Key Takeaways:
-
HIPAA compliance directly affects hospital procurement approval, security reviews, and contract conversion before deals close.
-
PHI lives across DICOM metadata, pixel data, AI outputs, logs, annotations, and support tools, not just primary databases.
-
Access control, BAAs, de-identification, and audit trails must be built into the architecture, not added after deployment.
-
Common failures include treating DICOM metadata as non-sensitive and signing BAAs without monitoring vendor security.
-
How Intellivon builds HIPAA-compliant AI imaging platforms your enterprise fully owns, with secure pipelines and audit workflows from day one.
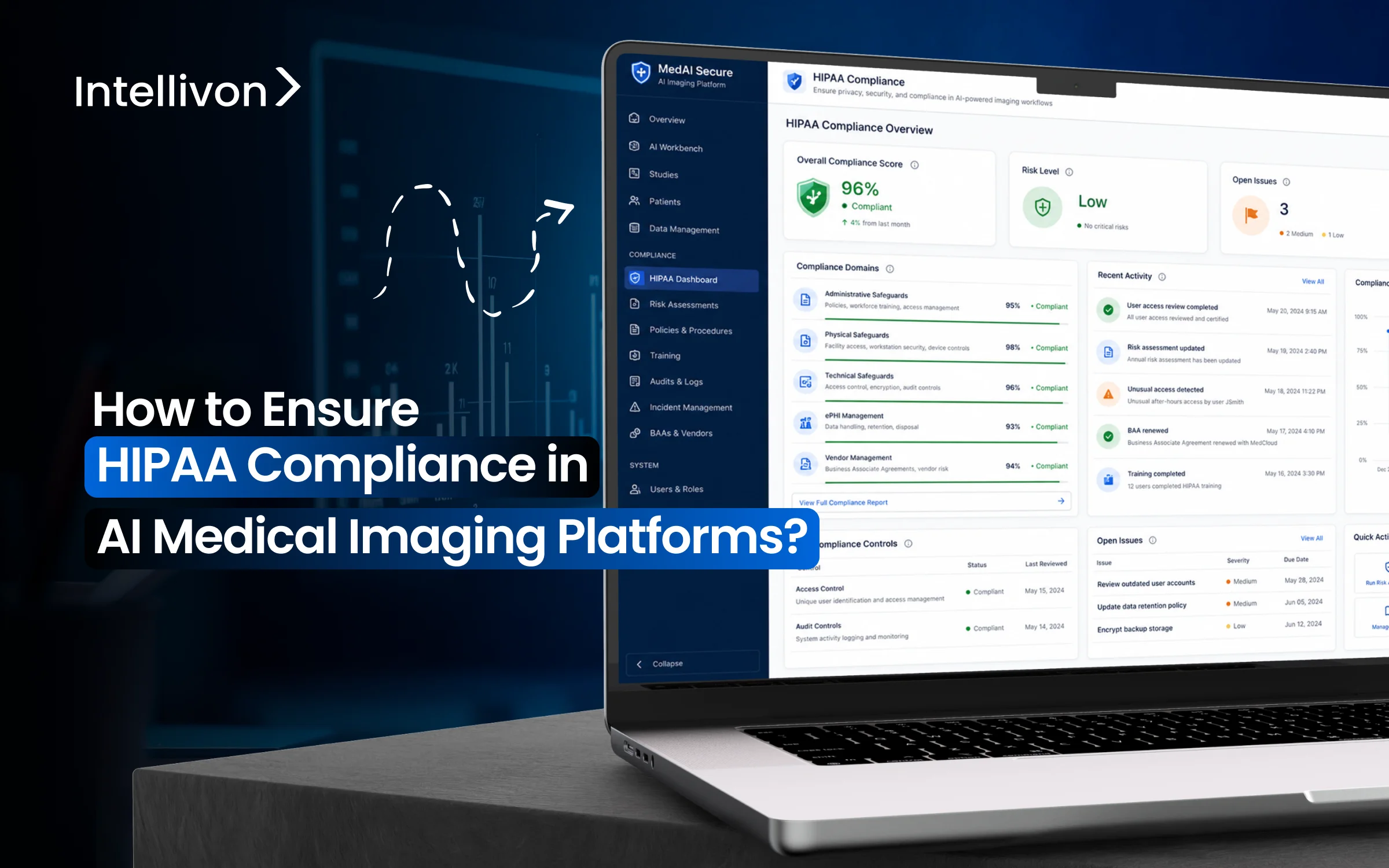
Healthcare platforms that scale within hospital systems treat compliance as a design decision, and not an afterthought. AI medical imaging platforms manage sensitive patient data at every level, including DICOM files, radiology reports, AI outputs, annotations, PACS/RIS workflows, cloud infrastructure, audit logs, and training datasets. At the same time, every touchpoint contains protected health information, which is subject to HIPAA regulations.
For healthcare technology companies, HIPAA compliance affects whether hospital procurement teams will approve the platform, whether security reviews proceed, whether pilot programs turn into contracts, and whether your design gains clinical trust. A single gap in the PHI workflow can delay a significant enterprise deal.
The platforms that succeed within health systems are those that integrate compliance from the start. This is because HIPAA influences how PHI is collected, transmitted, stored, de-identified, accessed, audited, and used in AI workflows. At Intellivon, we design imaging AI systems with compliance as a core element. This blog explains what that requires and why it’s important before you start building or investing.
Why HIPAA Compliance Matters In AI Medical Imaging
Medical images are not just clinical files. DICOM headers and pixel data carry rich protected health information, making every AI workflow a potential privacy exposure point.
