Key Takeaways
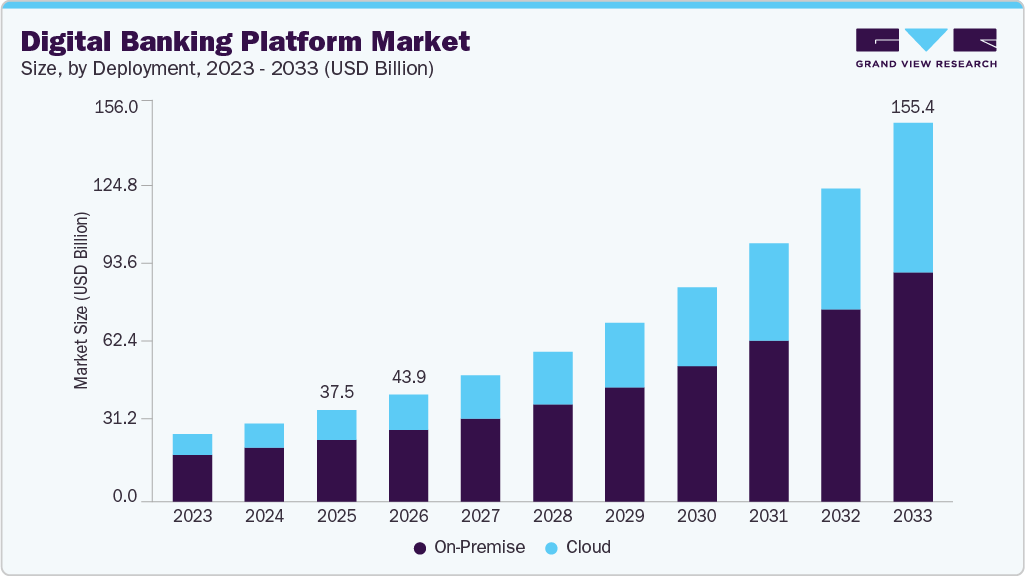
- The digital banking platform market is expected to reach USD 155.44 billion by 2033. Platforms built with compliance infrastructure from day one are positioned to capture that growth with institutional trust already established.
- AML transaction monitoring, KYC/KYB verification, sanctions screening, and immutable audit trails form the technical baseline that regulators verify before any platform goes live.
- BaaS models now require fintech partners to operate at bank-grade standards. Daily reconciliation, documented compliance SLAs, and dedicated compliance ownership are what sponsor banks look for before approving a partnership.
- AI deployed in banking workflows must be explainable, auditable, and bias-tested. Regulators expect a clear reasoning trail behind every automated financial decision.
- How Intellivon’s pre-vetted ASP.NET MVC and .NET MAUI developers, who are screened for regulatory-grade architecture depth, compliance-first design standards, and enterprise security practices, can help you build a compliance-ready banking platform that satisfies regulators, attracts institutional partners, and scales with confidence.
Every enterprise banking system has a legal duty the moment it processes a transaction. This obligation becomes clear the instant a platform handles payments, signs up a business client, or transfers funds across borders. It enters a complex network of rules that covers AML, KYC, data privacy, operational resilience, and preventing financial crime.
Banking compliance software is a layered setup of federal laws, international standards, and specific requirements from each institution that must all work together without any gaps. Enterprises need to know not only if compliance is important, but which specific requirements apply, the order in which to build them, and how they interact within a live banking system.
Intellivon has created compliant enterprise banking infrastructure systems for global financial institutions, embedding regulatory requirements from the beginning in areas like AML, KYC, data governance, and operational resilience frameworks. This blog covers our experience in detail on how we construct such systems from scratch.
Why Compliance Is Crucial For Digital Banking Systems Now
Compliance is no longer a back-office function in digital banking. It is a core infrastructure requirement. Banks and fintechs today handle sensitive data at scale, faster payment flows, and deeper third-party integrations than any previous generation of financial systems.
Therefore, regulators and enterprise clients both demand stronger controls across security, privacy, fraud prevention, and operational resilience.
The scale of this shift is measurable. Digital banking platforms represented a USD 37.49 billion market in 2025 and are forecast to cross USD 155.44 billion by 2033, a compound annual growth rate of 19.8%.
1. Rising Regulatory Pressure
Regulations now directly shape how banking products are built and monitored. Consequently, compliance failures carry real costs, like fines, license restrictions, reputational damage, and lost enterprise contracts.
2. More Complex Risk Exposure
APIs, cloud platforms, mobile apps, and fintech integrations widen the attack surface considerably. However, the bigger risk is structural. Regulators now hold institutions accountable for their partners’ compliance standards, not just their own.
A weak link in any third-party arrangement can trigger enforcement against the primary platform.
3. Customer Trust And Market Confidence
In digital channels, customers never interact with a physical branch. Their trust lives entirely in the platform experience. Strong compliance signals protection, and institutional clients verify that posture before reviewing commercial terms.
4. Enabling Scalable Growth
Compliance built into a system from day one enables faster market entry, cleaner due diligence, and stronger investor confidence. In addition, it reduces the cost and disruption of regulatory retrofits during scaling.
Compliance protects institutions from risk while enabling the growth that digital banking demands. It is the foundation that makes sustainable scaling possible.
What Rules Apply to Enterprise Banking Systems?
Maintaining an enterprise banking platform requires a rigorous commitment to global regulatory standards to ensure financial integrity and operational resilience.
These frameworks protect the institution from legal penalties while building the trust necessary to scale in a competitive market.
1. BSA, AML, and suspicious activity obligations
The Bank Secrecy Act (BSA) and Anti-Money Laundering (AML) laws form the bedrock of financial security. Banks must implement systems that detect patterns indicative of money laundering or terrorist financing.
- Transaction Monitoring: Automated tools flag unusual spikes in volume or rapid movement of funds across borders.
- SAR Filing: Institutions are legally required to file Suspicious Activity Reports (SARs) when they identify potential criminal behavior.
- Internal Controls: Effective programs include independent audits and a designated compliance officer to manage systemic risks.
2. KYC, KYB, CDD, and EDD requirements
Verifying the identity of users is no longer a manual process but a digital necessity. Know Your Customer (KYC) and Know Your Business (KYB) processes prevent fraud before it enters the ecosystem.
- Customer Due Diligence (CDD): This involves collecting basic identity markers like names, addresses, and tax IDs.
- Enhanced Due Diligence (EDD): High-risk clients, such as politically exposed persons, require deeper investigation into their source of wealth.
- Verification Layers: Using biometric checks and database cross-referencing speeds up onboarding while maintaining security.
3. GLBA and privacy rules for banking platforms
The Gramm-Leach-Bliley Act (GLBA) mandates that financial institutions protect the private data of their customers. You must provide clear notices about how data is shared and offer opt-out rights.
- Data Safeguards: Encrypting sensitive information at rest and in transit is a core requirement.
- Privacy Policies: Transparency regarding data usage builds consumer confidence and satisfies federal auditors.
