login attempts.
This structure allows for high-speed processing without compromising the secure perimeter. It ensures that the platform can scale to handle millions of transactions while remaining highly responsive.
Step 6: Build Role-Based UX And Work Queues
A platform is only effective if it is usable. We design custom dashboards tailored to the specific needs of each professional role within the revenue cycle.
- Operational Views: Specialized dashboards for coders, billers, and denial managers to focus on their specific tasks.
- Compliance Portals: Dedicated views for admins to monitor audit logs, session controls, and BAA statuses.
- CFO Command Center: High-level visualization of revenue forecasting, days in AR, and net collection rates.
- Intelligent Queues: Worklists that are automatically prioritized by the AI based on recovery likelihood and claim value.
Role-based design ensures that sensitive data is only visible to those who need it.
Step 7: Develop AI And Automation Modules
At this stage, we integrate the predictive models that drive the platform’s ROI. We use a combination of proprietary rules engines and advanced machine learning to optimize the billing cycle.
- Model Selection: Choosing the right architecture for specific tasks, such as NLP for coding and regression for forecasting.
- Prompt Engineering: Developing secure prompt structures that prevent PHI leakage while maximizing AI accuracy.
- Risk Scoring Engine: Calibrating models to identify “denial-prone” claims based on billions of historical data points.
- Feedback Loops: Implementing “human-in-the-loop” workflows where staff corrections directly retrain the AI.
These modules are the “brain” of the system.
Step 8: Integrate Healthcare And Payment Systems
The final step is connecting the platform to the broader healthcare ecosystem. This is where Intellivon excels, building the bridges that allow for seamless, secure data exchange.
| Integration Type | Purpose | Key Benefit |
| EHR/EMR | Clinical Data Pull | Eliminates manual data entry errors |
| Clearinghouse | EDI 837/835 Exchange | Faster claim submission and remittance |
| Payer APIs | Real-time Status & Auth | Ends the reliance on manual payer portals |
| Payment Gateway | Secure Collections | Accelerates patient-side revenue capture |
By integrating these systems, we create a unified platform that acts as a single source of truth for the organization’s finances. This connectivity is what transforms a simple tool into a comprehensive enterprise solution.
Our process ensures that every phase of development is documented, secure, and aligned with your business goals. By following this roadmap, Intellivon delivers a platform that is not just compliant but a true driver of organizational growth.
Conclusion
Building a HIPAA-compliant AI RCM platform is a strategic necessity for modern healthcare enterprises. By balancing advanced automation with rigorous security and human oversight, leaders can recover lost revenue while safeguarding patient trust.
The transition from reactive billing to predictive financial orchestration is no longer optional. Investing in a secure, intelligent infrastructure ensures long-term operational resilience and financial stability in an increasingly complex and regulated healthcare landscape.
Build A HIPAA-Compliant AI RCM Platform With Intellivon
At Intellivon, we build AI-powered RCM platforms for healthcare SaaS companies, RCM vendors, billing companies, specialty clinics, hospitals, and enterprise healthcare teams.
Our engineering approach connects secure data pipelines, HIPAA-aligned architecture, AI-assisted claims workflows, denial prediction, coding support, payer integrations, payment intelligence, compliance controls, and executive revenue dashboards into one connected platform.
This helps your team protect sensitive healthcare data, automate revenue cycle workflows, reduce avoidable denials, improve claim accuracy, and monitor financial performance with greater confidence.
A. Build Secure PHI Data Pipelines
AI RCM platforms depend on sensitive patient, claims, clinical, billing, and payer data. We design secure PHI data pipelines that support AI workflows without weakening privacy, compliance, or operational control.
We help with:
- Data ingestion
- PHI storage
- Encryption
- Access control
- Data validation
- Audit logging
- Backup planning
B. Integrate With Healthcare And Revenue Systems
A HIPAA-compliant AI RCM platform must work inside your existing healthcare ecosystem. We connect your platform with the systems that manage patient records, claims, payments, documents, payer responses, and revenue reporting.
We integrate with:
- EHR/EMR systems
- Practice management systems
- Clearinghouses
- Payer APIs
- Payment gateways
- Document systems
- Analytics tools
C. Make AI Explainable, Governed, And Reviewable
AI in revenue cycle management cannot operate like a black box. We build AI workflows with human review, clear reasoning, confidence scores, audit trails, override tracking, and compliance visibility.
We focus on:
- Human approval
- Confidence scores
- Explanation layers
- AI audit trails
- Model monitoring
- Override tracking
- Compliance dashboards
D. Build For Scale And Long-Term Compliance
HIPAA-compliant AI RCM platforms need to support more users, more claims, more integrations, and more compliance evidence as the business grows. We design systems that stay secure, scalable, and easier to maintain over time.
We build with:
- Role-based access
- Multi-tenant architecture
- Secure APIs
- Monitoring
- Disaster recovery
- Compliance evidence
- Ongoing optimization
If you are planning to build a HIPAA-compliant AI RCM platform, Intellivon can help you define the right scope, design secure architecture, integrate healthcare systems, and develop AI workflows that support real revenue outcomes. Contact Intellivon to discuss your HIPAA-compliant AI RCM platform roadmap.
Things To Know About HIPAA-Compliant AI RCM Platforms
Q1. What is a HIPAA-compliant AI RCM platform?
A1. A HIPAA-compliant AI RCM platform uses artificial intelligence to improve billing, coding, claim validation, denial prediction, payment tracking, and revenue analytics while protecting patient data. It must include secure PHI handling, access controls, audit logs, encryption, compliance workflows, and human review for AI-assisted decisions.
Q2. How do you make an AI RCM platform HIPAA-compliant?
A2. To make an AI RCM platform HIPAA-compliant, teams must protect PHI across data storage, model workflows, integrations, user access, logs, and third-party vendors. This includes encryption, role-based access, audit trails, secure APIs, BAA-ready vendors, minimum necessary data use, and ongoing compliance monitoring. HIPAA touches the full RCM lifecycle from registration to collections.
Q3. Can AI be used safely in healthcare revenue cycle management?
A3. Yes, AI can be used safely in RCM when it is designed with privacy, explainability, and human oversight. AI can support eligibility checks, claim scrubbing, coding review, denial prediction, appeal drafting, compliance auditing, and revenue forecasting. However, teams should avoid black-box automation for sensitive billing and PHI-heavy workflows.
Q4. How much does it cost to build a HIPAA-compliant AI RCM platform?
A4. A HIPAA-compliant AI RCM platform can cost between $50,000 and $150,000+, depending on AI modules, compliance depth, integrations, data infrastructure, security controls, and deployment scale. Denial prediction, coding intelligence, appeal automation, payer analytics, and EHR integrations usually increase the total development cost.