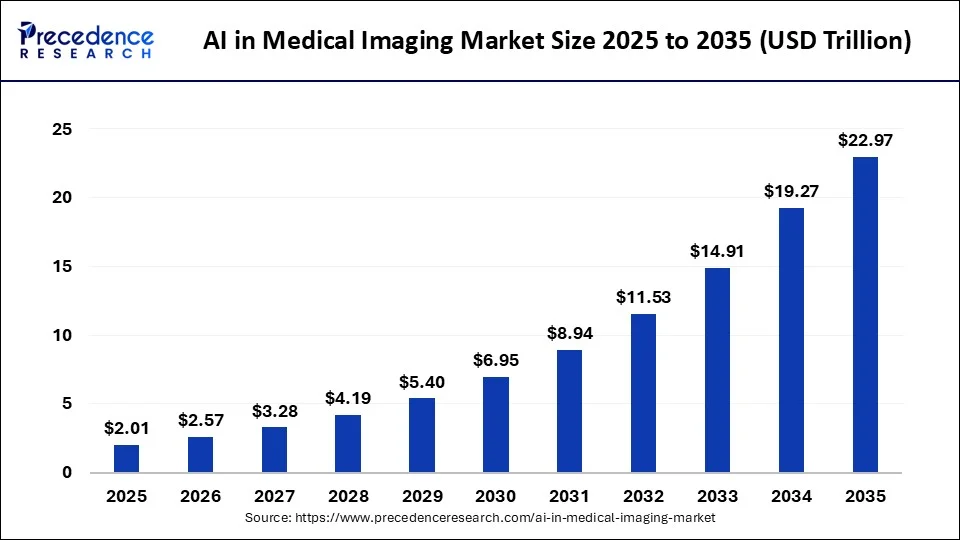
The market context makes this more urgent. AI medical imaging is growing at a CAGR of 23% to 35%, depending on the segment and source. That growth is accelerating vendor activity, hospital adoption, and data volume simultaneously.
However, scale without compliance creates institutional risk. Health systems are not simply buying software anymore. They are evaluating data pipelines, vendor security postures, and deployment architectures before a contract is signed.
Therefore, HIPAA compliance in AI medical imaging is not a checkbox. It directly affects how platforms are built, how vendors are selected, and how far a deployment can scale inside a hospital environment.
1. Hospitals May Reject Platforms That Fail HIPAA Review
Enterprise healthcare buyers utilize a stringent vetting process before they integrate any new technology. Their IT and legal departments conduct deep dives into your security posture to ensure they are not introducing new liabilities. You must be prepared to provide extensive documentation that proves your readiness.
- Access Controls: Prove that only authorized personnel can view specific patient records.
- Audit Trails: Maintain a permanent log of every person who accessed or modified an image.
- Business Associate Agreements: Sign a BAA to legally commit to protecting the data you process.
- Risk Documentation: Show a proactive approach through regular security assessments and vulnerability scans.
2. PHI Can Leak Through Imaging Workflows
Patient Health Information (PHI) is often hidden in layers that developers might overlook. Beyond the obvious name on a file, data resides in metadata and even within the visual pixels themselves. Failure to scrub these areas can lead to accidental exposure during model training or clinical use.
- DICOM Metadata: Hidden tags in image files often contain birth dates and social security numbers.
- Burned-in Text: Many scanners overlay patient names directly onto the medical image.
- Administrative Logs: System exports and support tickets might accidentally capture sensitive identifiers.
- Storage Backups: Insecure cloud backups can become easy targets for unauthorized data harvesting.
3. Weak Controls Can Delay Product Launches
Poor planning regarding data flows can stall your go-to-market strategy for months. Hospital IT reviews are notoriously slow, and any ambiguity in your security documentation will trigger a cycle of follow-up questions. Therefore, having a clear roadmap for data movement is essential for hitting your launch milestones.
Confusion often arises from unclear vendor gaps or weak access policies. When you rely on third-party cloud providers, you must ensure their configurations align with your specific compliance needs. Streamlining these internal policies early prevents the bottleneck of a failed institutional review later.
4. Breach Risk Can Damage Enterprise Trust
A single data breach can end a promising startup before it gains real traction. Insecure APIs or cloud misconfigurations often serve as the primary entry points for malicious actors. If imaging data is exposed, the resulting legal fees and loss of reputation are frequently impossible to recover from.
Robust monitoring and incident response planning are the only ways to mitigate these risks. You need a strategy that detects anomalies in real time and contains them before they escalate. Consistent investment in security infrastructure ensures that your partners feel confident in the safety of their patient data.
Establishing a compliant environment protects your capital and your reputation simultaneously. This foundation allows you to scale confidently across multiple health systems without the fear of regulatory setbacks.
What HIPAA Covers In AI Medical Imaging Platforms
The scope of federal protection applies to any information that can link a medical image to a specific individual. This includes the technical infrastructure used to process images and the organizational policies governing human access.
Ensuring every component of the AI lifecycle remains within these boundaries is critical for the legality of a commercial healthcare product.
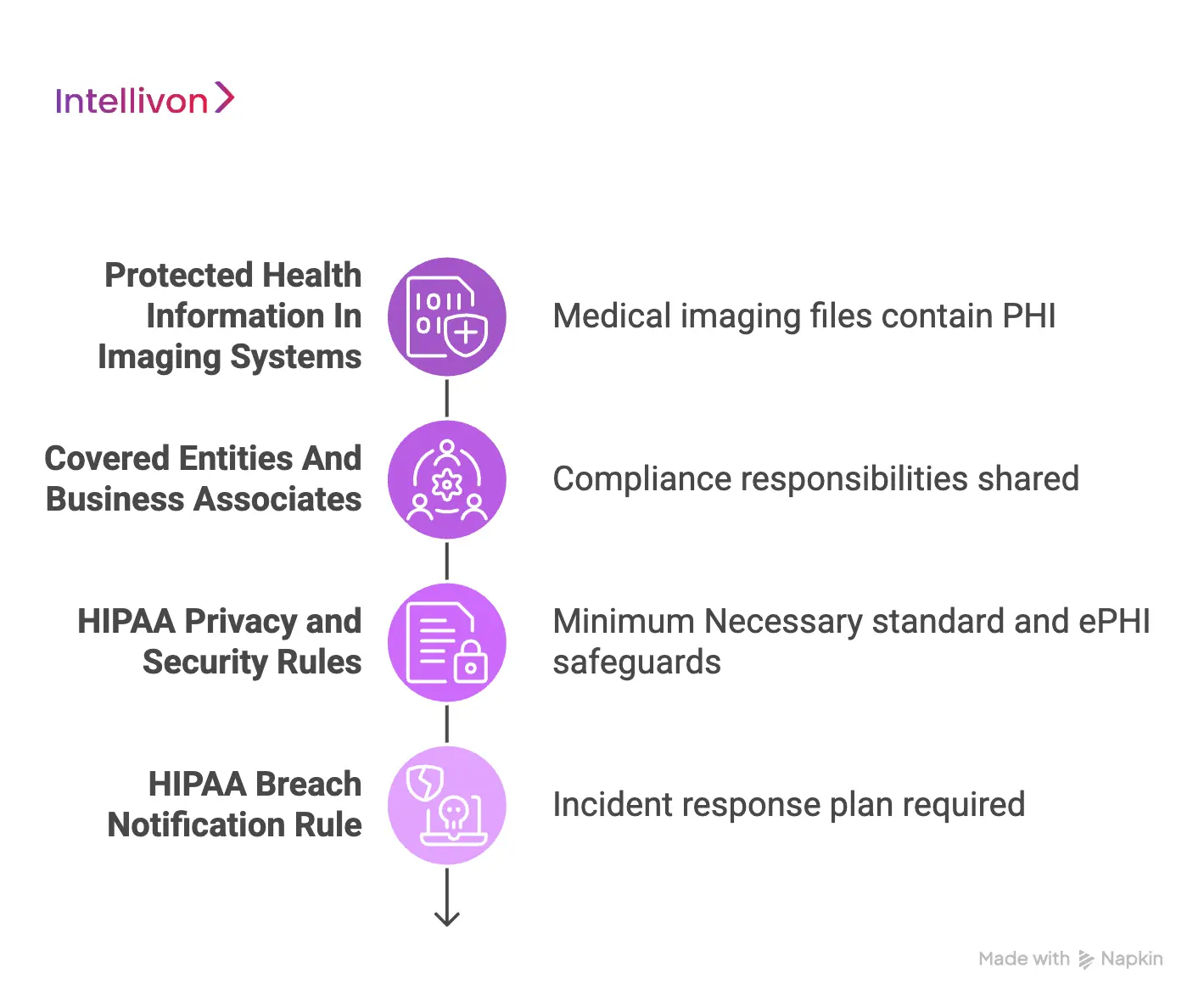
1. Protected Health Information In Imaging Systems
Medical imaging files are dense with identifiers that qualify as Protected Health Information (PHI). Beyond demographic data, clinical context and technical tags also fall under regulatory scrutiny.
- Direct Identifiers: Patient names and social security numbers embedded in files.
- Study Details: Accession numbers that can be cross-referenced with hospital databases.
- Visual Data: Image overlays and burned-in text displaying patient details on the scan.