4. PCI DSS requirements for payment systems
If your platform handles credit or debit card transactions, the Payment Card Industry Data Security Standard (PCI DSS) is mandatory. It ensures that cardholder data is never compromised during processing.
- Network Security: Maintaining a firewall and avoiding vendor-supplied default passwords is critical.
- Access Control: Restricting data access to only those who need it minimizes the internal threat surface.
5. FFIEC guidance and security expectations
The Federal Financial Institutions Examination Council (FFIEC) provides a uniform set of principles for financial examiners. Following this guidance ensures your tech stack meets the expectations of US regulators.
- Cybersecurity Framework: It emphasizes proactive threat hunting rather than just reactive patching.
- Risk Management: Leaders must demonstrate that they understand the digital risks associated with their specific banking services.
6. DORA rules for EU-facing banking platforms
The Digital Operational Resilience Act (DORA) is essential for any platform operating within the European Union. It shifts the focus from purely financial health to digital uptime and security.
- Incident Reporting: Systems must have protocols to report major ICT-related incidents to authorities quickly.
- Resilience Testing: Regular stress tests of your digital infrastructure are required to ensure business continuity during an attack.
7. ECOA and fair lending requirements
The Equal Credit Opportunity Act (ECOA) prevents discrimination in any aspect of a credit transaction. When building automated lending models, fairness must be baked into the algorithm.
- Algorithmic Bias: Regular audits of AI credit scoring models ensure no group is unfairly denied access to capital.
- Adverse Action: You must provide specific reasons to applicants when credit is denied, ensuring a transparent process.
8. ISO 20022 compliance in payment systems
ISO 20022 is the emerging global standard for financial messaging. It allows for much richer data to be sent with every payment, improving transparency and reducing errors.
- Structured Data: This standard replaces older, cluttered formats with organized XML messages.
- Interoperability: Adopting this ensures your platform can communicate seamlessly with global clearing houses and other major banks.
These regulations serve as a strategic roadmap for building a secure, scalable financial platform in a complex global market. Adherence to these standards transforms compliance from a hurdle into a significant competitive advantage.
Why Does Compliance Shape Banking System Design?
Regulatory requirements act as the structural blueprint for modern financial platforms rather than an afterthought. Integrating these standards into the initial design phase prevents costly re-engineering and ensures the system can withstand intense scrutiny from auditors.
1. Compliance as an architectural requirement
Software architecture in banking must prioritize data integrity and auditability from the first line of code. Therefore, developers build immutable ledgers that track every movement of capital without the possibility of unauthorized deletion.
- Audit Trails: Every API call and database change must be logged with a timestamp and user ID.
- Data Segregation: Sensitive personally identifiable information stays separated from transactional data to limit exposure during a breach.
- Modular Design: Regulations change frequently, so the system needs a modular structure that allows for updates to specific compliance rules without breaking the entire platform.
2. Why buyers assess compliance before features
Institutional investors and corporate clients prioritize stability over flashy user interfaces because a single regulatory failure can halt operations. They seek assurance that the platform will not become a liability that attracts heavy fines or reputational damage.
- Due Diligence: Potential partners will scrutinize your security certifications before discussing interest rates or transaction speeds.
- Market Entry: Compliance acts as the primary barrier to entry; without it, your platform cannot legally connect to global payment rails.
- Longevity: A system built on shaky regulatory ground is viewed as a high-risk asset that may not survive future legislative shifts.
3. Why partner risk shapes platform reviews
Enterprise banking involves a web of third-party integrations, and each partner represents a potential point of failure. Consequently, decision-makers evaluate how your system manages the risks associated with these external connections.
- Vendor Risk Management: You must prove that your vendors, such as cloud providers or KYC engines, adhere to the same strict standards you do.
- Liability Mapping: Contracts and system logs must clearly define who is responsible for data security at every stage of a transaction.
- Contingency Planning: Sophisticated buyers look for fail-safes that allow the platform to continue operating if a key partner goes offline.
4. What does compliance-ready infrastructure mean?
Compliance-ready infrastructure refers to a tech stack that is pre-configured to meet high security and reporting standards. It provides a foundation where the necessary controls are already active, reducing the time required to go from development to launch.
- Automated Reporting: The system generates the necessary documents for regulators with minimal manual intervention.
- Encrypted Environments: Data is protected by advanced encryption protocols whether it is being stored or sent across a network.
- Continuous Monitoring: Real-time dashboards alert administrators to potential compliance gaps before they become actual violations.
Integrating these regulatory pillars into your design ensures the platform remains resilient and attractive to high-value investors. This strategic alignment turns technical requirements into a powerful engine for institutional growth.
What AML Controls Must Banking Systems Include?
Top-tier banking compliance software utilizes machine learning to refine AML controls, shifting from static rules to dynamic risk detection.
By integrating real-time sanctions screening and automated SAR workflows, enterprise leaders can reduce manual oversight while maintaining total regulatory alignment.
1. Identity verification and onboarding controls
The first line of defense begins during the initial user sign-up. Digital identity verification must be seamless yet robust enough to detect sophisticated document forgery.
- Document Authentication: Systems scan government IDs to verify security features like holograms and watermarks.
- Biometric Matching: Comparing a live selfie to the ID photo prevents “presentation attacks” where a fraudster uses a stolen identity.
- Liveness Detection: This ensures the person behind the screen is a real human, not a deepfake or a static image.
2. Business verification and ownership checks
For enterprise platforms, verifying a business entity is far more complex than verifying an individual. You must peel back corporate layers to understand who truly controls the funds.
- Ultimate Beneficial Ownership (UBO): Regulations require identifying any individual who owns more than 25% of the company.
- Registry Integration: Automated hooks into official government business registries confirm the entity is active and in good standing.
- Entity Mapping: Visualizing corporate hierarchies helps compliance teams spot shell companies or circular ownership structures.
3. Customer risk scoring and segmentation
Not every customer poses the same level of threat to your platform. Therefore, your system must categorize users based on their specific risk profile.
- Dynamic Scoring: Risk scores should update based on behavior, such as sudden changes in transaction frequency or geographic location.
- Segmentation: High-risk groups, such as cash-intensive businesses, receive more frequent scrutiny than low-risk retail users.
- Variable Thresholds: Monitoring rules adjust automatically; for example, a “low-risk” user might trigger an alert at a lower dollar amount than a “high-risk” institutional client.
4. Sanctions, watchlist, and PEP screening
Banking systems must cross-reference every participant against global databases of restricted individuals and entities. Failure to do so can result in massive federal penalties and immediate loss of banking licenses.
- Real-time Screening: Every transaction is checked against OFAC, UN, and EU lists before the funds are cleared.
- Politically Exposed Persons (PEP): Screening for government officials is vital because these individuals carry a higher risk of involvement in bribery or corruption.
- Adverse Media: Advanced systems also scan news reports to identify users involved in ongoing criminal investigations or scandals.