- Metadata: Hidden tags within the DICOM header containing sensitive dates.
2. Covered Entities And Business Associates
Compliance responsibilities are shared across an ecosystem of providers. While a hospital is a covered entity, any AI vendor or cloud provider handling data is a Business Associate.
This necessitates formal Business Associate Agreements (BAAs) to ensure security standards remain consistent across the supply chain, including labeling services and analytics tools.
3. HIPAA Privacy and Security Rules
The Privacy Rule establishes the “Minimum Necessary” standard, dictating that only specific data required for a task should be accessible. Meanwhile, the Security Rule mandates technical safeguards for electronic PHI (ePHI).
This includes AES-256 encryption for data at rest and TLS 1.2 for data in transit, ensuring confidentiality, integrity, and availability.
4. HIPAA Breach Notification Rule
Preparedness for security incidents is mandatory. This rule requires a defined workflow for detecting, investigating, and reporting unauthorized access. An effective incident response plan includes pre-defined containment steps and rigorous documentation to prove due diligence and minimize reputational damage.
Navigating these regulatory layers is essential for transforming a technical concept into a market-ready clinical asset. Establishing this framework ensures that innovation remains protected and legally sound as it scales.
HIPAA Compliance Requirements At A Glance
HIPAA compliance for AI medical imaging platforms includes privacy controls, security safeguards, risk analysis, access control, encryption, audit logs, BAAs, de-identification, and incident response.
| HIPAA Area | What It Means | How It Affects AI Medical Imaging Platforms |
| Privacy Rule | Controls how PHI is used and disclosed | Defines how imaging data can be accessed, shared, reused, or disclosed |
| Security Rule | Protects ePHI through safeguards | Requires administrative, physical, and technical controls across imaging workflows |
| Risk Analysis | Identifies threats to ePHI | Maps PHI exposure across DICOM flows, AI inference, storage, logs, vendors, and APIs |
| Access Control | Limits who can access PHI | Controls radiologist, technologist, engineer, annotator, support, and admin permissions |
| Minimum Necessary Access | Limits PHI use to what each role needs | Prevents teams from over-accessing imaging data during care, support, annotation, or AI development |
| Audit Controls | Tracks access and user activity | Logs image access, AI output review, export events, admin changes, and service activity |
| Transmission Security | Protects PHI in transit | Secures DICOM, DICOMweb, API calls, cloud transfers, and hospital integrations |
| BAAs | Governs vendors handling PHI | Applies to cloud providers, AI vendors, labeling teams, analytics tools, and support partners |
| De-Identification | Reduces re-identification risk | Protects training, testing, validation, and annotation datasets |
| Integrity And Availability | Keeps ePHI accurate and accessible | Protects imaging records from corruption, loss, mismatching, downtime, and failed recovery |
| Incident Response | Manages suspected data breaches | Defines detection, containment, investigation, notification, recovery, and evidence collection |
| Documentation | Proves HIPAA readiness | Includes policies, data flow maps, access matrices, risk assessments, training records, and vendor files |
Conduct A HIPAA Risk Analysis For AI Imaging Platforms
A formal risk analysis serves as the essential blueprint for aligning an AI infrastructure with federal expectations. It involves a systematic review of how electronic Protected Health Information moves through the system from initial ingestion to final diagnostic output.
By documenting potential threats and their business impact, an organization can prioritize security investments where they are most needed.
1. Map Every ePHI Location Across The Platform
Identifying where data resides is a complex task in distributed AI environments. It is not sufficient to secure the primary database because every touchpoint must be accounted for. This mapping process creates a transparent inventory that simplifies future audits and security updates.
- Data in Transit: APIs and network protocols used to move DICOM files between hospitals and the cloud.
- Data at Rest: Primary cloud storage, long-term archives, and secondary backups.
- AI Lifecycle: Datasets used for model training and the resulting AI-generated annotations.
- Administrative Trace: System logs and support tickets that might inadvertently contain patient identifiers.
2. Identify Threats Across Imaging And AI Workflows
Threat modeling must go beyond traditional hacking risks to include nuances specific to machine learning. Vulnerabilities often emerge at the intersection of third-party integrations and internal processing pipelines. For instance, insecure APIs or improperly configured cloud permissions can lead to wide-scale exposure if not strictly governed.
Furthermore, inference leakage represents a modern risk where sensitive data might be reconstructed from model outputs. Weak authentication for remote developers also presents a significant entry point for unauthorized access.
Addressing these gaps early ensures that the workflow remains resilient against both external attacks and internal errors.
3. Rate The Likelihood And Impact Of Each Risk
Not all risks carry the same weight for a growing enterprise. This phase of the analysis assigns a value to the probability of a breach versus the severity of the fallout. High-impact risks like exposed imaging data or total system downtime receive immediate priority for mitigation efforts.
Factors such as vendor reliability and user role permissions are evaluated here. If a labeling vendor lacks robust internal controls, the likelihood of a leak increases. Conversely, the clinical workflow dependency must be measured to understand how a security shutdown would affect patient care and provider trust.
4. Build A Risk Management Plan From The Findings
The final step involves transforming the assessment into a living document of actionable safeguards. This plan identifies specific remediation steps and assigns ownership to internal teams for execution. It creates a clear timeline for closing security gaps while providing the necessary documentation for hospital IT reviews.
Executive approval of this plan ensures that compliance is viewed as a strategic priority rather than just a technical hurdle. Regular review cycles are established to adapt to new cybersecurity threats. This structured approach builds a defensible position that satisfies both regulators and institutional partners.
Completing this analysis provides the clarity needed to build a secure and scalable medical imaging platform. It transforms abstract regulatory requirements into a concrete roadmap for sustainable enterprise growth.
Where PHI Lives Inside AI Medical Imaging Workflows
Mapping the movement of sensitive data is a technical necessity for any enterprise looking to maintain a compliant architecture. PHI is rarely confined to a single database field because data is often replicated across training sets, temporary caches, and diagnostic outputs.
Identifying these hidden reservoirs is the only way to ensure that de-identification processes remain comprehensive and effective.
1. PHI In DICOM Files And Metadata
The DICOM standard is the backbone of medical imaging, but it represents a significant source of privacy risk. Each file contains a header with dozens of tags that store highly specific patient identifiers.
- Demographic Tags: Patient names, dates of birth, and gender are common identifiers.
- Unique Identifiers: Accession numbers and study instance UIDs that link back to hospital records.
- Institutional Data: Hospital names and modality locations that reveal where care was received.
2. PHI In Image Pixels And Burned-In Text
A significant challenge involves identifiers within the actual pixel data of a scan. Many older modalities overlay patient names and timestamps directly onto the visual output.
- Scrubbing Limits: These details are invisible to metadata scrubbers and require computer vision for redaction.
- Contextual Risks: Hospital logos or scanner serial numbers can allow for patient re-identification.
3. PHI In Reports, Annotations, And Labels
As data moves into the AI pipeline, it becomes associated with new forms of sensitive text. Radiology reports and clinical notes used for ground truth often contain detailed patient narratives.
- Labeling Sets: Annotations like bounding boxes can be linked to specific patient IDs.
- Reviewer Comments: Notes from radiologists during labeling often include identifying clinical details.
4. PHI In AI Outputs And Inference Records
The results generated by an artificial intelligence model can also constitute protected health information. If an AI identifies a specific finding and links it to a record, that output becomes part of the protected history.
- Prediction Logs: Confidence scores and triage labels provide a trail of a diagnostic journey.
- Access Management: Encrypting these records prevents unauthorized personnel from gaining health insights.
5. PHI In Logs, Exports, Caches, And Support Tools
The peripheral systems that support an AI platform are often the most overlooked areas for data leakage. System logs might capture snippets of raw data during a crash or performance bottleneck.
- Temporary Storage: Caches used for image loading can leave sensitive files on local workstations.
- Support Workflows: Screenshots or file downloads often bypass standard security protocols during troubleshooting.
Understanding the integration of patient data within these workflows allows for the implementation of surgical security controls. This technical oversight builds the institutional confidence required to deploy AI solutions in high-stakes clinical environments.
How To Secure DICOM Pipelines And Imaging Data Flows
Establishing a secure architecture for medical imaging requires a holistic view of how data travels between clinical environments and cloud infrastructures. Every transfer point represents a potential vulnerability where encryption or authentication could fail.
Therefore, a robust security strategy must focus on hardening these pipelines to ensure that patient data remains protected from ingestion through to final diagnostic inference.
1. Map Every Imaging Data Flow Before Development
Visualizing the journey of a medical image is the first step in identifying security gaps. This mapping should account for every hop a file takes, from the initial scan at the modality to its storage in a PACS and its eventual routing to an AI engine.
- Workflow Integrity: Clearly define the paths for AI inference and how results are returned to the clinical viewer.
- Edge Cases: Include documentation for secondary flows like backups, system exports, and support team access during troubleshooting.
2. Secure DICOM And DICOMweb Transfers
Modern imaging platforms often rely on web-based protocols to move large datasets across networks. Implementing encrypted transmission using TLS 1.2 or higher is a non-negotiable requirement for protecting data in transit.
- API Gateways: Use secure gateways to manage authenticated endpoints and filter incoming requests.
- Monitoring: Establish routing rules and connection monitoring to detect and handle failed transfers or unauthorized connection attempts.
3. De-Identify Imaging Data Before Secondary Use
When data is used for model training or research, all identifying markers must be systematically removed. This process goes beyond simple header stripping and must address data embedded within the images themselves.
- Metadata Stripping: Remove all identifying tags from the DICOM header while preserving essential clinical parameters.
- Visual Redaction: Use automated detection to find and mask burned-in text and patient overlays on the actual scan.
4. Protect Data During AI Inference
The actual processing of an image by a machine learning model requires a highly controlled environment. Isolating the inference engine ensures that temporary files or memory traces do not become a source of data leakage.
- Environment Isolation: Use containerization to separate the AI workspace from the rest of the enterprise network.
- Preprocessing Security: Ensure that any temporary files created during image normalization are encrypted and purged immediately after use.
5. Protect Image Integrity And Availability
Maintaining the accuracy of a medical record is just as important as maintaining its privacy. Implementing integrity checks ensures that an image has not been altered or corrupted during its journey through the pipeline.