5. Transaction monitoring and alert logic
Monitoring must happen in real-time to stop illicit activity before it leaves the ecosystem. Intelligent alert logic identifies “red flags” without overwhelming your operations team.
- Pattern Recognition: The system looks for “structuring,” where users make multiple small deposits to avoid the 10,000 USD reporting limit.
- Velocity Checks: Rapid movement of funds across multiple accounts in a short window triggers an immediate hold.
- Geofencing: Flagging transactions that originate from or are sent to high-risk jurisdictions or sanctioned regions.
6. Case management and SAR support
When an alert is triggered, your team needs a centralized workspace to investigate and document their findings. This workflow must be standardized to satisfy regulatory auditors.
- Evidence Gathering: The system automatically pulls transaction history and KYC data into a single case file.
- SAR Automation: If suspicious activity is confirmed, the platform should pre-fill a Suspicious Activity Report (SAR) to save time.
- Audit Trails: Every decision made by an investigator must be logged to prove the bank followed its own internal protocols.
7. Ongoing monitoring and review cycles
Compliance is not a “one and done” event at onboarding. Financial institutions must perform regular “check-ups” on their existing client base to ensure their risk profile hasn’t shifted.
- Periodic Reviews: High-risk accounts are reviewed every six months, while lower-risk accounts might be checked every two years.
- Event-Driven Triggers: Significant changes, like a change in business ownership or a massive spike in revenue, trigger an out-of-cycle review.
- Continuous Updating: The system prompts users to refresh expired IDs or outdated business documentation automatically.
8. Reducing false positives with control integrity
Traditional systems often flag legitimate transactions, which frustrates customers and wastes staff time. Modern architecture focuses on precision to ensure only truly risky behavior is stopped.
- Tuning and Optimization: Compliance teams regularly adjust “fuzzy matching” logic to ensure the system isn’t flagging every person with a common last name.
- Whitelisting: Known, trusted partners with predictable transaction patterns can be given higher thresholds to reduce noise.
- Feedback Loops: When an investigator clears an alert as “false,” the system learns from that decision to improve future accuracy.
By building these AML controls directly into your core infrastructure, you protect your capital and your reputation. This proactive approach turns a regulatory burden into a streamlined, high-trust environment for your most valuable investors.
How Is KYB Different From KYC in Banking?
While both protocols aim to verify identity, the primary difference lies in the complexity of the entity being vetted and the depth of the investigation required. Understanding these nuances is vital for leaders building platforms that serve both individual consumers and corporate clients.
| Feature | Know Your Customer (KYC) | Know Your Business (KYB) |
| Primary Subject | Individual human beings. | Legal entities (LLCs, Corporations, Trusts). |
| Data Focus | Government IDs, SSNs, and biometrics. | Articles of incorporation, tax IDs, and UBOs. |
| Verification Depth | Verifying a single identity and address. | Mapping complex ownership and control structures. |
| Risk Assessment | Personal credit and individual watchlists. | Business reputation, industry risk, and partner links. |
| Onboarding Speed | Often near-instant via automated apps. | Can take days or weeks due to document reviews. |
Effective compliance design treats these as separate but interlinked workflows within the same ecosystem. By mastering both, an enterprise platform can securely facilitate transactions for a single retail user or a multinational conglomerate with equal precision.
What Privacy and Security Compliance Is Needed?
Data security is the cornerstone of institutional trust and a non-negotiable requirement for any enterprise-grade banking platform.
Protecting sensitive financial information requires a multi-layered approach that combines rigorous technical barriers with strict organizational policies.
1. GLBA Safeguards Rule expectations
The Gramm-Leach-Bliley Act (GLBA) requires financial institutions to explain their information-sharing practices to their customers and to safeguard sensitive data. Therefore, your platform must have a written information security program that is appropriate to its size and complexity.
- Risk Assessment: You must regularly identify and analyze risks to customer information in every area of your operations.
- Service Provider Oversight: Contracts must require your partners to maintain similar safeguards to protect the data you share with them.
- Program Updates: The security plan cannot be static; it must be adjusted based on the results of regular testing and monitoring.
2. Encryption and access control requirements
Encryption serves as the final line of defense, ensuring that even if data is intercepted, it remains unreadable to unauthorized parties. Access control reinforces this by ensuring that only verified personnel can interact with specific datasets.
- AES-256 Standards: All sensitive data at rest should be protected using Advanced Encryption Standard 256-bit keys.
- TLS for Transit: Data moving between your servers and the user’s device must be secured via Transport Layer Security.
- Least Privilege Principle: Employees should only have access to the minimum amount of data necessary to perform their specific job functions.
3. GDPR and banking rules overlap
For platforms serving European clients, the General Data Protection Regulation (GDPR) introduces strict rules regarding user consent and data portability. Consequently, banking systems must reconcile these privacy rights with traditional financial record-keeping laws.
- The Right to Erasure: While GDPR allows users to request data deletion, banking laws often require you to keep records for several years.
- Data Minimization: Only collect the data you absolutely need for the specific financial service being provided.
- Legal Basis: You must clearly define whether you are processing data based on user consent or to fulfill a legal obligation, like AML monitoring.
4. Retention and deletion policy design
Financial regulators mandate that certain records be kept for specific periods, often five to seven years, to facilitate future audits or investigations. An automated retention policy ensures you don’t keep data longer than necessary, which reduces your liability.
- Automated Archiving: Move older records to secure, low-cost storage while keeping them searchable for regulatory requests.
- Secure Disposal: When the retention period ends, data must be wiped using “crypto-shredding” or other permanent deletion methods.
- Legal Holds: The system must be able to “freeze” specific records if they are needed for an ongoing legal or regulatory matter.
5. Breach response recordkeeping needs
When a security incident occurs, the clock starts ticking on your legal obligation to notify regulators and affected users. Having a pre-defined record-keeping process allows you to demonstrate that you responded quickly and effectively.
- Incident Logs: Maintain a detailed timeline of when the breach was detected, what data was accessed, and how it was contained.
- Forensic Evidence: Store system snapshots and network logs to help investigators determine the root cause of the attack.
- Notification Templates: Prepare draft communications for different jurisdictions to ensure you meet varied reporting deadlines without delay.
Establishing these security pillars ensures your platform is not just a vault for capital, but a fortress for information. This level of protection is exactly what high-value investors look for when choosing a long-term financial partner.
How Has BaaS Changed Compliance Expectations?
The rise of Banking-as-a-Service (BaaS) has fundamentally shifted the regulatory landscape, moving away from loose oversight toward a model of deep, integrated accountability.
Therefore, enterprise leaders must recognize that while they may own the customer relationship, the underlying sponsor bank remains legally responsible for the platform’s integrity.
1. Stricter sponsor-bank oversight requirements
Regulators have recently intensified their focus on how banks manage their fintech partners. Banks must now demonstrate active, daily involvement in the partner’s activities.
- Continuous Monitoring: Sponsor banks now require direct access to your compliance dashboards to review alerts in real-time.