- Validation: Use checksums to verify that the file received at the AI endpoint is identical to the one sent from the hospital.
- Redundancy: Develop downtime workflows and backup recovery plans to ensure clinical services remain available during system failures.
6. Control Storage Across Cloud, On-Prem, And Hybrid Environments
Choosing where to store imaging data involves balancing accessibility with strict regional and security constraints. Encrypted storage at rest must be the standard across all environments, whether they are local servers or distributed cloud buckets.
- Retention Rules: Implement automated deletion policies to ensure that data is not stored longer than legally required.
- Access Restrictions: Use role-based controls to limit who can modify or delete stored images and their associated backups.
Securing these data flows provides the technical assurance that a platform can handle sensitive clinical workloads at scale. This rigorous approach to pipeline integrity is what separates an experimental tool from a market-ready enterprise solution.
How To Control Access Across Clinical And AI Teams
Managing a diverse workforce of clinicians and technologists requires a sophisticated permissions framework that prevents unauthorized data exposure. Security in this domain relies on ensuring that individuals can only interact with the specific datasets required for their professional functions.
By implementing granular controls, an organization can maintain high operational velocity without compromising the privacy of the patient populations they serve.
1. Use Role-Based Access Control For Every User Type
A standardized permission model ensures that access is granted based on job functions rather than individual requests. This approach simplifies the management of large teams and ensures consistency across the enterprise.
- Clinical Roles: Radiologists and technologists receive full access to diagnostic-quality images and patient identifiers for clinical care.
- Technical Roles: AI engineers and data scientists are restricted to de-identified datasets to protect privacy during model development.
- Administrative Roles: Compliance officers and hospital admins access audit logs and reporting tools without needing to view clinical images.
- External Partners: Vendors and annotators operate within sandboxed environments with limited, project-specific visibility.
3. Apply Minimum Necessary Access To Imaging Data
The principle of minimum necessary access dictates that users should only see the data essential for their current task. This strategy limits the “blast radius” in the event of a credential compromise by narrowing the scope of available information.
Therefore, access is filtered by study type, project scope, and clinical site. An annotator working on a chest X-ray project does not need access to neurology records or patient billing information. Implementing these boundaries ensures that data exposure is always proportional to the requirements of the workflow.
3. Add SSO, MFA, And Strong Authentication
Foundational security starts with verifying the identity of every user before they enter the platform. Integrating with existing enterprise identity providers ensures that password policies and employee offboarding are managed centrally.
- Multi-Factor Authentication: Requires a second form of verification to prevent unauthorized entry via stolen credentials.
- Session Controls: Implements automatic timeouts and device trust requirements to secure workstations in busy clinical environments.
- Login Monitoring: Tracks authentication patterns to detect and block suspicious activity in real time.
4. Restrict Support And Engineering Access To PHI
Technical teams often require temporary access to live environments to troubleshoot performance issues or bugs. However, this access must be strictly governed to prevent it from becoming a permanent back door into sensitive databases.
- Time-Bound Access: Permissions are granted for a specific window and expire automatically once the task is complete.
- Masked Data: Support tools should display obfuscated patient details whenever possible to minimize unnecessary exposure.
- Justification Logs: Engineers must provide a documented reason for accessing production environments, creating a clear paper trail for compliance reviews.
5. Use Break-Glass Access With Full Audit Trails
In rare emergency scenarios, certain users may need to bypass standard restrictions to ensure patient safety or system stability. This “break-glass” mechanism provides a controlled way to escalate privileges during a crisis while maintaining absolute accountability.
Every instance of emergency access triggers immediate alerts to the compliance and security teams. Post-access reviews are mandatory to document the justification and ensure that all temporary privileges are revoked. This structured escalation path protects the organization by ensuring that even exceptional actions are fully transparent and auditable.
Granular access management transforms security from a restrictive barrier into a strategic enabler of trust. Establishing these protocols ensures that a platform can support complex, multi-disciplinary teams while meeting the highest standards of data stewardship.
How To Manage Vendors, BAAs, And Cloud Infrastructure
Building a scalable imaging platform involves an ecosystem of third-party services that must all align with federal privacy mandates. When an organization utilizes external cloud storage or specialized AI models, the regulatory perimeter expands to include those partners.
Therefore, leadership must implement a rigorous vendor management strategy to ensure that every link in the supply chain maintains the same level of integrity as the core platform.
1. Identify Every Vendor That Touches PHI
Transparency regarding data access is a prerequisite for a compliant enterprise architecture. It is essential to audit every service provider that interacts with imaging data or patient metadata during the development and deployment phases.
- Infrastructure Partners: Cloud hosting providers and database management services.
- Operational Tools: Error logging, system monitoring, and diagnostic analytics platforms.
- Development Services: Third-party labeling teams and external AI model vendors used for specialized inference.
2. Sign BAAs With Business Associates
A Business Associate Agreement is a legal contract that binds a vendor to HIPAA regulations. While these documents are mandatory, they serve as the floor rather than the ceiling for security expectations.
Establishing these agreements ensures that responsibilities are clearly documented and that the vendor is legally liable for data protection. However, a BAA alone is not enough to guarantee safety. Organizations must verify that the vendor actually possesses the technical safeguards promised in the contract.
3. Review Cloud Infrastructure For HIPAA Readiness
Public cloud providers offer HIPAA-eligible services, but the responsibility for secure configuration remains with the enterprise. A thorough review of the cloud environment ensures that sensitive imaging data is isolated and protected from common internet threats.
- Key Management: Maintain exclusive control over encryption keys to ensure data remains unreadable even to the cloud provider.
- Network Segmentation: Use virtual private clouds and firewalls to prevent unauthorized lateral movement within the infrastructure.
- Persistent Monitoring: Enable detailed logging and real-time alerts for any configuration changes or suspicious access patterns.
4. Protect Physical And Hosted Infrastructure
Security concerns extend beyond the digital realm into the physical locations where data is processed or stored. Whether utilizing on-premise servers or a hosted data center, strict environmental controls are necessary to prevent hardware theft or unauthorized physical access.
Workstation access in imaging rooms must be restricted to authorized clinical staff through biometric or card based entry systems. Furthermore, procedures for the secure disposal of old hardware and the protection of backup media are critical. These physical safeguards ensure that PHI cannot be retrieved from discarded or stolen equipment.