- Regular Audits: Expect frequent, deep-dive reviews of your internal processes, often conducted by third-party experts at the bank’s request.
- Pre-Approval Rights: Banks often insist on reviewing and approving any significant changes to your onboarding workflows or product features.
2. BSA and AML ownership in BaaS models
While a fintech may perform the day-to-day work of identity verification, the Bank Secrecy Act (BSA) obligations ultimately rest with the chartered institution. Consequently, the division of labor must be clearly documented to avoid gaps that bad actors could exploit.
- Joint Accountability: Both the platform and the bank must agree on the risk appetite and the specific “red flags” that trigger a report.
- Standardized Reporting: The platform must provide data in a format that allows the bank to file SARs efficiently and accurately.
- Staff Training: Your compliance team must be trained to the same rigorous standards as the bank’s own internal employees.
3. What sponsor banks now expect operationally
To mitigate their own risk, sponsor banks are demanding higher levels of operational maturity from their enterprise partners. They look for evidence that your compliance culture is led by experienced professionals rather than just automated scripts.
- Dedicated Compliance Officers: Having a qualified, senior-level person in charge of regulatory affairs is often a prerequisite for a partnership.
- Documented Procedures: Every manual process must be backed by a clear Standard Operating Procedure (SOP) that is updated regularly.
- Incident Escalation: There must be a clear, tested path for notifying the bank of any potential breaches or systemic errors.
4. Ledger and reconciliation control needs
Accurate record-keeping is the heartbeat of BaaS compliance. If your internal ledger does not match the bank’s core system down to the cent, it triggers immediate regulatory concern regarding the safety of customer funds.
- Daily Reconciliation: Systems must compare internal records against the bank’s movements every 24 hours to catch discrepancies early.
- Shadow Ledgers: Many platforms maintain a “shadow” version of the bank’s records to provide an extra layer of verification.
- Exception Management: When a mismatch is found, the system must have a clear workflow to investigate and resolve the error within a strict timeframe.
5. Defining shared compliance responsibilities
Success in a BaaS model depends on a “Compliance Service Level Agreement” (SLA) that explicitly states who does what. This clarity prevents the “finger-pointing” that often occurs during a regulatory exam.
- The Responsibility Matrix: A detailed chart should list every regulatory task, from KYC to data privacy, and assign it to either the bank or the platform.
- Data Portability: Ensure that if the partnership ends, you have clear rights to access and move historical compliance data to a new partner.
- Communication Channels: Regular, formal meetings between the compliance departments of both organizations are essential for staying aligned on new laws.
This evolved BaaS landscape demands a
sophisticated regulatory strategy. By mastering these shared responsibilities, enterprise platforms can build a foundation that is both highly innovative and defensively sound.
What Resilience Controls Should Banking Systems Have?
Financial regulators are now equally concerned with your digital uptime. Operational resilience ensures that your banking platform can absorb shocks, adapt to disruptions, and maintain core services during a cyberattack or systemic failure.
1. Operational resilience in banking systems
Operational resilience is the ability of an institution to deliver its critical operations through a disruption. Therefore, you must map out your most vital services and determine the maximum tolerable level of downtime for each.
- Critical Service Mapping: Identify which processes, such as real-time payments or account access, would cause the most harm if they failed.
- Impact Tolerances: Define exactly how long a system can be down before it causes significant damage to customers or the broader market.
- Adaptive Capacity: Your infrastructure should be able to scale or shift resources automatically when it detects a surge in traffic or a localized hardware failure.
2. DORA and third-party ICT oversight
The Digital Operational Resilience Act (DORA) mandates that financial entities maintain strict control over their tech providers. Consequently, your compliance strategy must extend beyond your own walls to include every cloud provider and API partner you use.
- Concentration Risk: Avoid relying on a single provider for all critical functions to prevent a “single point of failure” for your entire platform.
- Right to Audit: Your contracts must legally allow you—and your regulators—to inspect the security practices of your third-party vendors.
- Exit Strategies: You must have a documented plan for how to move your data and operations to a new provider if your current one fails or becomes non-compliant.
3. Regulator-ready incident response planning
When a system failure occurs, regulators expect a disciplined, pre-planned reaction. A “regulator-ready” plan focuses on transparency and rapid containment rather than just technical troubleshooting.
- Communication Trees: Establish clear lines of authority so that the right executives and authorities are notified within minutes of a detected breach.
- Classification Logic: Use a standardized system to rank incidents by severity, ensuring that your response resources are allocated to the most critical threats first.
- Playbook Documentation: Maintain specific “step-by-step” guides for common scenarios like DDoS attacks, database corruption, or unauthorized fund transfers.
4. Testing, failover, and recovery controls
Resilience must be proven through rigorous testing before an actual crisis occurs. Redundancy is useless if the “switch” to a backup system fails during a live event.
- Chaos Engineering: Intentionally inject failures into your system to see how it reacts and to identify hidden vulnerabilities.
- Geographic Redundancy: Store data and run applications in multiple, physically separate regions to protect against natural disasters or regional power grid failures.
- RPO and RTO: Set strict Recovery Point Objectives (how much data you can lose) and Recovery Time Objectives (how fast you must be back online) for every critical database.
5. Evidence needed after a major incident
After a disruption is resolved, the regulatory “post-mortem” begins. You must be able to prove exactly what happened and how you prevented the situation from escalating.
- Immutable Logs: Ensure your system logs cannot be altered after an incident, providing an honest record for forensic investigators.
- Root Cause Analysis (RCA): Document the technical or human failure that caused the issue and the specific steps taken to ensure it never happens again.
- Impact Statements: Provide data-driven reports on how many customers were affected and for how long, demonstrating that you stayed within your stated impact tolerances.
Building these resilience controls turns your platform into a dependable utility that institutional partners can trust. This structural stability is a primary selling point for investors who prioritize long-term security over short-term speed.
What AI Compliance Applies to Banking Platforms?
Regulators are increasingly focused on how AI influences financial outcomes and risk management.
Therefore, enterprise leaders must ensure that their AI deployments are transparent, ethical, and fully auditable to avoid significant legal and reputational fallout.
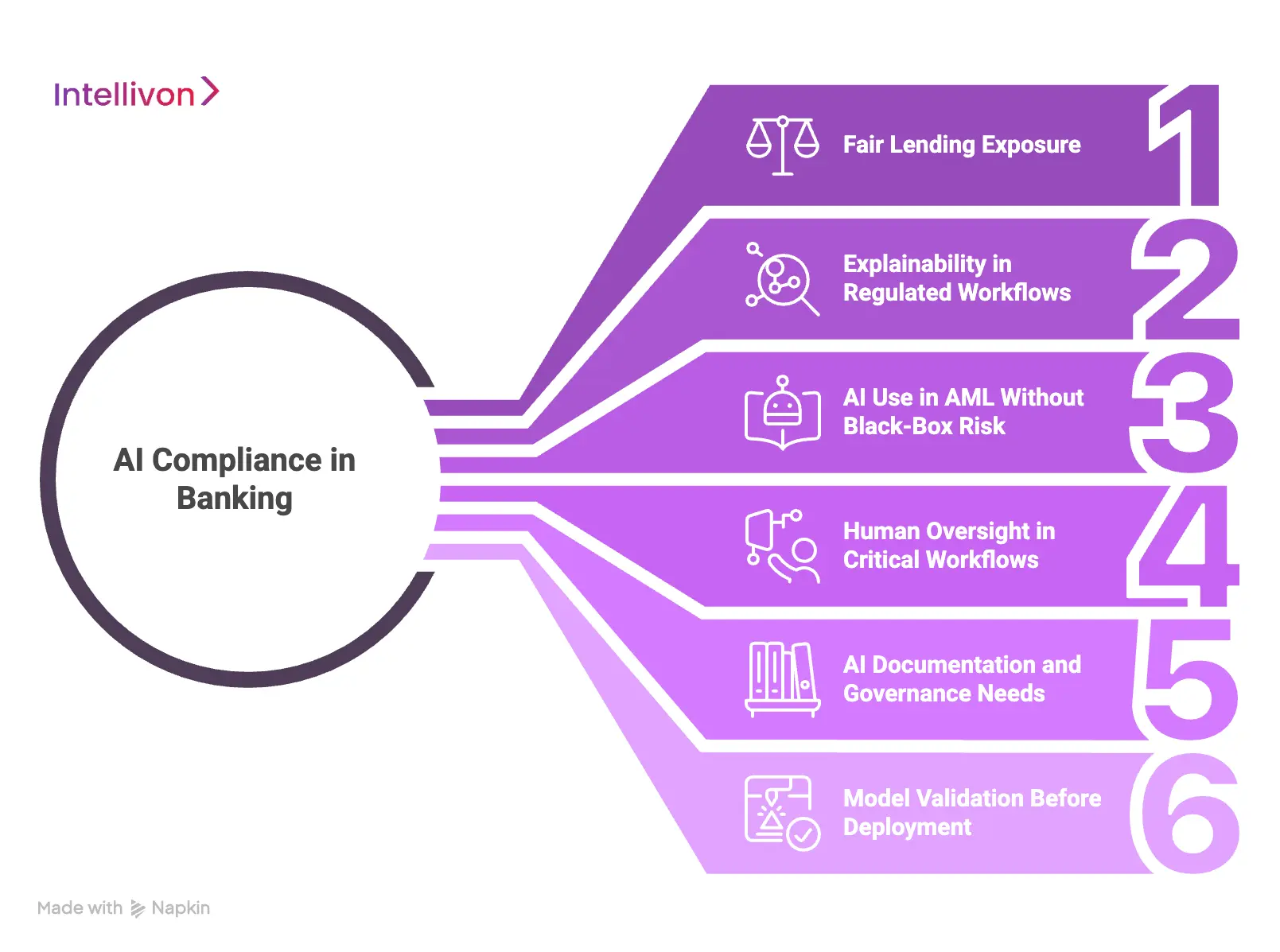
1. Fair lending exposure in AI-led decisions
Algorithms can unintentionally mirror historical human biases if they are trained on flawed datasets. Consequently, you must proactively test your models to ensure they do not discriminate against protected groups during the credit application process.
- Bias Auditing: Regular statistical reviews check for disparate impact across different demographic segments.
- Neutral Data Inputs: Avoid using variables that act as proxies for race or gender, such as specific zip codes or educational history.
- Corrective Tuning: If a model shows a bias toward one group, engineers must recalibrate the weighting to ensure fair and equal treatment for all applicants.
2. Explainability in regulated banking workflows
Regulators demand to know the “why” behind every automated decision, especially when a consumer is denied a service. This requirement for explainability prevents the use of opaque systems that cannot be audited.
- Local Interpretability: Your system should provide a specific reason for each individual outcome rather than just a general confidence score.
- Decision Trees: Using models that follow a logical, step-by-step path makes it easier for compliance officers to explain the results to examiners.
- Simplified Summaries: The platform should translate complex mathematical weights into plain language that a customer service representative can understand.
3. AI use in AML without black-box risk
While AI is excellent at spotting complex money laundering patterns, it must not operate in a “black box” where its logic is hidden. You must be able to demonstrate the specific red flags that triggered an automated AML alert.
- Feature Transparency: Maintain a list of the data points that the AI considers most important when flagging suspicious activity.
- Logic Mapping: Ensure that your data science team can walk an auditor through the mathematical reasoning used by the software.
- Standardized Outputs: Every AI-generated alert should come with a standardized report that justifies the investigation.
4. Human oversight in critical workflows
Automation should assist human decision-makers rather than replace them entirely in high-stakes banking scenarios. This “human-in-the-loop” approach ensures that empathy and professional judgment remain part of the process.
- Final Review Rights: A human compliance officer should have the final say on filing a Suspicious Activity Report (SAR).
- Override Protocols: Establish clear rules for when a human can go against an AI recommendation and how that decision is documented.
- Escalation Paths: If the AI is unsure about a specific transaction, it should automatically pass the case to a senior analyst for review.
5. AI documentation and governance needs
Every AI model you deploy must be accompanied by a comprehensive “paper trail” that describes its purpose and limitations. Proper governance proves to investors that you are managing your digital assets with institutional rigor.
- Model Inventories: Maintain a centralized list of all active algorithms, their versions, and their intended business functions.
- Usage Logs: Track where and when each AI model is being used across your entire enterprise banking platform.
- Policy Alignment: Ensure your AI usage complies with your internal data privacy and security policies.
6. Model validation before deployment
Before any algorithm goes live, it must pass through a strict validation phase to ensure it performs as expected in real-world conditions. This prevents “model drift,” where the AI becomes less accurate over time as market conditions change.
- Backtesting: Run the model against historical data to see if it would have correctly identified past risks or opportunities.
- Stress Testing: Put the AI through extreme scenarios to see how it behaves during a market crash or a massive spike in fraud.
- Ongoing Monitoring: After launch, the system must continuously check the model’s performance against a set of baseline metrics.
Implementing these AI safeguards ensures your platform remains at the cutting edge of technology without sacrificing regulatory safety. This balance is critical for attracting sophisticated investors who value both innovation and long-term stability.
How Do Cross-Border Rules Affect Compliance?
Operating a financial platform across international lines introduces a complex web of conflicting legal mandates.
Therefore, enterprise leaders must design their systems to be “jurisdiction-aware,” ensuring that every transaction respects the specific laws of both the sender and the receiver.
1. Overlap across US, EU, and UK rules
While the US, EU, and UK share similar goals regarding financial stability, their specific implementation methods often vary significantly. Consequently, a platform must be flexible enough to satisfy the strict privacy rules of the EU while meeting the aggressive reporting requirements of the US.
- Mutual Recognition: Some regions acknowledge each other’s standards, which can simplify the licensing process for your platform.