5. Control Subcontractor And Third-Party Risk
The risk profile of an organization is often dictated by the weakest link in its downstream partnerships. If a primary vendor uses subcontractors to process data, those secondary parties must also be vetted and bound by similar privacy obligations.
- Security Questionnaires: Conduct annual reviews of vendor security postures to identify emerging vulnerabilities.
- Breach Obligations: Ensure that all contracts include specific timelines for reporting security incidents to the primary organization.
6. Define Data Residency And Deletion Rules
Legal requirements often dictate exactly where patient data can be stored and how long it must be kept. Governance policies must clearly define these parameters to avoid regulatory penalties and reduce the long-term liability of holding unnecessary data.
Retention rules should specify who has the authority to delete records and how that deletion is verified. Archive governance ensures that even long-term storage remains encrypted and accessible only for legitimate clinical or legal reasons. Implementing these rules provides a clear lifecycle for every image processed by the platform.
Managing the technical and legal complexities of a vendor ecosystem is a hallmark of a mature healthcare enterprise. By centralizing these controls, an organization can leverage global cloud scale while maintaining the local trust of its clinical partners.
What Documentation Proves HIPAA Readiness
For any enterprise, documentation is the objective evidence of compliance that satisfies institutional auditors and federal regulators. It transforms abstract security practices into a verifiable framework that proves a platform can be trusted with sensitive clinical data.
Maintaining a centralized repository of these records is a prerequisite for passing the complex security reviews required by major health systems.
1. PHI Inventory And Data Flow Maps
A comprehensive inventory acts as the master record for every piece of sensitive data entering the system. Data flow maps visualize how this information moves and transforms, ensuring there are no undocumented leaks in the technical pipeline.
- Ingestion Points: Documentation of where and how PHI enters the platform from external modalities or hospital systems.
- Transformation Logs: Records of how data is de-identified or modified during the AI inference process.
- Storage and Export: Clear diagrams showing where data is stored and the authorized paths for it to leave the platform.
2. Security Risk Analysis And Risk Management Plan
This documentation proves that the organization has systematically identified potential threats and implemented specific safeguards to mitigate them. It must be updated periodically to reflect changes in the technical architecture or the broader cybersecurity landscape.
The risk management plan defines ownership for every identified vulnerability and establishes a clear timeline for remediation. It includes a detailed review of technical likelihood and business impact. Therefore, this plan serves as a living document that guides the strategic security investments of the enterprise.
3. Access Matrix And User Permission Records
An access matrix defines exactly which roles have permission to view or modify specific types of data. This record ensures that the principle of minimum necessary access is enforced consistently across all clinical and technical teams.
- Role Definitions: Documentation of the specific permissions assigned to radiologists, engineers, and administrators.
- Approval Workflows: Records of how access is requested, reviewed, and granted for internal and external users.
- Audit Reviews: Periodic logs showing that user permissions are regularly audited and revoked when no longer necessary.
4. Policies, Procedures, And Staff Training Records
Standard Operating Procedures (SOPs) provide the governing rules for how the workforce interacts with sensitive data. Furthermore, documentation of staff training proves that every individual in the organization understands their legal responsibilities under HIPAA.
- Acceptable Use: Policies defining the secure use of workstations, mobile devices, and remote access tools.
- Incident Reporting: Step-by-step procedures for how employees must report potential security breaches or data leaks.
- Acknowledgment Records: Signed verification that every staff member has completed mandatory privacy and security training.
5. Patient Rights And Disclosure Records
HIPAA grants patients specific rights regarding their medical data, and an organization must document its ability to honor these requests. This includes tracking every instance where data was shared outside the primary clinical workflow.
- Access Requests: Logs of patient requests to view or receive a copy of their medical imaging records.
- Accounting of Disclosures: A formal record of PHI shared for research, legal requirements, or public health purposes.
- Authorization Records: Documentation of specific patient consent for any data use not covered under standard clinical care.
6. Vendor Files, BAAs, And Security Reviews
Management of third-party risk must be thoroughly documented to protect the primary organization from downstream liabilities. This section of the compliance file includes all legal contracts and periodic evaluations of vendor security performance.
The vendor file contains a complete list of business associates and their signed agreements. It also includes completed security questionnaires and documentation of audit rights exercised by the organization. Maintaining these records ensures that the entire supply chain remains accountable for the safety of patient health information.
Detailed documentation provides the structural integrity needed to withstand a federal audit or a high-level corporate due diligence process. It ensures that compliance is not just a technical state but a repeatable and provable business operation.
Common HIPAA Compliance Mistakes In AI Imaging Platforms
Regulatory failures often stem from a misunderstanding of how deeply patient data is woven into the technical fabric of an artificial intelligence system. While many organizations focus on primary databases, they frequently overlook the secondary pathways where information can leak.
Recognizing these common pitfalls allows leadership to implement more resilient safeguards before they result in a formal audit or a public breach.
1. Treating DICOM Metadata As Non-Sensitive
A frequent error is assuming that removing a patient’s name from a file header constitutes full anonymization. DICOM files contain hundreds of metadata tags that can carry enough indirect identifiers to re-identify an individual.
- Hidden Fields: Institution names or specific scan dates can be cross-referenced with public records.
- Deep Review: Platforms must utilize automated tools to scrub private vendor tags that standard cleaners often ignore.
2. Access Production PHI Without Controls
Engineering teams sometimes bypass security protocols during high-pressure debugging sessions. Granting broad or permanent access to production environments for troubleshooting is a significant compliance violation.
- Temporary Gaps: Using screenshots or unencrypted exports during support tickets creates unmonitored data silos.
- Access Reviews: Failing to revoke temporary permissions immediately after a task is completed leaves the platform vulnerable.
3. Using Training Data Without Proper De-Identification
Model training requires massive datasets, but using raw images without rigorous de-identification is a major liability. Data leaks often occur within the labeling environments where annotators may see unredacted patient details.
- Annotation Risks: Comments or bounding box labels may inadvertently include clinical identifiers.
- Re-identification: Without proper pixel-level scrubbing, burned-in text can remain visible to the development team.
4. Forgetting Logs, Caches, And Telemetry
Operational data is often the most neglected area of a compliance strategy. System logs and API traces can accidentally capture snippets of raw data during failed jobs or performance monitoring.