- Regulatory Divergence: Since the UK left the EU, its rules are slowly drifting away from European mandates, requiring separate compliance tracks for each market.
- Harmonized Standards: Leveraging international frameworks like the Basel Accords helps create a baseline that simultaneously satisfies most major Western regulators.
2. Regional data control requirements
Data sovereignty laws dictate where financial information can be stored and who is allowed to access it. For example, some countries require that the financial data of their citizens remain on servers physically located within their borders.
- Local Hosting: You may need to utilize localized cloud regions to stay compliant with “data residency” laws in specific nations.
- Cross-Border Transfers: Legal mechanisms like Standard Contractual Clauses (SCCs) are often required to move data between jurisdictions safely.
- Access Limitations: Even if data is stored centrally, your internal teams in one country might be legally barred from viewing the records of users in another.
3. Sanctions and AML across jurisdictions
International sanctions lists are constantly in flux as geopolitical situations evolve. Your system must be capable of screening against multiple global lists simultaneously to ensure you do not inadvertently facilitate a prohibited transaction.
- Global Watchlists: Automated systems must cross-reference OFAC (US), HM Treasury (UK), and EU lists in real-time.
- Secondary Sanctions: Even if a transaction is legal in your home country, it might still trigger penalties if it touches a person or entity sanctioned by the US.
- Conflict Resolution: In rare cases, two countries may have conflicting rules, requiring a pre-defined legal strategy to navigate the risk.
4. ISO 20022 in cross-border compliance
The transition to the ISO 20022 messaging standard is the single most important technical update for international payments. This format allows for much richer data, which makes it easier for foreign banks to verify the legitimacy of a payment.
- Enhanced Transparency: Including detailed information about the ultimate sender and receiver reduces the likelihood of funds being held up at intermediary banks.
- Reduced Friction: Standardized data fields mean fewer “repair” actions are needed when money moves through different global clearing systems.
- Rich Data Payloads: You can include purpose-of-payment codes and tax information directly within the payment message itself.
5. Global expansion and regulatory complexity
Scaling into new markets is a strategic move that requires a deep understanding of local licensing and consumer protection laws. Most successful platforms approach expansion in phases, mastering one regulatory environment before moving to the next.
- Passporting Rights: In some regions like the EU, a license in one country allows you to operate across the entire bloc with minimal extra paperwork.
- Localized Onboarding: You may need to adjust your KYC process to accept local identity documents that are unique to a specific country.
- Partner Networks: Working with local “correspondent” banks can help you navigate local rules without needing to secure a full banking license immediately.
Navigating these cross-border complexities requires a tech stack built on modularity and intelligence. By mastering international compliance, your platform becomes a bridge for global capital, making it an incredibly valuable asset for any serious investor.
What Features Should a Compliance-Ready System Have?
A truly compliant banking platform is defined by its ability to prove its integrity at any moment. Therefore, the features you build into the system should prioritize transparency and automated governance to ensure that every action is traceable and every risk is mitigated.
1. Immutable audit trails and event logging
Regulators look for a permanent record of everything that happens within your system. An immutable audit trail ensures that once a piece of data is written, it cannot be changed or deleted without leaving a clear mark.
- Timestamped Events: Every user login, transaction, and configuration change must be logged with a precise time and date.
- Cryptographic Hashing: Using advanced math to link log entries together makes it impossible to remove a single entry without breaking the entire chain.
- Storage Redundancy: Audit logs should be mirrored across multiple secure locations to prevent data loss during a system failure.
2. Role-based access and duty segregation
Security is strongest when no single person has total control over the platform. By assigning specific roles, you ensure that employees only access the data they need and that critical actions require multiple approvals.
- Granular Permissions: Different levels of access for customer support, compliance officers, and system administrators prevent accidental or malicious data exposure.
- The Four-Eyes Principle: High-risk tasks, such as approving a large wire transfer, should require at least two different people to authorize the action.
- Access Reviews: Regular checks ensure that employees who have changed roles or left the company no longer have active system permissions.
3. Screening engines and rule controls
Automated screening is the heart of real-time AML and sanctions compliance. These engines must be powerful enough to process thousands of names and transactions every second without causing delays for the user.
- Fuzzy Matching: This logic identifies potential hits even when names are misspelled or presented in different formats.
- Dynamic Rule Sets: You must be able to update your screening rules quickly as new sanctions lists are released by global authorities.
- Low Latency: The screening process should happen in the background so it does not slow down the user experience.
4. Case management and review workflows
When the system flags a potential issue, your compliance team needs a structured environment to investigate. A good case management tool turns a complex alert into a manageable task.
- Centralized Evidence: All relevant documents and transaction histories should be automatically gathered into a single view for the investigator.
- Step-by-Step Checklists: Guiding employees through a standardized review process ensures that nothing is missed during an investigation.
- Escalation Logic: High-priority cases should automatically move to senior staff to ensure they are handled with the necessary urgency.
5. Consent, retention, and policy enforcement
Managing user data requires a strict adherence to privacy laws and internal retention schedules. Consequently, the platform must automate the process of asking for consent and deleting data when it is no longer needed.
- Consent Tracking: Keep a clear record of exactly what the user agreed to when they signed up for your service.
- Automatic Purging: Set the system to permanently delete user data once the legal retention period has expired.
- Policy Versioning: Maintain copies of previous privacy policies so you can prove what rules were in place at any specific time in the past.
6. Vendor oversight and evidence repositories
Your compliance is only as strong as your weakest partner. A centralized repository for vendor documents helps you track the security certifications and audits of everyone you do business with.
- Document Tracking: Store SOC2 reports, ISO certifications, and insurance documents for every third-party API or cloud provider.
- Renewal Alerts: The system should notify you months in advance when a partner’s security certification is about to expire.
- Performance Logs: Track the uptime and security incidents of your vendors to ensure they are meeting their contractual obligations.
7. Reconciliation and exception handling
In banking, every cent must be accounted for. Automated reconciliation compares your internal records with the bank’s records to ensure they match perfectly.
- Real-time Balancing: The system should flag discrepancies as soon as they occur rather than waiting until the end of the day.
- Automated Patching: Some minor errors can be corrected by the system automatically, saving your team hours of manual work.
- Exception Queues: Any mismatch that the system cannot fix should be placed in a high-priority queue for immediate human review.
8. Incident response evidence preservation
If a security breach or a major system failure occurs, you must preserve the evidence for later forensic analysis. This documentation is vital for proving to regulators that you handled the crisis correctly.
- System Snapshots: Capture the exact state of your servers and databases at the moment an incident is detected.
- Communication Logs: Save all internal and external messages related to the incident response to prove you followed your own plan.
- Post-Mortem Reports: Use the preserved data to build a detailed report on the root cause and the steps taken to prevent a recurrence.
Investing in these features ensures that your banking platform is not just functional, but defensible. This level of technical maturity is a major differentiator that builds confidence with serious investors and long-term institutional partners.