- Temporary Files: Inference caches and backup copies must be encrypted and purged according to strict retention policies.
- Analytics Tools: Third-party monitoring services might ingest PHI if data flows are not properly filtered at the source.
5. Signing BAAs Without Vendor Monitoring
Many leaders believe a signed contract is the end of their compliance obligation. However, a Business Associate Agreement is only effective if the organization actively monitors the vendor’s actual security practices.
- Oversight Gaps: Failing to review subcontractor agreements or audit vendor access controls can lead to a chain of liability.
- Breach Workflows: Without pre-defined incident response coordination, a vendor breach can spiral into an enterprise-wide crisis.
6. Ignoring New Cybersecurity Expectations
Regulatory standards are not static and are currently evolving to meet modern threats. The Department of Health and Human Services (HHS) has proposed updates to the HIPAA Security Rule to strengthen protections around electronic data.
- Proactive Testing: Enterprises should prioritize multi-factor authentication and regular technical testing to stay ahead of upcoming requirements.
- Evolving Laws: Framing compliance as a continuous improvement process ensures the platform remains ready for future legal shifts.
Avoiding these common mistakes transforms a security posture from reactive to proactive. This strategic foresight is what builds a defensible and trustworthy imaging platform in a competitive healthcare market.
How Intellivon Builds HIPAA-Compliant AI Imaging Platforms
Engineering a diagnostic platform requires a deep fusion of medical imaging standards and rigorous federal security protocols. Intellivon approaches every project by prioritizing a security-first architecture that anticipates the complexities of hospital IT environments.
By embedding compliance into the core of the development lifecycle, the transition from a technical prototype to a market-ready clinical solution is streamlined and risk-averse.
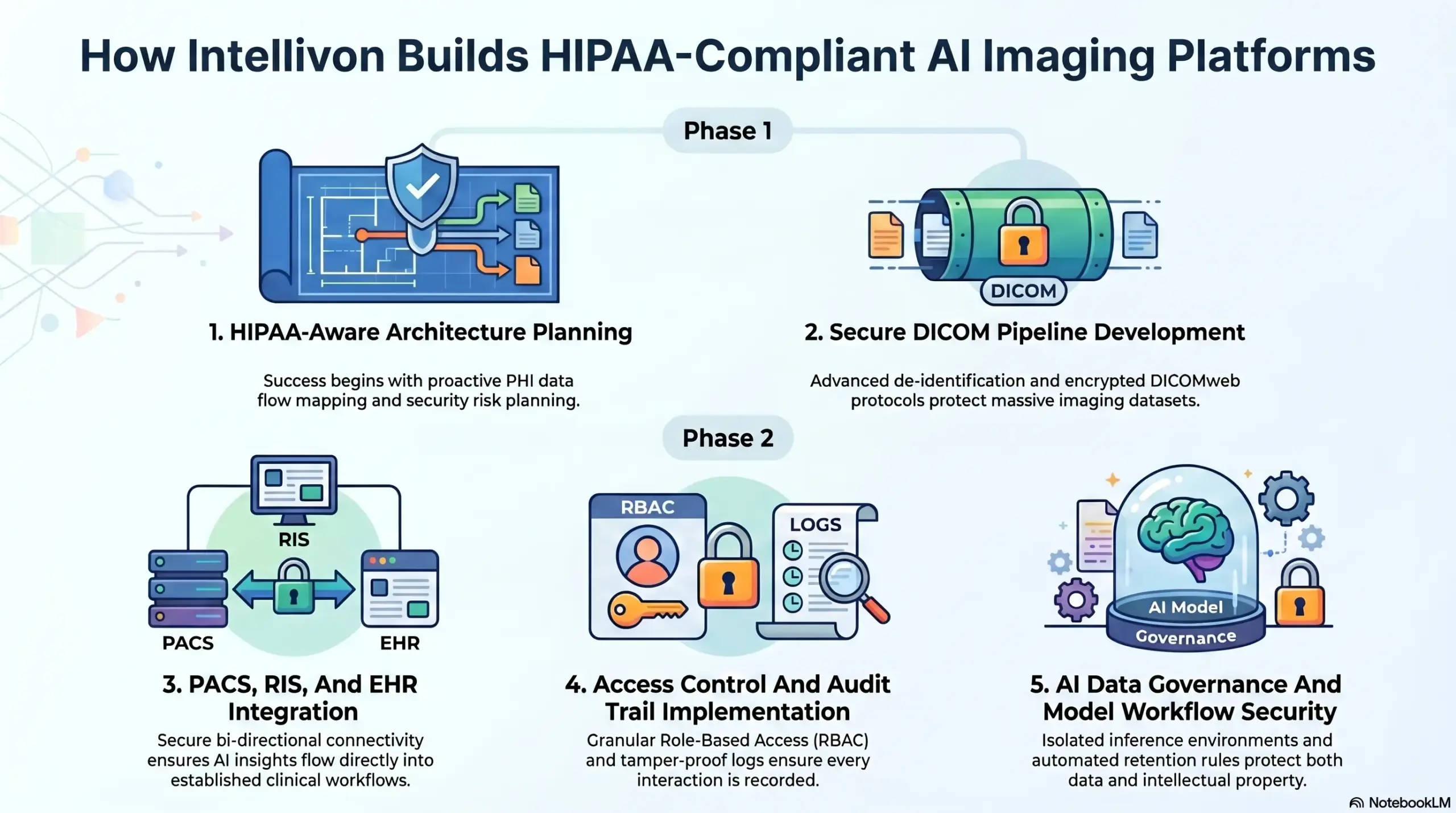
1. HIPAA-Aware Architecture Planning
Success begins with a comprehensive blueprint that accounts for every potential data touchpoint before a single line of code is written. This proactive planning phase ensures that the platform is built to withstand the scrutiny of institutional review boards and federal auditors alike.
- PHI Data Flow Mapping: We visualize the entire journey of patient data to identify and secure every point of ingress and egress.
- Security Risk Planning: Our team conducts early-stage assessments to address vulnerabilities in cloud configurations and third-party integrations.
- Hospital Review Readiness: We structure all technical documentation to align with the specific requirements of hospital procurement and legal departments.
2. Secure DICOM Pipeline Development
Intellivon develops high-performance pipelines designed to handle massive imaging datasets without compromising privacy. We focus on the integrity of the DICOM standard while implementing automated de-identification layers essential for AI research and clinical use.
- Advanced De-identification: We implement sophisticated workflows to scrub sensitive metadata and redact burned-in text from image pixels.
- Secure Transfer: All data movement utilizes encrypted DICOMweb protocols and TLS-secured API gateways to prevent interception.
- Integrity Checks: Every file is validated through checksums and study-matching protocols to ensure diagnostic accuracy remains uncompromised.
3. PACS, RIS, And EHR Integration
A standalone AI is only valuable if it integrates seamlessly into the existing clinical ecosystem. We bridge the gap between AI engines and hospital databases, ensuring that data flows are both efficient and protected.
- Bi-Directional Connectivity: We secure the routing of images from the PACS to the AI engine and the subsequent delivery of results back to the radiologist’s viewer.
- EHR Data Exchange: Our integrations ensure that clinical context from Electronic Health Records is utilized securely to improve model performance.
- Workflow Support: We connect AI outputs directly to reporting systems, allowing clinicians to utilize insights within their established diagnostic workflows.
4. Access Control And Audit Trail Implementation
We build granular permission structures that enforce the principle of minimum necessary access across the entire organization. This ensures that every interaction with patient data is authorized, monitored, and permanently recorded.
- Role-Based Access (RBAC): We define strict permissions for clinicians, engineers, and administrators to prevent over-privileged access.
- Comprehensive Audit Logs: Every action, from an image view to a system export, is tracked in a tamper-proof log for compliance reporting.
- Break-Glass Controls: We implement emergency access mechanisms that provide necessary clinical flexibility while maintaining an absolute audit trail.
5. AI Data Governance And Model Workflow Security
Protecting the intellectual property of a model is as critical as protecting the data used to train it. We establish secure environments for the entire AI lifecycle, from raw data ingestion to the delivery of live predictions.
- Dataset Governance: We implement strict controls over how training and validation datasets are stored, accessed, and reused.
- Inference Security: Our inference environments are isolated through containerization to prevent data leakage during live processing.
- Retention and Deletion: Automated rules ensure that data is only retained for the duration required by law or contract before being securely purged.
By partnering with Intellivon, enterprises gain access to a technical framework designed for the highest level of clinical trust. We transform the challenges of HIPAA compliance into a strategic advantage for sustainable growth in the digital health market.
Conclusion
Securing an AI medical imaging platform is a strategic investment in long-term enterprise viability. By prioritizing rigorous data governance and technical safeguards, organizations transform regulatory hurdles into a foundation of clinical trust.
This proactive approach not only mitigates significant legal risks but also ensures that innovative diagnostic tools are prepared for seamless integration into the global healthcare ecosystem, driving sustainable growth and improved patient outcomes.
Build HIPAA-Compliant AI Imaging Platforms With Intellivon
At Intellivon, we develop AI imaging platforms for hospitals, diagnostic imaging chains, teleradiology providers, radiology SaaS companies, healthcare enterprises, and medical imaging startups.
Our engineering approach focuses on privacy-first data flows, secure imaging infrastructure, clinical workflow integration, and audit-ready platform design.
A. Designing HIPAA-Aware Platform Architecture
We start by mapping how PHI enters, moves, transforms, and exits the platform. This helps teams identify privacy and security risks before development begins.
Our architecture planning covers DICOM workflows, PACS/RIS connections, AI inference points, storage systems, support access, vendor touchpoints, audit requirements, and deployment models.
B. Building Secure DICOM And Imaging Data Pipelines
We build secure imaging pipelines that protect patient data across ingestion, preprocessing, routing, storage, and AI processing.
This includes DICOM ingestion, DICOMweb support, metadata handling, de-identification workflows, encrypted transfer, image integrity checks, temporary file controls, and secure storage across cloud, on-prem, or hybrid environments.
C. Protecting PHI Across AI Workflows
AI imaging platforms often expose PHI through training datasets, annotations, inference records, model outputs, logs, exports, and monitoring tools. We design controls around each of these points.
Intellivon helps secure dataset governance, annotation workflows, AI inference environments, validation data, role-based access, data retention, output review, and reuse approvals.
D. Integrating With PACS, RIS, EHR, And Hospital Systems
We connect AI imaging platforms with the systems clinical teams already use while keeping PHI protected across the workflow.
This includes PACS integration, RIS workflow connection, EHR data exchange, AI result routing, viewer integration, reporting workflow support, secure API development, and hospital IT coordination.
Intellivon builds systems that help teams monitor PHI access, detect unusual activity, manage logs, review permissions, prepare compliance documentation, and support hospital security reviews over time.
If you are planning to build an AI medical imaging platform, contact Intellivon to design a secure, HIPAA-aware, and enterprise-ready system from the first architecture decision.
FAQs
Q1. Does HIPAA apply to AI medical imaging platforms?
A1. Yes. HIPAA applies when an AI medical imaging platform creates, receives, maintains, or transmits protected health information for a covered entity or business associate. This can include DICOM files, metadata, reports, annotations, AI outputs, logs, exports, and linked clinical records.
Q2. What is PHI in AI medical imaging?
A2. PHI in AI medical imaging includes patient identifiers inside scans, DICOM metadata, radiology reports, annotations, labels, worklists, model outputs, access logs, and exported files. Even technical records can contain sensitive patient data if they link back to an individual.
Q3. How can AI imaging platforms protect PHI?
A3. AI imaging platforms protect PHI through encryption, de-identification, access controls, audit logs, secure DICOM routing, vendor controls, BAAs, risk analysis, monitoring, and incident response workflows. These controls should be built into the platform architecture, not added later.
Q4. Are BAAs required for AI medical imaging vendors?
A4. BAAs are required when vendors handle PHI on behalf of covered entities or business associates. AI vendors, cloud providers, labeling partners, analytics tools, and support teams may need BAAs depending on their role, data access, and responsibilities.
Q5. What is the biggest HIPAA risk in AI imaging?
A5. The biggest risk is hidden PHI movement. Patient data can appear in DICOM headers, burned-in image text, logs, annotations, exports, caches, telemetry tools, and support workflows. Enterprises must map every data flow to understand where PHI lives and how it is protected.