How Intellivon Builds Compliance-Ready Platforms
Building a financial ecosystem requires a deep integration of regulatory logic into the very fabric of the architecture.
Intellivon follows a rigorous eight-step methodology to ensure that every platform we develop is ready for the scrutiny of global regulators and institutional investors.
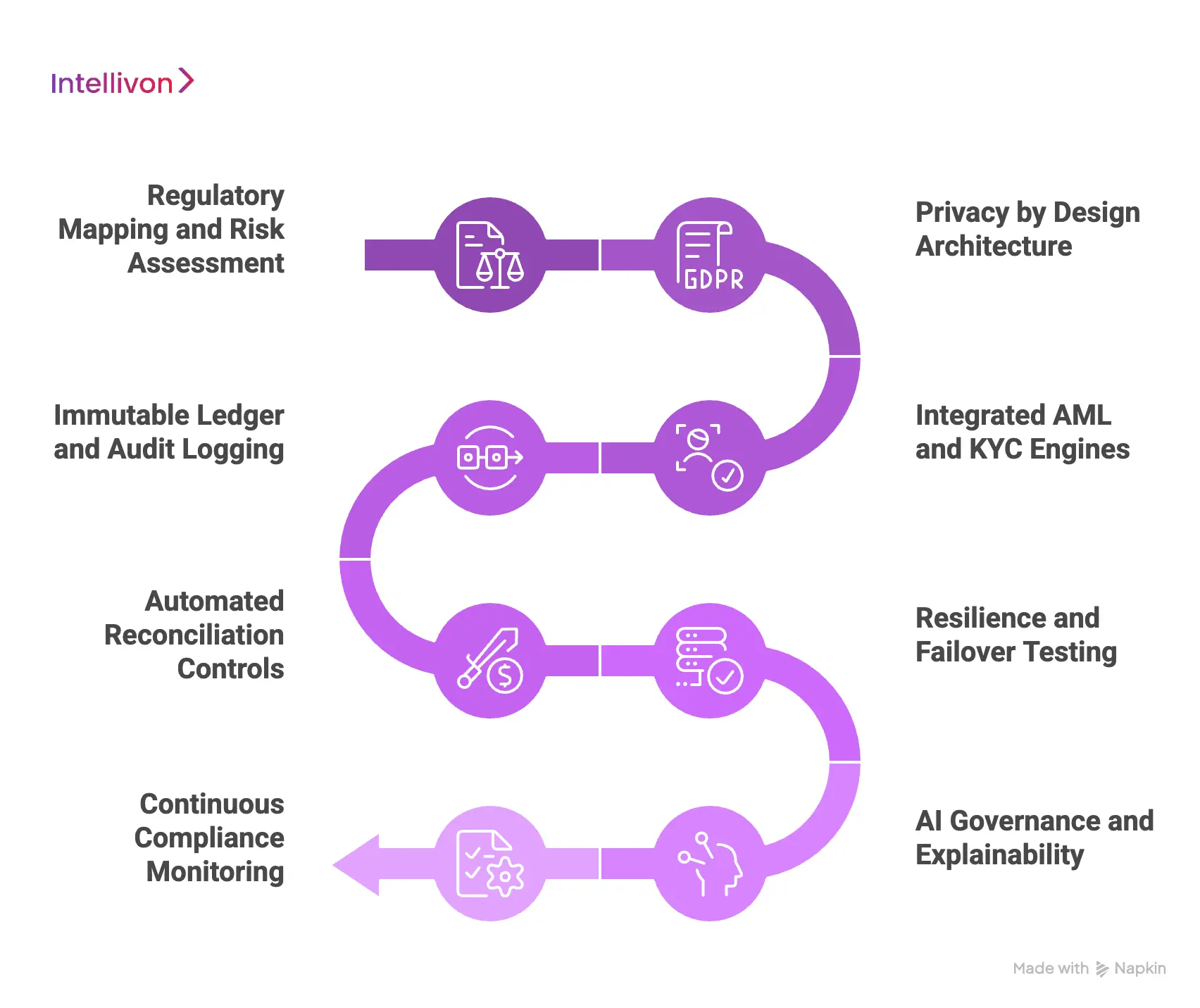
1. Regulatory Mapping and Risk Assessment
We begin by identifying every legal framework that applies to your specific business model and geographic target. This step ensures that we build only the necessary controls without bloating the system with irrelevant features.
- Jurisdictional Review: We analyze the overlap between US, EU, and local laws to create a unified compliance roadmap.
- Risk Profiling: Our team identifies potential “weak points” in your product flow, such as high-velocity transfers or anonymous onboarding.
- Baseline Requirements: We establish the minimum viable security and privacy standards needed to secure your banking license or partner bank approval.
2. Privacy by Design Architecture
We treat data privacy as a foundational requirement rather than an add-on. Therefore, we structure the database to ensure that sensitive user information is protected from day one.
- Data Segregation: We store personally identifiable information in isolated, encrypted vaults separate from transactional logs.
- Consent Management: Our systems include automated triggers that track user consent versions and manage data deletion requests.
- Access Control Mapping: We define specific user roles and permissions early in the design phase to prevent internal data leaks.
3. Integrated AML and KYC Engines
Intellivon builds automated verification flows that verify identities without slowing down the user experience. We integrate with top-tier data providers to ensure accuracy and speed.
| Component | Intellivon Implementation Strategy |
| KYC/KYB | Multi-layered document and biometric verification with UBO discovery. |
| Sanctions | Real-time screening against OFAC, UN, and EU lists via low-latency APIs. |
| Risk Scoring | Dynamic algorithms that update user profiles based on real-time behavior. |
4. Immutable Ledger and Audit Logging
Transparency is the key to passing a regulatory audit. We implement a non-negotiable logging system that records every event within the platform.
- Cryptographic Hashing: Every log entry is linked to the previous one, making it impossible to alter history without detection.
- Comprehensive Tracking: We log everything from administrative setting changes to individual API calls.
- Offline Backups: Logs are mirrored to secure, read-only environments to prevent tampering during a security incident.
5. Automated Reconciliation Controls
To protect the integrity of your capital, we build systems that constantly cross-reference your internal data with external bank records.
- Daily Matching: Our logic compares your platform’s ledger to your sponsor bank’s records every 24 hours.
- Discrepancy Alerts: The system flags any mismatch, even by a single cent, for immediate human review.
- Exception Management: We build dedicated workflows for compliance teams to investigate and resolve reconciliation errors quickly.
6. Resilience and Failover Testing
We ensure your platform can survive systemic shocks and technical failures. This proactive approach satisfies the rigorous demands of DORA and other operational resilience mandates.
- Geographic Redundancy: We deploy your infrastructure across multiple cloud regions to ensure 99.99% uptime.
- Chaos Testing: Our engineers intentionally simulate system failures to verify that failover mechanisms work as intended.
- Incident Playbooks: We provide pre-written response plans that your team can execute during a crisis.
7. AI Governance and Explainability
When we deploy AI for fraud detection or credit scoring, we ensure the logic is never a “black box.” We build transparency into every algorithm to satisfy regulatory examiners.
- Model Validation: We conduct extensive backtesting to ensure the AI behaves predictably before it touches live funds.
- Bias Detection: Our team runs regular audits to ensure the AI is not making discriminatory decisions.
- Reasoning Logs: The system generates a plain-language explanation for every automated rejection or alert.
8. Continuous Compliance Monitoring
Regulatory standards change constantly, so our work doesn’t end at launch. We build tools that allow you to monitor your compliance health in real-time.
- Compliance Dashboards: We provide a “single pane of glass” view for your COOs and compliance officers to track AML alerts and system uptime.
- Automated Reporting: The platform generates regulator-ready documents with the click of a button.
- Update Loops: We design the system with a modular architecture, allowing us to push updates for new laws without taking the platform offline.
By following this comprehensive strategy, Intellivon transforms compliance from a hurdle into a strategic moat. We build the technical foundation that allows you to scale confidently while maintaining the trust of your investors and the safety of your users.
Conclusion
Compliance is no longer a peripheral concern but a core engine for financial growth. A system built with deep regulatory integrity attracts higher-tier investors and ensures long-term operational survival in a volatile market.
By prioritizing auditability, resilience, and automated governance, you transform technical requirements into a powerful strategic moat. Secure your future by building a platform that turns every regulatory mandate into a foundation for institutional trust.
Build Compliance-Ready Banking Platforms With Intellivon
Building an enterprise banking system is not just about launching faster or adding more features. It is about creating a platform that can operate within strict regulatory expectations, satisfy bank partners, support audits, and scale without exposing the business to avoidable compliance risk.
At Intellivon, we build enterprise banking platforms with compliance embedded into the architecture from the start. Our approach focuses on turning regulatory complexity into clear system design, so your platform is easier to launch, easier to defend, and easier to scale.
A. Embedding Compliance Into Core Platform Architecture
Compliance becomes expensive when it is treated as an afterthought.
We design banking systems where auditability, access control, monitoring, and recordkeeping are built into the platform foundation from day one.
- Audit trails are designed for reviews, investigations, and control validation
- Role-based access controls with approval and segregation logic
- Event logging across onboarding, payments, and account activity
- Data structures that support retention, reporting, and traceability
This helps you avoid costly rework later and creates a stronger base for growth.
B. Building AML, KYC, and Monitoring Workflows Into Operations
Banking compliance depends on how operational workflows actually function.
We build systems that support identity checks, business verification, screening, transaction monitoring, and review workflows in a way that fits real enterprise operations.
- KYC and KYB workflows aligned with onboarding requirements
- Sanctions, PEP, and watchlist screening integrations
- Transaction monitoring logic with alert and case flows
- Review queues and escalation paths for compliance teams
This allows your team to manage compliance through the product, not outside of it.
C. Preparing Platforms for Bank and Enterprise Due Diligence
Strong compliance posture matters long before regulators get involved.
Enterprise buyers, sponsor banks, and financial partners all want proof that the platform has been designed with control maturity in mind. We help build systems that stand up to that scrutiny.
- Architecture aligned with security and control expectations
- Support for vendor reviews and due diligence discussions
- Clear evidence trails for approvals, changes, and incidents
- Platform logic built for accountability across teams and partners
This makes your platform more credible in high-stakes sales and partnership conversations.
D. Supporting Privacy, Security, and Resilience by Design
Modern banking platforms must do more than process transactions. They must protect data, handle incidents properly, and operate reliably under pressure.
We design systems that support privacy requirements, security controls, and resilience planning without fragmenting the user or operations experience.
- Encryption, access control, and data protection layers
- Retention and deletion logic aligned with policy needs
- Incident response support and evidence preservation
- Recovery, failover, and operational resilience planning
This helps you build a banking platform that is dependable in both day-to-day operations and high-risk situations.
E. Scaling Compliance Across Products, Partners, and Regions
Compliance complexity grows quickly as platforms expand.
Whether you are adding new workflows, entering new markets, or working with more partners, the platform needs a structure that can support change without breaking control integrity.
- Modular compliance logic that supports product expansion
- Shared control frameworks across teams and workflows
- Support for cross-border regulatory requirements
- Architecture that scales without weakening oversight
This gives you a more practical path to scale while maintaining control.
Enterprise banking platforms succeed when compliance is treated as part of the system, not a layer added later. Intellivon helps organizations build banking infrastructure that supports regulatory readiness, operational clarity, and long-term growth.
Planning a compliance-ready banking platform? Connect with Intellivon to discuss your requirements and get a tailored project estimate.
FAQs
Q1. Is KYC the same as KYB for enterprise banking clients, or do B2B onboarding compliance rules work differently?
A1. KYB is significantly more complex than KYC. While KYC verifies an individual, KYB requires identifying the Ultimate Beneficial Ownership of a corporation. You must peel back corporate layers to verify entities and owners against sanctions lists, ensuring no illicit actors control the business or its capital flows.
Q2. How often does a BSA/AML program need to be independently audited for a fintech without a traditional compliance team?
A2. Most regulators and sponsor banks require an independent BSA/AML audit every 12 to 18 months. Even without a large internal team, you must prove that your automated systems effectively flag suspicious activity. Regular testing ensures your risk thresholds remain appropriate for your transaction volume and user base.
Q3. What compliance documentation does a bank require before approving us as a fintech vendor, and in what order?
A3. Banks typically follow a “Security-First” sequence. First, they require SOC2 Type II reports and your written Information Security Program. Next, they review your AML/BSA policy and KYC workflows. Finally, they inspect your business continuity plans and insurance certificates to ensure you are a low-risk partner.
Q4. How do open banking APIs under PSD2 interact with GDPR consent, and what happens to data already shared?
A4. Customers can revoke consent at any time. Under GDPR, once a user withdraws access, the API must immediately stop fetching new data. However, data already shared for a completed transaction is often retained for a period to meet financial record-keeping laws and anti-fraud requirements.
Q5. Does DORA apply to US fintech platforms that serve European banking clients?
A5. Yes, DORA applies to any entity providing critical ICT services to EU financial institutions. You must build robust incident reporting tools and conduct regular resilience testing. Your system must also maintain a register of all third-party cloud and API providers to ensure total supply-chain transparency.
Q6. Which states require a Money Transmitter License, and is there a way to avoid 50-state licensing via a BaaS bank partnership?
A6. Nearly every US state requires an MTL for handling third-party funds. You can often bypass individual state licensing by partnering with a chartered bank through a BaaS model. In this setup, you operate as a “service provider” under the bank’s existing regulatory umbrella and license.
Q7. How does ISO 20022 messaging compliance affect cross-border enterprise payment systems in 2025?
A7. ISO 20022 replaces legacy formats with structured, data-rich XML messages. This allows for better transparency during international transfers. Systems must be updated to handle these larger data payloads, which reduces “false positives” in AML screening and ensures faster clearing across different global banking networks.